Overview
MFA enablement completely changes an organization’s security posture. Even though MFA does not necessarily provide perfect security, it does make it significantly more challenging to breach accounts and perhaps enough to encourage the attacker to seek out an easier target instead. This statement is not a presumption; during the 2017 Black Hat conference, multi-factor authentication and encryption were the 2 biggest named obstacles surveyed from hackers. Organizations recognize the benefits of MFA but we’ve received feedback about usability challenges in Exchange administration scenarios. This post identifies the popular administration workflows and will reference tools to fulfill them in accounts with MFA enforced.
To help increase the security of administrator accounts, you should enable MFA for your administrative accounts. For instructions on how to turn on MFA for Office 365 accounts, see this article. The workflow for users to set up MFA on their accounts is laid out in this document.
Exchange Online Administration Tools
Depending on the organization, Exchange Online is administrated through several different interfaces. The Office 365 customer base is incredibly diverse with larger tenants relying on automation to service their users while less complex organizations administrate the service from the portals.
Automation
Automation of Exchange administration is exposed primarily through remote PowerShell cmdlets. Many administrators use standard Windows PowerShell to connect to a remote Exchange server but if the account has MFA enabled, you need to install a separate Exchange Online PowerShell module based on the instructions in this document.
Follow the instructions here to connect to Exchange Online PowerShell with MFA. You can run scripts from this client or interact directly with Exchange. Some organizations create custom interactive scripts which provides a more admin friendly and less error prone interface for common administrative tasks on the tenant.
Portals
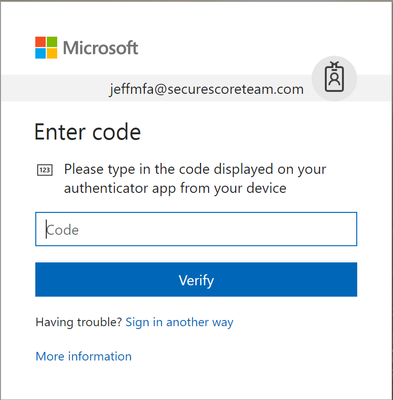
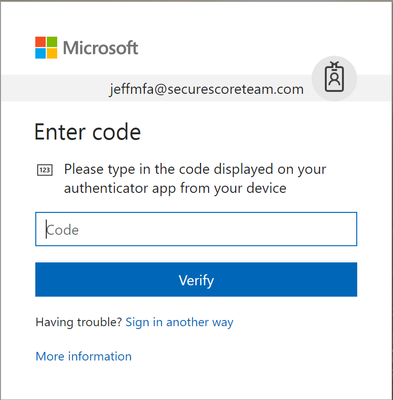
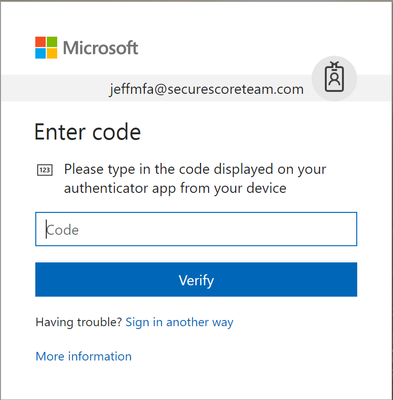
Office 365 provides portals to administrate Exchange Online, such as the Admin center, Security & Compliance Center and Exchange admin center. When MFA is enabled, you will be prompted for an authentication code.
Other Administration Workflows
Scheduled Automation
One of the main reasons organizations need to periodically run scripts on their tenant is for compliance/reporting requirements to scan the states of various assets. Some organizations have established procedures for employees to run a set of scripts as a part of their weekly/monthly responsibilities.
Some admins set up scheduled PowerShell tasks to delegate the responsibility of running this script to a machine. Of course, since the objective is to run these scripts without human intervention, MFA is not possible and will need to be turned off on these accounts. In order to authenticate into the service, administrators will still need to submit their credentials. Credentials should never be stored in plaintext. Instead, use the commands below to encode your password. You can only decode the password on the same computer with the same user account.
$AdminCred = Get-Credential
$AdminCred.Password | ConvertFrom-SecureString | Out-File C:AdminCred.txt
To submit this password in your scripts use the commands below. Replace “AdminUsername” with your account username.
$password = Get-Content C:AdminCred.txt | ConvertTo-SecureString
$Credentials = New-Object -typename System.Management.Automation.PSCredential -ArgumentList "AdminUsername",$password
Connect-EXOPSSession -Credential $AdminCred
Import-PSSession $ExoSession
Since this does still register a risk if an adversary breaches your computer, you should take the following precautions on the machine with the scheduled task:
- Tightly control access to the machine and disable Remote Desktop Protocol (RDP)
- Limit the use of the account to only administrative activities (disable mail or use an alt account)
- Set strong passwords
- Enable unified audit log and mailbox auditing
- Periodically review the audit logs for this account for signs of compromise
- Confine admin activities to within your network perimeter
- Constrain cmdlets permissions as tightly as possible to the account through role management
Exchange Role Management
You can limit the permissions of administrative accounts using role groups to ensure that even if the account does get breached, the actions that the attacker can take are limited to the administration responsibilities of the account. Details on how to manage role assignments are in this article.
Long-running Scripts
When running long scripts from the standard Windows PowerShell client, administrators have faced session timeouts. Typically, the solution is to wrap the script with a loop that checks for session timeouts and recover by submitting saved credentials to re-establish the session. Now, how would you do this without human intervention for MFA accounts which require a second method of authentication?
Fortunately, the Exchange Online PowerShell Module takes care of session timeouts by re-establishing the session automatically. NOTE: it is important to use the UserPrincipalName parameter to connect so that the client can automatically re-establish the session for you.
Connect-EXOPSSession –UserPrincipalName joe@contoso.com
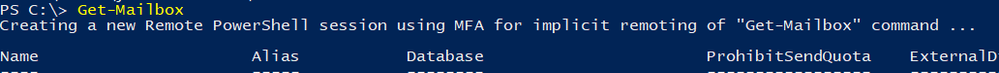
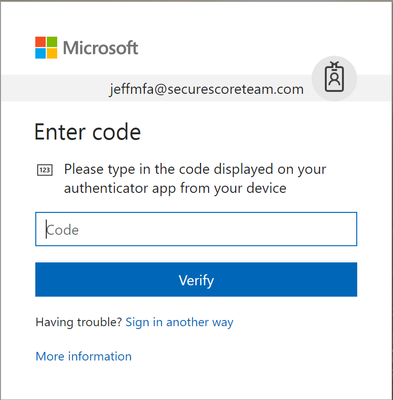
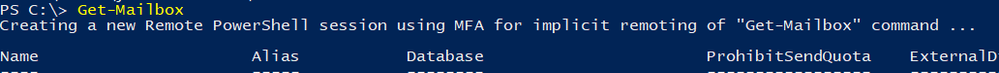
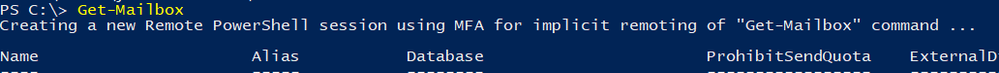
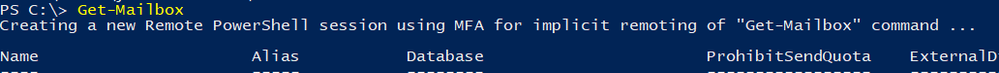
See below, the original PowerShell session has expired before I ran the Get-mailbox command. The client recognizes that the session has expired and automatically creates a new session without prompting for credentials.
General Secure Administration Recommendations
Beyond using MFA for Exchange administration, Microsoft recommends that you also take a broader look at your security. Below are some great solutions and ideas to help protect administrator accounts:
We hope this post has helped create a more secure and usability friendly administration story for you. Leave us a comment below with feedback!
Overview
MFA enablement completely changes an organization’s security posture. Even though MFA does not necessarily provide perfect security, it does make it significantly more challenging to breach accounts and perhaps enough to encourage the attacker to seek out an easier target instead. This statement is not a presumption; during the 2017 Black Hat conference, multi-factor authentication and encryption were the 2 biggest named obstacles surveyed from hackers. Organizations recognize the benefits of MFA but we’ve received feedback about usability challenges in Exchange administration scenarios. This post identifies the popular administration workflows and will reference tools to fulfill them in accounts with MFA enforced.
To help increase the security of administrator accounts, you should enable MFA for your administrative accounts. For instructions on how to turn on MFA for Office 365 accounts, see this article. The workflow for users to set up MFA on their accounts is laid out in this document.
Exchange Online Administration Tools
Depending on the organization, Exchange Online is administrated through several different interfaces. The Office 365 customer base is incredibly diverse with larger tenants relying on automation to service their users while less complex organizations administrate the service from the portals.
Automation
Automation of Exchange administration is exposed primarily through remote PowerShell cmdlets. Many administrators use standard Windows PowerShell to connect to a remote Exchange server but if the account has MFA enabled, you need to install a separate Exchange Online PowerShell module based on the instructions in this document.
Follow the instructions here to connect to Exchange Online PowerShell with MFA. You can run scripts from this client or interact directly with Exchange. Some organizations create custom interactive scripts which provides a more admin friendly and less error prone interface for common administrative tasks on the tenant.
Portals
Office 365 provides portals to administrate Exchange Online, such as the Admin center, Security & Compliance Center and Exchange admin center. When MFA is enabled, you will be prompted for an authentication code.
Other Administration Workflows
Scheduled Automation
One of the main reasons organizations need to periodically run scripts on their tenant is for compliance/reporting requirements to scan the states of various assets. Some organizations have established procedures for employees to run a set of scripts as a part of their weekly/monthly responsibilities.
Some admins set up scheduled PowerShell tasks to delegate the responsibility of running this script to a machine. Of course, since the objective is to run these scripts without human intervention, MFA is not possible and will need to be turned off on these accounts. In order to authenticate into the service, administrators will still need to submit their credentials. Credentials should never be stored in plaintext. Instead, use the commands below to encode your password. You can only decode the password on the same computer with the same user account.
$AdminCred = Get-Credential
$AdminCred.Password | ConvertFrom-SecureString | Out-File C:AdminCred.txt
To submit this password in your scripts use the commands below. Replace “AdminUsername” with your account username.
$password = Get-Content C:AdminCred.txt | ConvertTo-SecureString
$Credentials = New-Object -typename System.Management.Automation.PSCredential -ArgumentList "AdminUsername",$password
Connect-EXOPSSession -Credential $AdminCred
Import-PSSession $ExoSession
Since this does still register a risk if an adversary breaches your computer, you should take the following precautions on the machine with the scheduled task:
- Tightly control access to the machine and disable Remote Desktop Protocol (RDP)
- Limit the use of the account to only administrative activities (disable mail or use an alt account)
- Set strong passwords
- Enable unified audit log and mailbox auditing
- Periodically review the audit logs for this account for signs of compromise
- Confine admin activities to within your network perimeter
- Constrain cmdlets permissions as tightly as possible to the account through role management
Exchange Role Management
You can limit the permissions of administrative accounts using role groups to ensure that even if the account does get breached, the actions that the attacker can take are limited to the administration responsibilities of the account. Details on how to manage role assignments are in this article.
Long-running Scripts
When running long scripts from the standard Windows PowerShell client, administrators have faced session timeouts. Typically, the solution is to wrap the script with a loop that checks for session timeouts and recover by submitting saved credentials to re-establish the session. Now, how would you do this without human intervention for MFA accounts which require a second method of authentication?
Fortunately, the Exchange Online PowerShell Module takes care of session timeouts by re-establishing the session automatically. NOTE: it is important to use the UserPrincipalName parameter to connect so that the client can automatically re-establish the session for you.
Connect-EXOPSSession –UserPrincipalName joe@contoso.com
See below, the original PowerShell session has expired before I ran the Get-mailbox command. The client recognizes that the session has expired and automatically creates a new session without prompting for credentials.
General Secure Administration Recommendations
Beyond using MFA for Exchange administration, Microsoft recommends that you also take a broader look at your security. Below are some great solutions and ideas to help protect administrator accounts:
We hope this post has helped create a more secure and usability friendly administration story for you. Leave us a comment below with feedback!
Overview
MFA enablement completely changes an organization’s security posture. Even though MFA does not necessarily provide perfect security, it does make it significantly more challenging to breach accounts and perhaps enough to encourage the attacker to seek out an easier target instead. This statement is not a presumption; during the 2017 Black Hat conference, multi-factor authentication and encryption were the 2 biggest named obstacles surveyed from hackers. Organizations recognize the benefits of MFA but we’ve received feedback about usability challenges in Exchange administration scenarios. This post identifies the popular administration workflows and will reference tools to fulfill them in accounts with MFA enforced.
To help increase the security of administrator accounts, you should enable MFA for your administrative accounts. For instructions on how to turn on MFA for Office 365 accounts, see this article. The workflow for users to set up MFA on their accounts is laid out in this document.
Exchange Online Administration Tools
Depending on the organization, Exchange Online is administrated through several different interfaces. The Office 365 customer base is incredibly diverse with larger tenants relying on automation to service their users while less complex organizations administrate the service from the portals.
Automation
Automation of Exchange administration is exposed primarily through remote PowerShell cmdlets. Many administrators use standard Windows PowerShell to connect to a remote Exchange server but if the account has MFA enabled, you need to install a separate Exchange Online PowerShell module based on the instructions in this document.
Follow the instructions here to connect to Exchange Online PowerShell with MFA. You can run scripts from this client or interact directly with Exchange. Some organizations create custom interactive scripts which provides a more admin friendly and less error prone interface for common administrative tasks on the tenant.
Portals
Office 365 provides portals to administrate Exchange Online, such as the Admin center, Security & Compliance Center and Exchange admin center. When MFA is enabled, you will be prompted for an authentication code.
Other Administration Workflows
Scheduled Automation
One of the main reasons organizations need to periodically run scripts on their tenant is for compliance/reporting requirements to scan the states of various assets. Some organizations have established procedures for employees to run a set of scripts as a part of their weekly/monthly responsibilities.
Some admins set up scheduled PowerShell tasks to delegate the responsibility of running this script to a machine. Of course, since the objective is to run these scripts without human intervention, MFA is not possible and will need to be turned off on these accounts. In order to authenticate into the service, administrators will still need to submit their credentials. Credentials should never be stored in plaintext. Instead, use the commands below to encode your password. You can only decode the password on the same computer with the same user account.
$AdminCred = Get-Credential
$AdminCred.Password | ConvertFrom-SecureString | Out-File C:AdminCred.txt
To submit this password in your scripts use the commands below. Replace “AdminUsername” with your account username.
$password = Get-Content C:AdminCred.txt | ConvertTo-SecureString
$Credentials = New-Object -typename System.Management.Automation.PSCredential -ArgumentList "AdminUsername",$password
Connect-EXOPSSession -Credential $AdminCred
Import-PSSession $ExoSession
Since this does still register a risk if an adversary breaches your computer, you should take the following precautions on the machine with the scheduled task:
- Tightly control access to the machine and disable Remote Desktop Protocol (RDP)
- Limit the use of the account to only administrative activities (disable mail or use an alt account)
- Set strong passwords
- Enable unified audit log and mailbox auditing
- Periodically review the audit logs for this account for signs of compromise
- Confine admin activities to within your network perimeter
- Constrain cmdlets permissions as tightly as possible to the account through role management
Exchange Role Management
You can limit the permissions of administrative accounts using role groups to ensure that even if the account does get breached, the actions that the attacker can take are limited to the administration responsibilities of the account. Details on how to manage role assignments are in this article.
Long-running Scripts
When running long scripts from the standard Windows PowerShell client, administrators have faced session timeouts. Typically, the solution is to wrap the script with a loop that checks for session timeouts and recover by submitting saved credentials to re-establish the session. Now, how would you do this without human intervention for MFA accounts which require a second method of authentication?
Fortunately, the Exchange Online PowerShell Module takes care of session timeouts by re-establishing the session automatically. NOTE: it is important to use the UserPrincipalName parameter to connect so that the client can automatically re-establish the session for you.
Connect-EXOPSSession –UserPrincipalName joe@contoso.com
See below, the original PowerShell session has expired before I ran the Get-mailbox command. The client recognizes that the session has expired and automatically creates a new session without prompting for credentials.
General Secure Administration Recommendations
Beyond using MFA for Exchange administration, Microsoft recommends that you also take a broader look at your security. Below are some great solutions and ideas to help protect administrator accounts:
We hope this post has helped create a more secure and usability friendly administration story for you. Leave us a comment below with feedback!
Overview
MFA enablement completely changes an organization’s security posture. Even though MFA does not necessarily provide perfect security, it does make it significantly more challenging to breach accounts and perhaps enough to encourage the attacker to seek out an easier target instead. This statement is not a presumption; during the 2017 Black Hat conference, multi-factor authentication and encryption were the 2 biggest named obstacles surveyed from hackers. Organizations recognize the benefits of MFA but we’ve received feedback about usability challenges in Exchange administration scenarios. This post identifies the popular administration workflows and will reference tools to fulfill them in accounts with MFA enforced.
To help increase the security of administrator accounts, you should enable MFA for your administrative accounts. For instructions on how to turn on MFA for Office 365 accounts, see this article. The workflow for users to set up MFA on their accounts is laid out in this document.
Exchange Online Administration Tools
Depending on the organization, Exchange Online is administrated through several different interfaces. The Office 365 customer base is incredibly diverse with larger tenants relying on automation to service their users while less complex organizations administrate the service from the portals.
Automation
Automation of Exchange administration is exposed primarily through remote PowerShell cmdlets. Many administrators use standard Windows PowerShell to connect to a remote Exchange server but if the account has MFA enabled, you need to install a separate Exchange Online PowerShell module based on the instructions in this document.
Follow the instructions here to connect to Exchange Online PowerShell with MFA. You can run scripts from this client or interact directly with Exchange. Some organizations create custom interactive scripts which provides a more admin friendly and less error prone interface for common administrative tasks on the tenant.
Portals
Office 365 provides portals to administrate Exchange Online, such as the Admin center, Security & Compliance Center and Exchange admin center. When MFA is enabled, you will be prompted for an authentication code.
Other Administration Workflows
Scheduled Automation
One of the main reasons organizations need to periodically run scripts on their tenant is for compliance/reporting requirements to scan the states of various assets. Some organizations have established procedures for employees to run a set of scripts as a part of their weekly/monthly responsibilities.
Some admins set up scheduled PowerShell tasks to delegate the responsibility of running this script to a machine. Of course, since the objective is to run these scripts without human intervention, MFA is not possible and will need to be turned off on these accounts. In order to authenticate into the service, administrators will still need to submit their credentials. Credentials should never be stored in plaintext. Instead, use the commands below to encode your password. You can only decode the password on the same computer with the same user account.
$AdminCred = Get-Credential
$AdminCred.Password | ConvertFrom-SecureString | Out-File C:AdminCred.txt
To submit this password in your scripts use the commands below. Replace “AdminUsername” with your account username.
$password = Get-Content C:AdminCred.txt | ConvertTo-SecureString
$Credentials = New-Object -typename System.Management.Automation.PSCredential -ArgumentList "AdminUsername",$password
Connect-EXOPSSession -Credential $AdminCred
Import-PSSession $ExoSession
Since this does still register a risk if an adversary breaches your computer, you should take the following precautions on the machine with the scheduled task:
- Tightly control access to the machine and disable Remote Desktop Protocol (RDP)
- Limit the use of the account to only administrative activities (disable mail or use an alt account)
- Set strong passwords
- Enable unified audit log and mailbox auditing
- Periodically review the audit logs for this account for signs of compromise
- Confine admin activities to within your network perimeter
- Constrain cmdlets permissions as tightly as possible to the account through role management
Exchange Role Management
You can limit the permissions of administrative accounts using role groups to ensure that even if the account does get breached, the actions that the attacker can take are limited to the administration responsibilities of the account. Details on how to manage role assignments are in this article.
Long-running Scripts
When running long scripts from the standard Windows PowerShell client, administrators have faced session timeouts. Typically, the solution is to wrap the script with a loop that checks for session timeouts and recover by submitting saved credentials to re-establish the session. Now, how would you do this without human intervention for MFA accounts which require a second method of authentication?
Fortunately, the Exchange Online PowerShell Module takes care of session timeouts by re-establishing the session automatically. NOTE: it is important to use the UserPrincipalName parameter to connect so that the client can automatically re-establish the session for you.
Connect-EXOPSSession –UserPrincipalName joe@contoso.com
See below, the original PowerShell session has expired before I ran the Get-mailbox command. The client recognizes that the session has expired and automatically creates a new session without prompting for credentials.
General Secure Administration Recommendations
Beyond using MFA for Exchange administration, Microsoft recommends that you also take a broader look at your security. Below are some great solutions and ideas to help protect administrator accounts:
We hope this post has helped create a more secure and usability friendly administration story for you. Leave us a comment below with feedback!
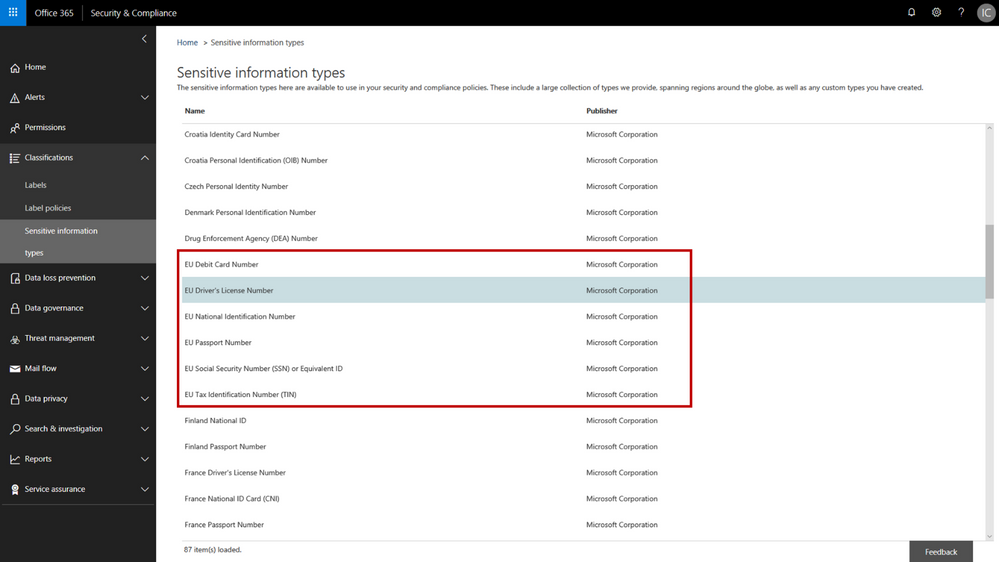
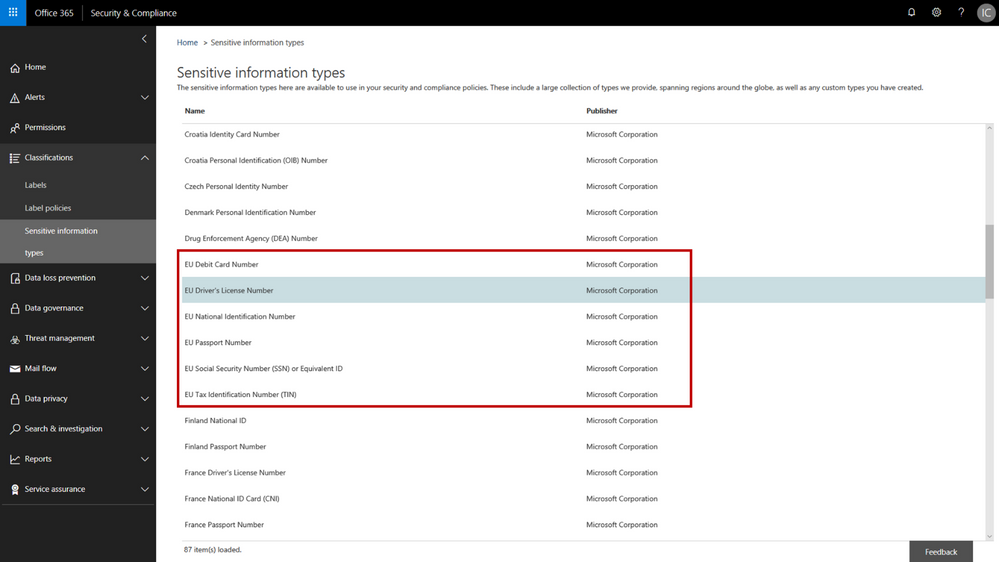
In February we announced several new capabilities coming soon to help organizations protect their sensitive data – across devices, apps, cloud services and on-premises. Today we’re announcing the general availability of several new sensitive information types and a new template that helps you discover, classify, protect and manage personal information that is relevant to GDPR obligations.
The addition of the new personal information data types adds to the existing built-in sensitive information types that are available in the Office 365 security & compliance center. You can use these sensitive information types in defining your data governance and data protection policies – there are now 87 different data types to choose from. While many of the previous sensitive information types were relevant to GDPR, the new sensitive information types help provide a more complete and consolidated set. The new personal information data types include:
- EU passport number
- EU national identification number
- EU driver’s license number
- EU tax identification number (TIN)
- EU social security number (SSN) or equivalent ID
For each of these information types, the service detects data that matches the specific patterns used by the 28 EU countries. For example, configuring your policy to include “EU driver’s license number” will detect driver’s license numbers used by any of the 28 covered EU countries.
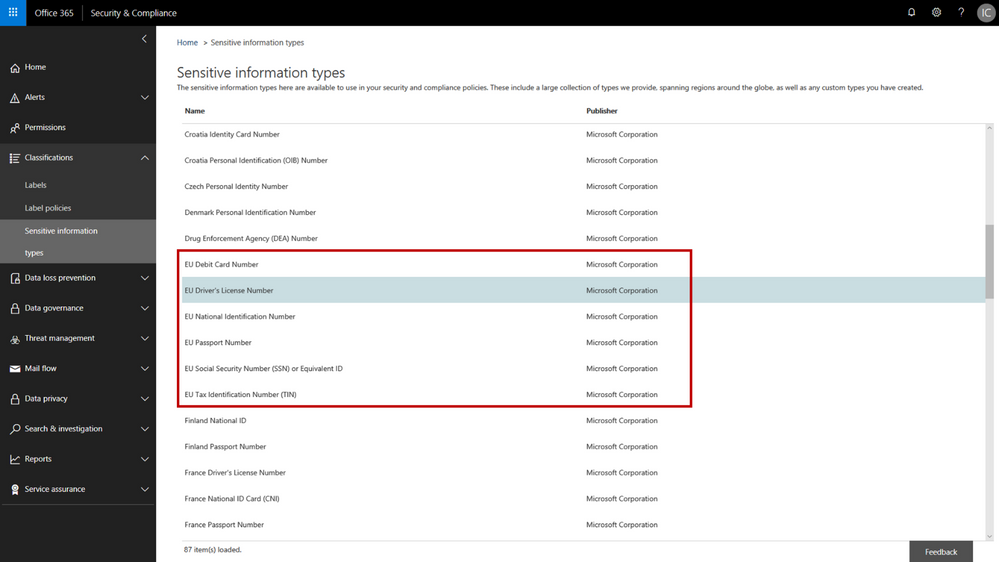 New EU personal information data types in the Office 365 Security & Compliance Center
New EU personal information data types in the Office 365 Security & Compliance Center
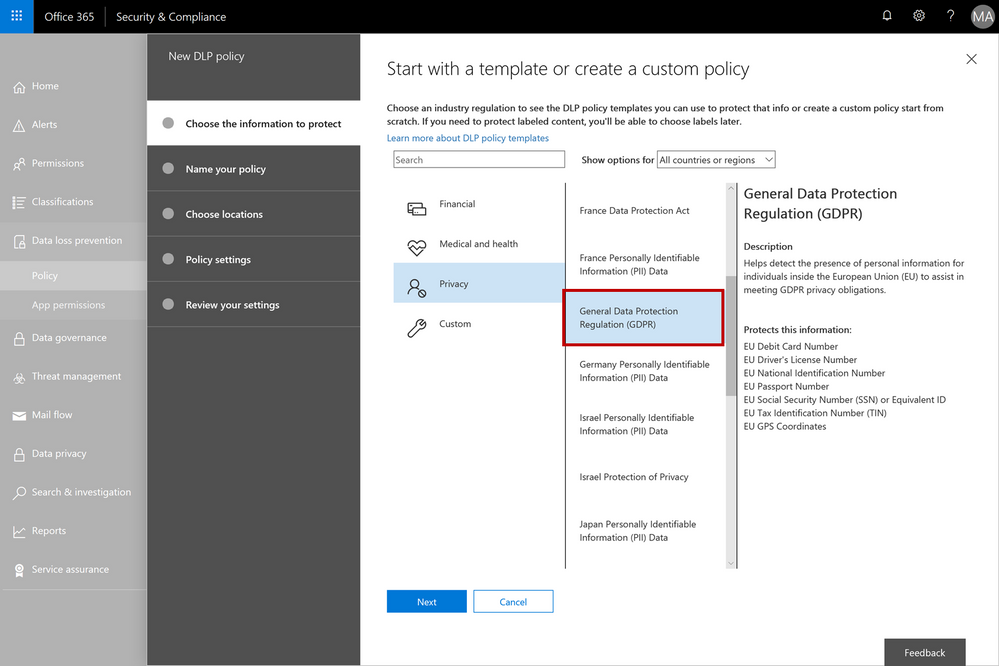
When configuring data governance or data loss prevention policies, you can now scan Office 365 locations (e.g. Exchange Online, SharePoint Online, OneDrive for Business) for personal information that matches the new EU data types, and then apply the desired data retention or protection actions. You can customize your policies to look for any combination of these new personal data types or use in conjunction with any of the other existing sensitive information types. For example, you can detect EU national identification numbers and EU passport numbers (both of which are new information types), in combination with US passport numbers (a previously available information type). We’ve also made it easy to detect any of the EU personal information data types by providing a GDPR template that consolidates these new information types into a single group that you can use in your policy configuration.
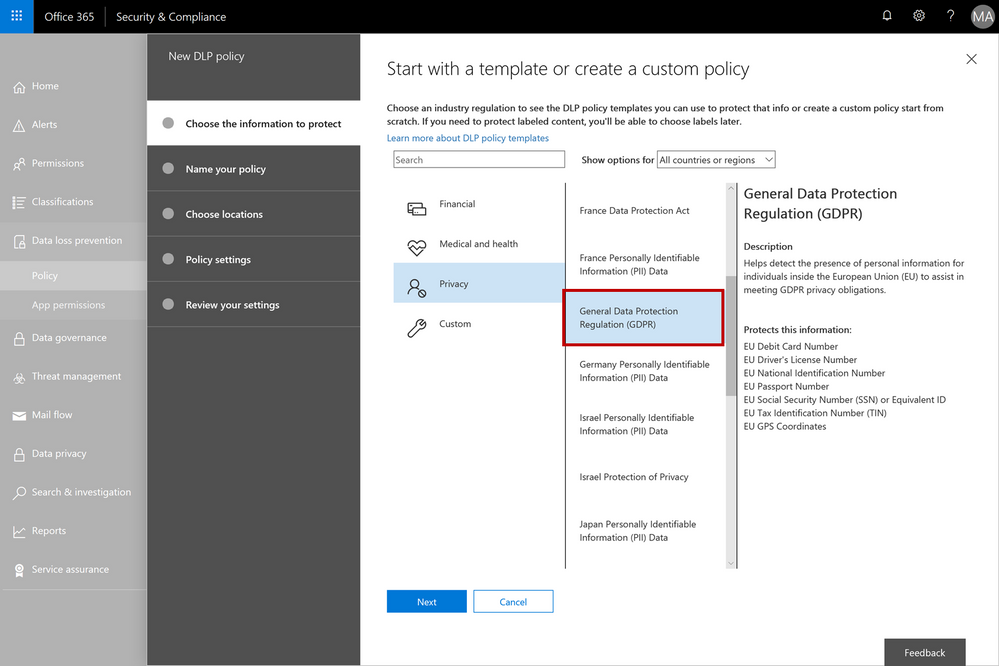 The GDPR template consolidates the new EU personal information data types into a single group – this can be used when configuring your data governance or data loss prevention policies
The GDPR template consolidates the new EU personal information data types into a single group – this can be used when configuring your data governance or data loss prevention policies
As with all the other sensitive information types, there is a lot of flexibility to customize and fine-tune the parameters to meet your specific needs. Learn more about the built-in sensitive information types or even create your own custom sensitive information types (such as employee ID numbers that are unique to your company).
We’re excited to release the new EU sensitive information types and GDPR template – this should help make it easier to discover, classify, protect and manage GDPR related personal information. Our support articles have also been updated with details on the specific detection methods and patterns associated with each of the data types. These new sensitive information types are available now in the Office 365 security and compliance center, and we are targeting these to also be available in Azure Information Protection in Q3 CY18. We are also investigating adding more EU personal information data types in the future and will provide more details as plans get formalized.