Azure ATP investigation of brute force and account enumeration attacks made over the NTLM protocol
Security research shows most successful enumeration and brute force attacks use either NTLM or Kerberos authentication protocols for entry. In fact, they’re the most popular discovery-phase attacks Azure ATP observed in the past 12 months. ...
Latest SharePoint Dev Weekly – Episode 66
In this session of SharePoint Dev Weekly, hosts – Vesa Juvonen (Microsoft), Waldek Mastykarz (Rencore), and typically a special guest from the SharePoint PnP Community, discuss the latest news and topics around SharePoint development....
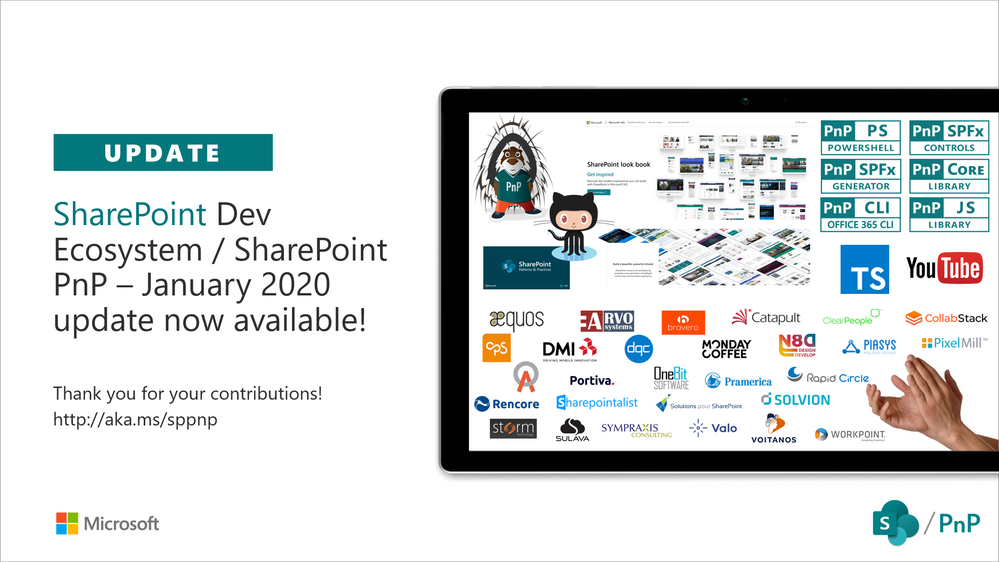
SharePoint Development Community (PnP) – January 2020 update
Latest monthly summary of SharePoint Development guidance for SharePoint Online and on-premises is now available from the SharePoint Dev Blog. Check the latest news, samples and other guidance from this summary. SharePoint Dev Ecosystem / SharePoint PnP...
Latest SharePoint Dev Weekly – Episode 65
In this session of SharePoint Dev Weekly, hosts – Vesa Juvonen (Microsoft), Waldek Mastykarz (Rencore), discuss the latest news and topics around SharePoint development. In addition to drawing attention to the latest advancements being...
Securing ALL your cloud apps with Microsoft
For most customers, cloud apps run the workplace. While we see an average of 129 IT-managed applications, Discovery data from our Cloud Access Security Broker (CASB) shows that the total number of apps accessed by employees in large organizations often exceeds 1,000....
Securing ALL your cloud apps with Microsoft
This post is authored by @Boris_Kacevich For most customers, cloud apps run the workplace. While we see an average of 129 IT-managed applications, Discovery data from our Cloud Access Security Broker (CASB) shows that the total number of apps...
SharePoint Dev Weekly – Episode 64
In this session of SharePoint Dev Weekly, hosts – Vesa Juvonen (Microsoft), Waldek Mastykarz (Rencore), discuss the latest news and topics around SharePoint development. Vesa and Waldek are joined by Thomas...
Announcing Updates to the M365 Attack Simulator
Overview The Microsoft 365 Attack Simulation team is pleased to announce the release of several new features in our phish simulation tool. This includes: an attachment-based phishing attack the ability to filter your simulation user targets by directory metadata like...
Announcing Updates to the M365 Attack Simulator
Overview The Microsoft 365 Attack Simulation team is pleased to announce the release of several new features in our phish simulation tool. This includes: an attachment-based phishing attack the ability to filter your simulation user targets by directory metadata like...