It has been a busy few weeks since we previewed the new Secure Score API. While the team was working on this, they also were working on another common request, support for additional controls. In particular we heard that you wanted controls from the Enterprise Mobility + Security (EMS) suite. As you might have seen in the Microsoft Secure Blog we are expanding Secure Score to support additional EMS solutions and are happy to share that we have new controls for Microsoft Cloud App Security and additional controls for Azure Active Directory (Azure AD).
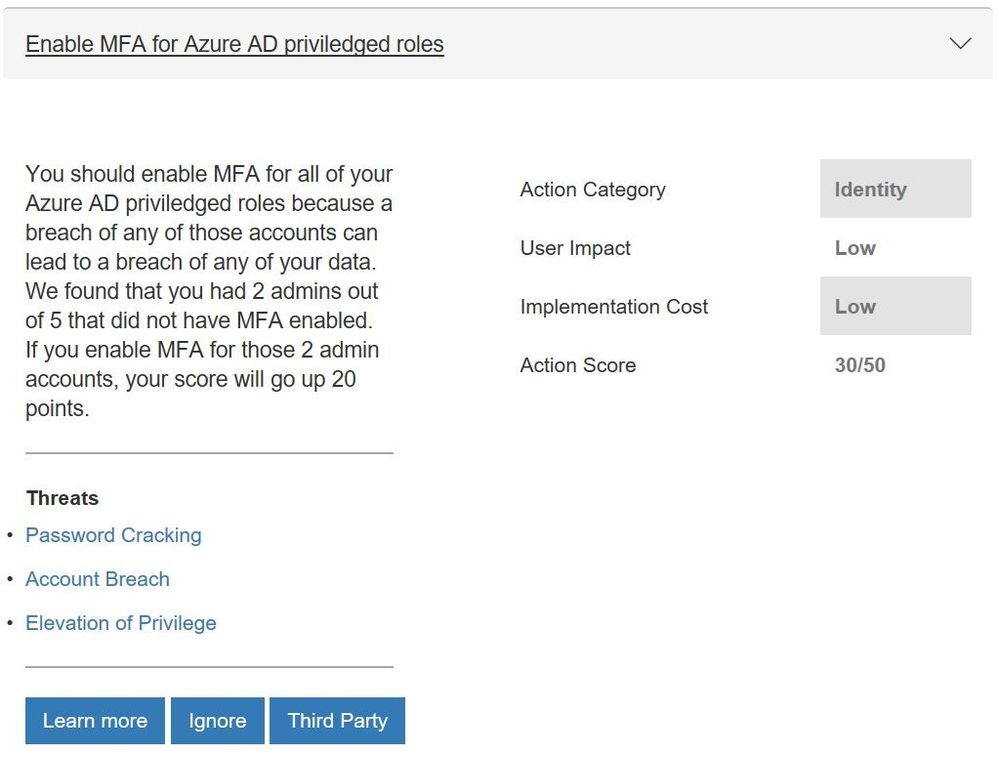
Azure AD Controls
We have seen the feedback from many of you that you wanted support for additional Azure Active Directory (Azure AD) controls to help you manage user identities and create intelligence-driven access policies to secure your resources. In particular you wanted the multifactor authentication (MFA) controls to support conditional access. Working with the Azure AD team this is now available and 8 more controls which include:
- Enabling self-service password reset that helps empower users and reduce help desk costs
- Require just in time access for global administrators using Privileged Identity Management
- Turning on password hash sync which helps you leverage the same password you use to sign in to your on-premises Active Directory for Azure AD services
- Enable user risk policies that can block access or require a user to use MFA to login in when there is a likelihood that a user’s identity has been compromised
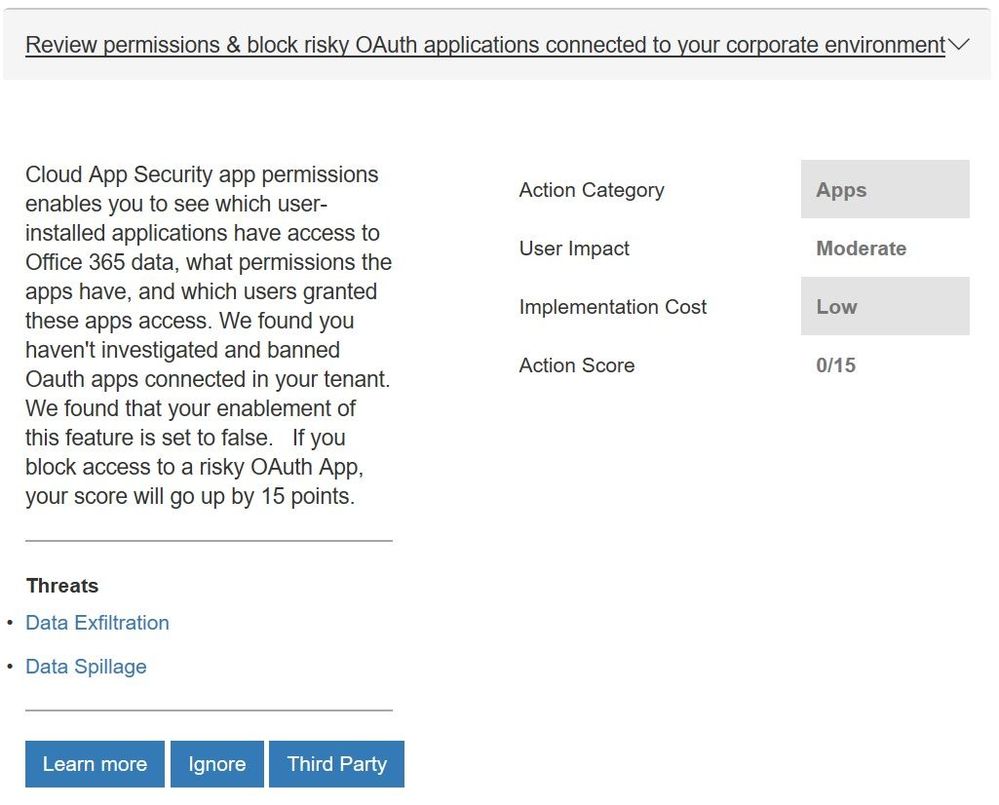
Microsoft Cloud App Security Controls
More and more organizations are adopting SaaS apps, not only to reduce costs but also to unlock competitive advantages such as faster time to market and improved collaboration. Even if your company hasn’t embraced cloud applications, your employees are probably using them. Microsoft Cloud App Security is our cloud access security broker that gives you visibility into your cloud apps and services, provides sophisticated analytics to identify and combat cyberthreats and enables you to control how your data travels. If you are taking advantage of the solution, you will now get points for actions like:
- Reviewing permissions and blocking risky OAuth applications that your users have installed and have access to Office 365 data
- Reviewing anomaly detection policies that help you understand if users are logging in from locations that they normally don’t log in from, using anonymous IP addresses, and have multiple failed login attempts
- Discover risky and non-compliant Shadow IT applications used in your organization through the Cloud Discovery Dashboard and automatic uploading of your firewall/proxy logs
- Creating custom activity policies to discover risky behavior in cloud apps like a mass downloads of data.
We will be looking to add more controls in the future. For example, we will look to add controls from Azure Security Center as they have launched a public preview of their own score.
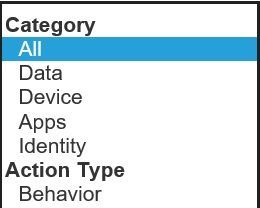
With all the new controls we are rethinking how we show the points you have obtained. Today we display the overall Microsoft Secure Score and the points by solution (Office 365 and Windows). With the addition of controls from EMS and eventually Azure Security Center, along with the fact that organizations have told us that they think about their environment more broadly then just solutions, this approach will be less effective in helping you understand your security posture. To help solve this, in the future we will move to a category view that will show a score for controls that focus on identity, apps, data, devices, and infrastructure. You can see the beginnings of this change in the filter box within the “Take Action, Improve Your Microsoft Secure Score” section of Secure Score.
To see what your score looks like with the new controls, login with administrative credentials at https://securescore.microsoft.com and start thinking about which ones you will enable. We hope that these changes help you get even greater visibility into your security posture and the guidance to help you find the right level of security for your organization.
As always, feel free to leave your questions, thoughts, and comments below.