Automate cybersecurity at scale with Microsoft Security Copilot agents
This post was originally published on this site.
When we introduced Microsoft Security Copilot last year, we set out to transform the way defenders approach cybersecurity. As one of the industry’s first generative AI solutions for security and IT teams, Security Copilot is empowering teams to catch what others miss, respond faster, and strengthen team expertise in an evolving threat landscape.
Customers like Eastman are already seeing the impact. “I’m finding that I can ask [Security Copilot] about attack factors that I’ve never seen before and get answers much faster”, said David Yates, Senior Cybersecurity Analyst at Eastman. “That helps me to make a better decision and respond faster to an attacker.” A recent study of Copilot users showed that using Security Copilot reduced mean time to resolution by 30%, helping accelerate response times and minimizing the impact of security incidents.
But as defenders evolve, so have attackers.
Adversaries are now leveraging AI to launch more sophisticated attacks with unprecedented speed and scale. Security and IT teams – already overwhelmed by a huge volume of alerts, data, and threats – are struggling to keep up. Traditional automation, while useful, lacks the flexibility and adaptability to keep up.
Today, we’re taking the next leap forward in generative AI-powered cybersecurity. I am thrilled to introduce agents in Microsoft Security Copilot.
AI-powered agents represent the natural evolution of Security Copilot, going beyond AI assistant capabilities. They autonomously manage high-volume security and IT tasks, seamlessly integrated with Microsoft Security solutions and partner solutions. Purpose-built for security, these agents learn from feedback, adapt to organizational workflows with your team fully in-control, and operate securely within Microsoft’s Zero-Trust framework.
Delivering powerful automation across threat protection, identity management, data security, and IT operations, these agents empower teams to accelerate responses, prioritize risks, and drive efficiency at scale. By reducing manual workloads, they enhance operational effectiveness and strengthen overall security posture – allowing defenders to stay ahead. To bring this automation to life, we’re introducing six security agents from Microsoft and five security agents from partners which will be available for preview in April.
Empowering security and IT teams with Security Copilot agents
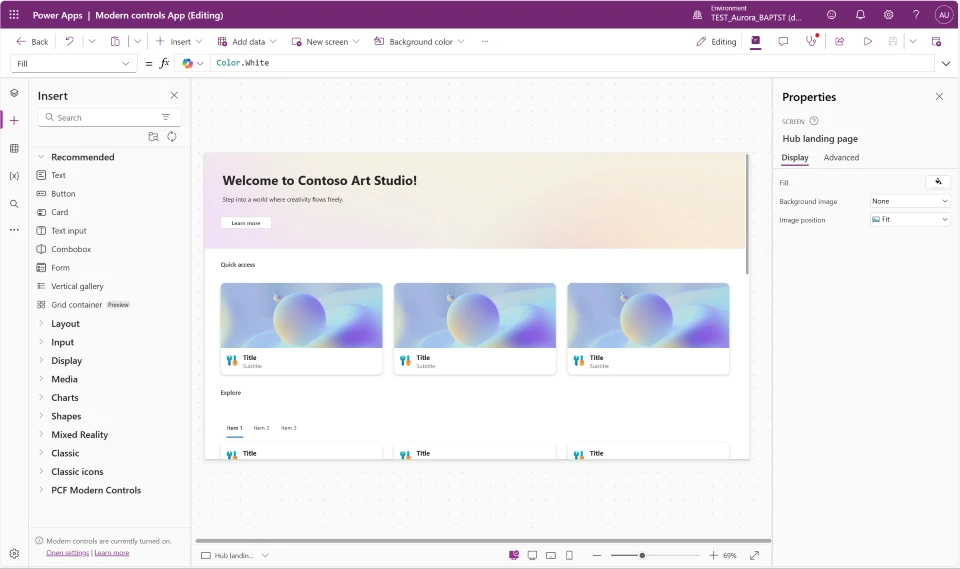
Our goal is to provide generative AI-powered security for everyone. Integrating Copilot with Microsoft Security products helps IT and security teams benefit from increased speed and accuracy. Now, you can use embedded Security Copilot agents with capabilities specific to use cases for your role in the products you know and love:
Security Alert Triage Agent (previously named Phishing Triage Agent)
SOC analysts often face the challenge of managing hundreds of user-submitted phishing alerts each week, with each alert taking up to 30 minutes for manual triage. This process requires meticulous sifting through submissions to find the needle in the haystack – the genuine threat amidst all the noise. Security Copilot solves this challenge with an AI-powered agent embedded in Microsoft Defender, that works in the background to autonomously triage user-submitted phishing incidents. Powered by advanced multi-modal AI tools, it determines whether an alert is a genuine phishing attempt or a false alarm with exceptional precision. The agent not only delivers natural language explanations for its decisions but also dynamically refines its detection capabilities based on analyst feedback. By alleviating the burden of reactive work, it empowers SOC analysts to focus on proactive security measures, ultimately strengthening the organization’s overall security posture.
Note: The Phishing Triage Agent has since been expanded and is now called the Security Alert Triage Agent. Learn more at aka.ms/SATA
Alert Triage Agents for Data Loss Prevention and Insider Risk Management
Data security admins regularly struggle to manage the volume of alerts they receive daily, addressing only about 60% of them due to time and resource constraints1. The Alert Triage Agents in Microsoft Purview Data Loss Prevention (DLP) and Insider Risk Management (IRM) identify the alerts that pose the greatest risk to your organization and should be prioritized first. These agents analyze the content and potential intent involved in an alert, based on the organization’s chosen parameters and selected policies, to categorize alerts based on the impact they have on sensitive data. Additionally, they provide a comprehensive explanation on the logic behind that categorization, allowing admins to analyze a risk in just a few minutes. These agents empower data security teams to focus on the most important alerts and concentrate on the critical threats, with a dynamic process that takes inputs from data security admins in natural language and fine-tunes the triage results to better match the organizations’ priorities. The agent learns from this feedback, using that rationale to calibrate the prioritization of future alerts in DLP and IRM. Learn more about the Alert Triage Agents for DLP and IRM here.
Conditional Access Optimization Agent
As organizations grow, identity and IT admins must continuously ensure that access policies adapt to new employees, contractors, SaaS apps, and more – keeping security intact without adding complexity. But as their environments evolve, keeping Conditional Access (CA) policies up to date becomes increasingly difficult. New users and apps can slip through, and exclusions can go unaddressed, creating security risks. Even with routine reviews, manually auditing policies and adjusting coverage can take days or weeks –yet gaps can still go unnoticed. The CA Optimization Agent in Microsoft Entra changes that for admins, automating the detection and resolution of policy drift. This agent continuously monitors for newly created users and applications, analyzing their alignment with existing CA policies, and proactively detects security gaps in real time. Unlike static automation, it recommends optimizations and provides one-click fixes, helping admins refine policy coverage effortlessly while ensuring a strong, adaptive security posture. Learn more about the CA Optimization Agent here.
Vulnerability Remediation Agent
Managing security vulnerabilities is a growing challenge for organizations, as the volume of CVEs and limited resources make it difficult to prioritize and implement critical fixes effectively. Microsoft Intune is designed for organizations that need a modern, cloud-powered approach to endpoint management, one that not only simplifies IT operations but strengthens security in an evolving threat landscape. IT admins require more than just visibility into vulnerabilities; they need a proactive, risk-based security strategy that continuously assesses risk and automates remediation to minimize exposure. That’s why Intune is introducing the Vulnerability Remediation Agent—a solution built to help organizations stay ahead of emerging threats.
By leveraging Microsoft Defender Vulnerability Management, the agent automatically identifies, evaluates, and prioritizes vulnerabilities. It continuously monitors newly published threats, assesses their risk levels, and offers clear, actionable recommendations for remediation. With continuous vulnerability detection, risk-based prioritization and guided remediation, the agent reduces exposure time while freeing up IT teams to focus on strategic initiatives. This is the first step toward designing vulnerability remediation at scale. A future, comprehensive approach will work across device platforms, address vulnerabilities in third-party applications, and remediate using configuration changes. Learn more about the Vulnerability Remediation Agent here.
Threat Intelligence Briefing Agent
Cyber Threat Intelligence analysts often face data overload and resource constraints when sourcing the threat intelligence needed to help their organizations understand, prioritize, and respond to critical threats. Crafting a threat intelligence briefing for security teams and executives can take hours—or even days—due to the constant evolution of both the threat landscape and an organization’s attack surface.
The Threat Intelligence Briefing Agent in Security Copilot dramatically expedites this process. It automatically curates up-to-date, context-specific intelligence tailored to your organization’s unique profile and attack surface. Operating autonomously in the background, it taps into Microsoft’s extensive threat intelligence resources (including Microsoft Defender Threat Intelligence and Microsoft Defender External Surface Management) to deliver prioritized reports in just 4-5 minutes. This tool not only cuts down on manual effort but also highlights the most pressing threats and provides actionable recommendations, ensuring your team stays well-informed and ready to respond. Learn more about the Threat Intelligence Briefing Agent here.
Extending agentic capabilities with partner solutions
We are grateful to our partners who continue to play a vital role in empowering everyone to confidently adopt safe and responsible AI. Our growing partner ecosystem seamlessly integrates Security Copilot with established tools across various applications. Today, I am pleased to share five new upcoming agents in partner solutions, with many more to come.
- Privacy Breach Response Agent by OneTrust analyzes a data breach based on type of data, geographic jurisdiction, and regulatory requirements to generate guidance for the privacy team on how to meet those requirements.
- Network Supervisor Agent by Aviatrix determines why a VPN, Gateway, or Site2Cloud connection is down and provides information about the failure.
- SecOps Tooling Agent by BlueVoyant assesses your security operations center (SOC) and state of controls to make recommendations to optimize security operations to improve controls, efficacy, and compliance.
- Alert Triage Agent by Tanium provides analysts with necessary context to quickly and confidently make a decision on each alert.
- Task Optimizer Agent by Fletch helps organizations forecast and prioritize the most critical threat alerts to reduce alert fatigue and improve security.
Learn more about our partner integrations at aka.ms/partnerintegrations.
Get Started with Security Copilot Agents
Microsoft Security Copilot agents will be available in preview starting April 2025. To get started with Security Copilot, check out the website for more information. Already using Security Copilot? Make sure you’re signed up for the Security Copilot Customer Connection Program (CCP) to receive the latest updates and features—join today at aka.ms/JoinCCP. Learn more about the latest innovations at the Microsoft Secure digital event on April 9, 2025. Register now.
With agents, Security Copilot continues to lead the way in AI-powered cybersecurity, helping organizations defend against threats faster, smarter, and with greater confidence.