We’re excited to announce new improvements to the SharePoint Migration Tool for the month of February.
Designed to be used for migrations ranging from the smallest set of files to a large scale enterprise migration, the SharePoint Migration Tool will let you bring your information to the cloud and take advantage of the latest collaboration, intelligence, and security solutions with Office 365.
Over the past several months we’ve been continually working to add features to the SharePoint Migration Tool to help you accelerate your journey to Microsoft 365, from support for full site migrations, to incremental improvements to the user experience – the SharePoint Migration Tool is designed to support migrations of all sizes. This month we’re adding some exciting new improvements to help you on your journey to the cloud.
Improvements this month include:
Managed Metadata Service support
If you have an existing taxonomy in SharePoint Server 2013, the SharePoint Migration Tool can now migrate your content types and term stores to Office 365. Global term store migration requires global tenant admin permissions.
Web Parts Support, Site Navigation, and more…
The SharePoint Migration Tool has continuously improved to support more complex migration requirements. From a humble beginning of accelerating files migration to incremental improvements leading up to complete SharePoint 2013 site migrations. Now using the SharePoint Migration Tool you can migrate just about every element of SharePoint sites that you care most about including Web Parts, Pages, and site navigation!
For a detailed list of improvements in this release, refer to the release notes at https://docs.microsoft.com/en-us/sharepointmigration/new-and-improved-features-in-the-sharepoint-migration-tool.
If you’re new to the SharePoint Migration Tool, keep reading below to learn more about how you can transform your business by bringing it to the cloud.
About the SharePoint Migration Tool
The SharePoint Migration Tool is designed to simplify your journey to the cloud through a free, simple, and fast solution to migrate content from on-premises SharePoint sites and file shares to SharePoint or OneDrive in Office 365. The SharePoint Migration Tool allows you to accelerate your journey to Office 365 overcoming obstacles typically associated with migration projects. With the SharePoint Migration Tool you can evaluate and address the information that matters the most to your organization, the Libraries, and now Lists that form the foundation of the SharePoint experience. Using the SharePoint Migration Tool you can start your migration today and take advantage of the full suite of features and security capabilities that Office 365 offers.
Keep reading to learn more about the SharePoint Migration Tool or download the latest version now at https://aka.ms/SPMT.
Getting Started
You can download the SharePoint Migration Tool at http://aka.ms/SPMT. Through v3 of the SharePoint Migration Tool you’ll have available to you the innovation we’re delivering to help you bring your information to the cloud and take advantage of the latest collaboration, intelligence, and security solutions with Office 365.
What’s next…
Through continued innovation across migration scenarios we’ll be adding more capabilities over time to the SharePoint Migration Tool, including support for more SharePoint versions, site structure migrations, and more. Subscribe here to stay up to date on future announcements for SharePoint and Office 365.
Wrapping Up…
Whether you’re looking to migrate from file shares on-premises to SharePoint or OneDrive or from on-premises versions of SharePoint, the SharePoint Migration Tool is designed to support the smallest of migrations to large scale migrations with support for bulk scenarios.
Learn more about migrating to Office 365 at https://resources.techcommunity.microsoft.com/cloud-migration/.
Learn more about the SharePoint Migration Tool at https://support.office.com/en-us/article/Introducing-the-SharePoint-Migration-Tool-9c38f5df-300b-4adc-8fac-648d0215b5f7.
Prepare your environment for migration using the SharePoint Migration Assessment Tool by learning more at https://www.microsoft.com/en-us/download/details.aspx?id=53598.
Today, we are excited to announce new capabilities in Advanced eDiscovery that directly respond to customer feedback on how they need to be able to do more with the built-in discovery tools in Microsoft 365. We have heard that organizations require expanded capabilities to complete more of common investigation and discovery workflows right within Microsoft 365.
Now we are starting to rollout a new version of Advanced eDiscovery that includes a new look and feel, additional functionality such as hold notifications and acknowledgment tracking, and a concept of a static set of content for performant searches as well as an integrated review and redact experience.
With these new updates we hope to more directly meet customer requirements for an efficient and effective way to preserve, collect and review content related to investigations or litigation.
Microsoft’s director of discovery, EJ Bastien has stated that even as “data from the average custodian has increased 20x over the last ten years, our team has reduced the cost per custodian of completing this eDiscovery work by 85%. While also maintaining high security standards of keeping data in place within the Microsoft cloud.” The capabilities integrated into Microsoft 365 have enabled Microsoft discovery to change the playing field on meeting legal and investigation requirements.
Read on below for more on the new features and check out the Mechanics video where we show and tell a bit about how the capabilities work.
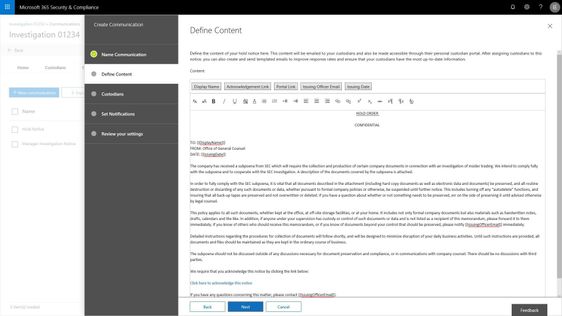
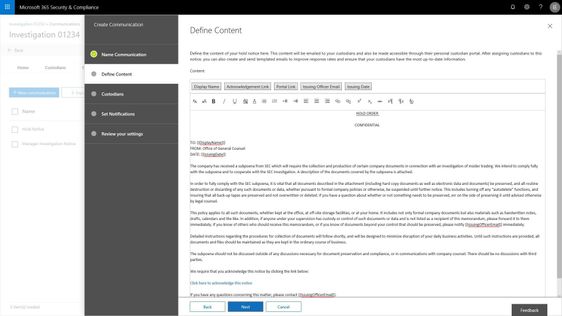
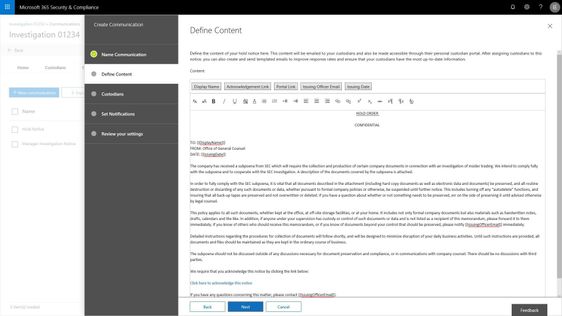
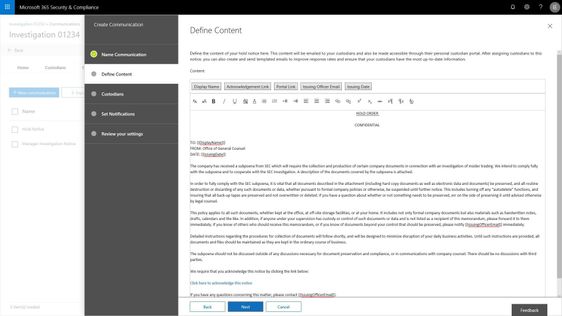
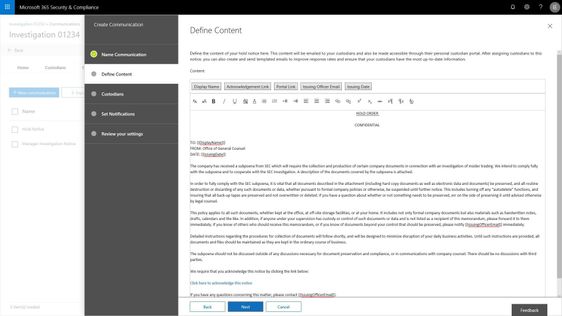
Manage custodians and notifications
Customers have told us they need to be able to manage custodians, or employees in their organization related to a particular case or investigation, from both the perspective of the content the custodian controls and manages in their email inbox and cloud storage, but also from the perspective of the shared locations that those employees interact with as part of their daily job such as team sites, groups, and channels. In addition to retention and discovery, we have also heard that organizations require a way to communicate to those custodians that are legal hold within their organization. Not only communicate with custodians, but track the fact that the custodians have been notified. Now you can manage complete that entire process right within your Advanced eDiscovery experience.
Search to add custodians and their custodial content locations, add sites and teams that they are members of from the shared locations picker, and place their content on hold for retention and discovery purposes. With the new custodial picker experience, you have a quick look up from Azure Active Directory in your organization to quickly find and identify individuals by name or organization identification alias.
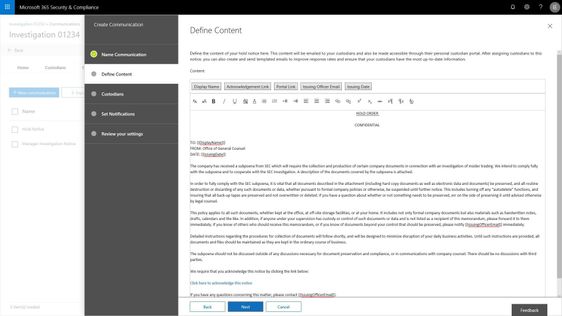
Use templates to build out commonly used communications, escalate with reminders and or manager notifications. And the end user gets a clean experience showing them all of their active legal holds or other case related notifications.
Manage case content with consistency and performance using working sets
We have also heard that search and content processing needs to be higher performing, more predictable and transparent. Customers have told us that any variability in search results erodes confidence and ability to effectively complete the requirements of some eDiscovery processes. In addition, defensibility of the results is weakened, and it is just harder to get things done quickly and efficiently.
In order to help address this challenge and others, now you can isolate the set of results from a search and add it to a working set for further analysis, processing and refinement. Once this content is included in a working set you have a number of ways that you can interact with that content, all of which help you define and address the most responsive and relevant content in your case or investigation.
Customers are continuing to derive value form the advanced analytics capabilities already included in Advanced eDiscovery as the core vehicle to reduce and refine content. This reduction helps to drive down redundant, duplicative or highly related content and reduce the costs of eDiscovery.
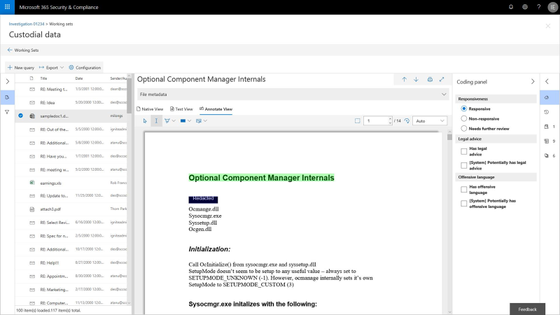
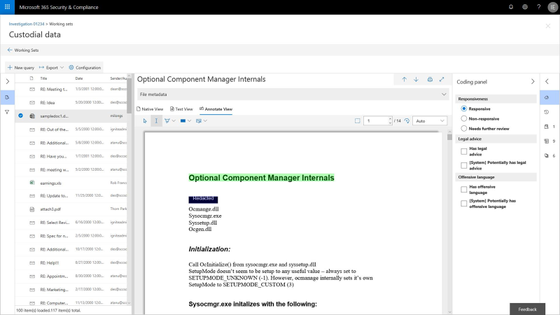
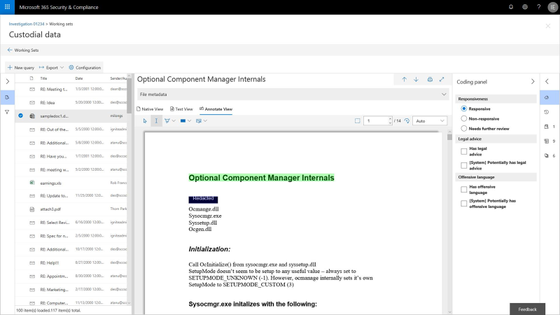
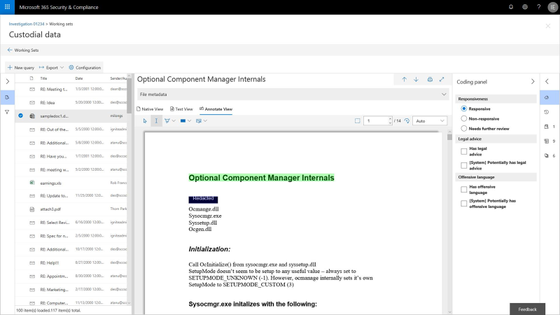
Integrated review and redact experience
Now organizations can review and take action on the content within their case right within Microsoft 365. A new integrated review experience offers the ability to view a wide variety of file types, including jpgs, all office files, mp4s and more, and to take action on that content. Either tag and further refine content based on its responsiveness, or annotate, mark-up and redact content that might be sensitive and should not be shared with outside parties.
The new review experience includes a native, text and annotate view to provide options to support the various ways your team assess content. In addition, a customizable coding panel helps make sure that you are able to effectively tag and triage and organize the content under review. Further insights such as document history, other contributors to the document and views like difference detection in near duplicates will help speed the process to identify and curate the most responsive content.
Watch the short video and read more about this new review and redact experience here.
Data Investigations preview
Also today, we are announcing a new preview for a Data Investigations capability that helps IT and security operations search and take action on specific data in their organizations. Many organizations need to address scenarios like leaked confidential information, or investigating data breaches with this type of data remediation workflow. These scenarios are important as the risk to data security and privacy expectations continue to evolve. IT and privacy officers now have the tools to respond to any kinds of risk to personal, sensitive or business confidential information effectively and efficiently with this new solution.
The new capability, starting to roll out to preview today, includes the ability to execute targeted searches for specific content based on a variety of conditions, then investigate user activity around relevant content, and contain and ultimately remediate the leaked content at the source. Read more about the early look at this new capability here.
Ready to get started?
Make sure you have Office 365 E5, Advanced Compliance, or Microsoft 365 Information Protection and Compliance to get started today with these new features.
Read more about Advanced eDiscovery in Microsoft 365, see our broader updates and webcast on privacy and compliance in the modern era of privacy expectations and engage with us in our Tech Community .
- Iram Arras, Sr Program Manager, Advanced eDiscovery Microsoft 365
Today, we are excited to announce new capabilities in Advanced eDiscovery that directly respond to customer feedback on how they need to be able to do more with the built-in discovery tools in Microsoft 365. We have heard that organizations require expanded capabilities to complete more of common investigation and discovery workflows right within Microsoft 365.
Now we are starting to rollout a new version of Advanced eDiscovery that includes a new look and feel, additional functionality such as hold notifications and acknowledgment tracking, and a concept of a static set of content for performant searches as well as an integrated review and redact experience.
With these new updates we hope to more directly meet customer requirements for an efficient and effective way to preserve, collect and review content related to investigations or litigation.
Microsoft’s director of discovery, EJ Bastien has stated that even as “data from the average custodian has increased 20x over the last ten years, our team has reduced the cost per custodian of completing this eDiscovery work by 85%. While also maintaining high security standards of keeping data in place within the Microsoft cloud.” The capabilities integrated into Microsoft 365 have enabled Microsoft discovery to change the playing field on meeting legal and investigation requirements.
Read on below for more on the new features and check out the Mechanics video where we show and tell a bit about how the capabilities work.
Manage custodians and notifications
Customers have told us they need to be able to manage custodians, or employees in their organization related to a particular case or investigation, from both the perspective of the content the custodian controls and manages in their email inbox and cloud storage, but also from the perspective of the shared locations that those employees interact with as part of their daily job such as team sites, groups, and channels. In addition to retention and discovery, we have also heard that organizations require a way to communicate to those custodians that are legal hold within their organization. Not only communicate with custodians, but track the fact that the custodians have been notified. Now you can manage complete that entire process right within your Advanced eDiscovery experience.
Search to add custodians and their custodial content locations, add sites and teams that they are members of from the shared locations picker, and place their content on hold for retention and discovery purposes. With the new custodial picker experience, you have a quick look up from Azure Active Directory in your organization to quickly find and identify individuals by name or organization identification alias.
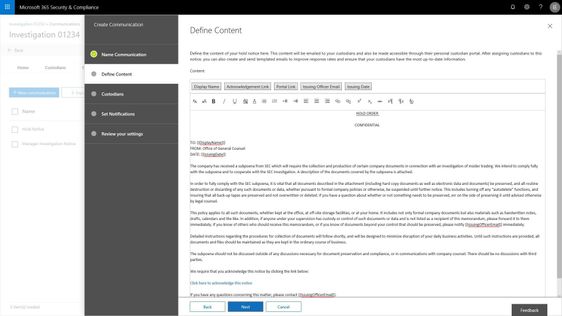
Use templates to build out commonly used communications, escalate with reminders and or manager notifications. And the end user gets a clean experience showing them all of their active legal holds or other case related notifications.
Manage case content with consistency and performance using working sets
We have also heard that search and content processing needs to be higher performing, more predictable and transparent. Customers have told us that any variability in search results erodes confidence and ability to effectively complete the requirements of some eDiscovery processes. In addition, defensibility of the results is weakened, and it is just harder to get things done quickly and efficiently.
In order to help address this challenge and others, now you can isolate the set of results from a search and add it to a working set for further analysis, processing and refinement. Once this content is included in a working set you have a number of ways that you can interact with that content, all of which help you define and address the most responsive and relevant content in your case or investigation.
Customers are continuing to derive value form the advanced analytics capabilities already included in Advanced eDiscovery as the core vehicle to reduce and refine content. This reduction helps to drive down redundant, duplicative or highly related content and reduce the costs of eDiscovery.
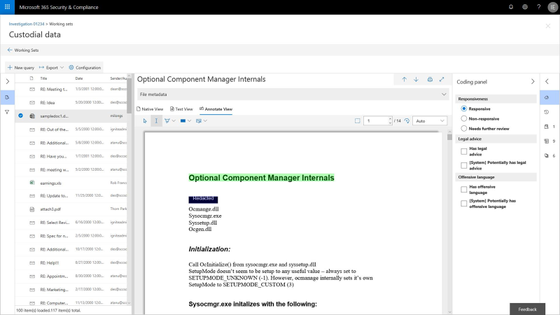
Integrated review and redact experience
Now organizations can review and take action on the content within their case right within Microsoft 365. A new integrated review experience offers the ability to view a wide variety of file types, including jpgs, all office files, mp4s and more, and to take action on that content. Either tag and further refine content based on its responsiveness, or annotate, mark-up and redact content that might be sensitive and should not be shared with outside parties.
The new review experience includes a native, text and annotate view to provide options to support the various ways your team assess content. In addition, a customizable coding panel helps make sure that you are able to effectively tag and triage and organize the content under review. Further insights such as document history, other contributors to the document and views like difference detection in near duplicates will help speed the process to identify and curate the most responsive content.
Watch the short video and read more about this new review and redact experience here.
Data Investigations preview
Also today, we are announcing a new preview for a Data Investigations capability that helps IT and security operations search and take action on specific data in their organizations. Many organizations need to address scenarios like leaked confidential information, or investigating data breaches with this type of data remediation workflow. These scenarios are important as the risk to data security and privacy expectations continue to evolve. IT and privacy officers now have the tools to respond to any kinds of risk to personal, sensitive or business confidential information effectively and efficiently with this new solution.
The new capability, starting to roll out to preview today, includes the ability to execute targeted searches for specific content based on a variety of conditions, then investigate user activity around relevant content, and contain and ultimately remediate the leaked content at the source. Read more about the early look at this new capability here.
Ready to get started?
Make sure you have Office 365 E5, Advanced Compliance, or Microsoft 365 Information Protection and Compliance to get started today with these new features.
Read more about Advanced eDiscovery in Microsoft 365, see our broader updates and webcast on privacy and compliance in the modern era of privacy expectations and engage with us in our Tech Community .
- Iram Arras, Sr Program Manager, Advanced eDiscovery Microsoft 365
Today, we are excited to announce new capabilities in Advanced eDiscovery that directly respond to customer feedback on how they need to be able to do more with the built-in discovery tools in Microsoft 365. We have heard that organizations require expanded capabilities to complete more of common investigation and discovery workflows right within Microsoft 365.
Now we are starting to rollout a new version of Advanced eDiscovery that includes a new look and feel, additional functionality such as hold notifications and acknowledgment tracking, and a concept of a static set of content for performant searches as well as an integrated review and redact experience.
With these new updates we hope to more directly meet customer requirements for an efficient and effective way to preserve, collect and review content related to investigations or litigation.
Microsoft’s director of discovery, EJ Bastien has stated that even as “data from the average custodian has increased 20x over the last ten years, our team has reduced the cost per custodian of completing this eDiscovery work by 85%. While also maintaining high security standards of keeping data in place within the Microsoft cloud.” The capabilities integrated into Microsoft 365 have enabled Microsoft discovery to change the playing field on meeting legal and investigation requirements.
Read on below for more on the new features and check out the Mechanics video where we show and tell a bit about how the capabilities work.
Manage custodians and notifications
Customers have told us they need to be able to manage custodians, or employees in their organization related to a particular case or investigation, from both the perspective of the content the custodian controls and manages in their email inbox and cloud storage, but also from the perspective of the shared locations that those employees interact with as part of their daily job such as team sites, groups, and channels. In addition to retention and discovery, we have also heard that organizations require a way to communicate to those custodians that are legal hold within their organization. Not only communicate with custodians, but track the fact that the custodians have been notified. Now you can manage complete that entire process right within your Advanced eDiscovery experience.
Search to add custodians and their custodial content locations, add sites and teams that they are members of from the shared locations picker, and place their content on hold for retention and discovery purposes. With the new custodial picker experience, you have a quick look up from Azure Active Directory in your organization to quickly find and identify individuals by name or organization identification alias.
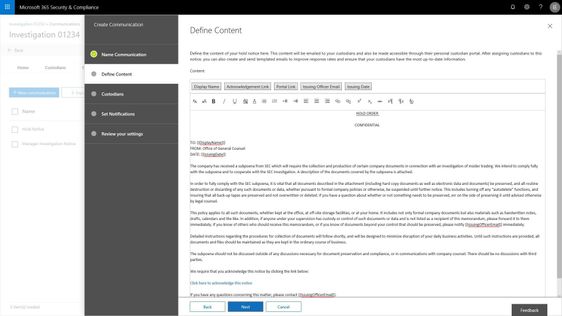
Use templates to build out commonly used communications, escalate with reminders and or manager notifications. And the end user gets a clean experience showing them all of their active legal holds or other case related notifications.
Manage case content with consistency and performance using working sets
We have also heard that search and content processing needs to be higher performing, more predictable and transparent. Customers have told us that any variability in search results erodes confidence and ability to effectively complete the requirements of some eDiscovery processes. In addition, defensibility of the results is weakened, and it is just harder to get things done quickly and efficiently.
In order to help address this challenge and others, now you can isolate the set of results from a search and add it to a working set for further analysis, processing and refinement. Once this content is included in a working set you have a number of ways that you can interact with that content, all of which help you define and address the most responsive and relevant content in your case or investigation.
Customers are continuing to derive value form the advanced analytics capabilities already included in Advanced eDiscovery as the core vehicle to reduce and refine content. This reduction helps to drive down redundant, duplicative or highly related content and reduce the costs of eDiscovery.
Integrated review and redact experience
Now organizations can review and take action on the content within their case right within Microsoft 365. A new integrated review experience offers the ability to view a wide variety of file types, including jpgs, all office files, mp4s and more, and to take action on that content. Either tag and further refine content based on its responsiveness, or annotate, mark-up and redact content that might be sensitive and should not be shared with outside parties.
The new review experience includes a native, text and annotate view to provide options to support the various ways your team assess content. In addition, a customizable coding panel helps make sure that you are able to effectively tag and triage and organize the content under review. Further insights such as document history, other contributors to the document and views like difference detection in near duplicates will help speed the process to identify and curate the most responsive content.
Watch the short video and read more about this new review and redact experience here.
Data Investigations preview
Also today, we are announcing a new preview for a Data Investigations capability that helps IT and security operations search and take action on specific data in their organizations. Many organizations need to address scenarios like leaked confidential information, or investigating data breaches with this type of data remediation workflow. These scenarios are important as the risk to data security and privacy expectations continue to evolve. IT and privacy officers now have the tools to respond to any kinds of risk to personal, sensitive or business confidential information effectively and efficiently with this new solution.
The new capability, starting to roll out to preview today, includes the ability to execute targeted searches for specific content based on a variety of conditions, then investigate user activity around relevant content, and contain and ultimately remediate the leaked content at the source. Read more about the early look at this new capability here.
Ready to get started?
Make sure you have Office 365 E5, Advanced Compliance, or Microsoft 365 Information Protection and Compliance to get started today with these new features.
Read more about Advanced eDiscovery in Microsoft 365, see our broader updates and webcast on privacy and compliance in the modern era of privacy expectations and engage with us in our Tech Community .
- Iram Arras, Sr Program Manager, Advanced eDiscovery Microsoft 365
Today, we are excited to announce new capabilities in Advanced eDiscovery that directly respond to customer feedback on how they need to be able to do more with the built-in discovery tools in Microsoft 365. We have heard that organizations require expanded capabilities to complete more of common investigation and discovery workflows right within Microsoft 365.
Now we are starting to rollout a new version of Advanced eDiscovery that includes a new look and feel, additional functionality such as hold notifications and acknowledgment tracking, and a concept of a static set of content for performant searches as well as an integrated review and redact experience.
With these new updates we hope to more directly meet customer requirements for an efficient and effective way to preserve, collect and review content related to investigations or litigation.
Microsoft’s director of discovery, EJ Bastien has stated that even as “data from the average custodian has increased 20x over the last ten years, our team has reduced the cost per custodian of completing this eDiscovery work by 85%. While also maintaining high security standards of keeping data in place within the Microsoft cloud.” The capabilities integrated into Microsoft 365 have enabled Microsoft discovery to change the playing field on meeting legal and investigation requirements.
Read on below for more on the new features and check out the Mechanics video where we show and tell a bit about how the capabilities work.
Manage custodians and notifications
Customers have told us they need to be able to manage custodians, or employees in their organization related to a particular case or investigation, from both the perspective of the content the custodian controls and manages in their email inbox and cloud storage, but also from the perspective of the shared locations that those employees interact with as part of their daily job such as team sites, groups, and channels. In addition to retention and discovery, we have also heard that organizations require a way to communicate to those custodians that are legal hold within their organization. Not only communicate with custodians, but track the fact that the custodians have been notified. Now you can manage complete that entire process right within your Advanced eDiscovery experience.
Search to add custodians and their custodial content locations, add sites and teams that they are members of from the shared locations picker, and place their content on hold for retention and discovery purposes. With the new custodial picker experience, you have a quick look up from Azure Active Directory in your organization to quickly find and identify individuals by name or organization identification alias.
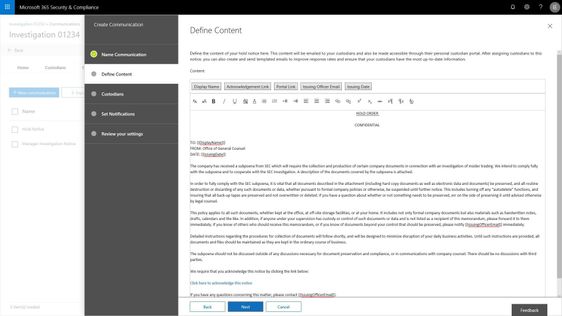
Use templates to build out commonly used communications, escalate with reminders and or manager notifications. And the end user gets a clean experience showing them all of their active legal holds or other case related notifications.
Manage case content with consistency and performance using working sets
We have also heard that search and content processing needs to be higher performing, more predictable and transparent. Customers have told us that any variability in search results erodes confidence and ability to effectively complete the requirements of some eDiscovery processes. In addition, defensibility of the results is weakened, and it is just harder to get things done quickly and efficiently.
In order to help address this challenge and others, now you can isolate the set of results from a search and add it to a working set for further analysis, processing and refinement. Once this content is included in a working set you have a number of ways that you can interact with that content, all of which help you define and address the most responsive and relevant content in your case or investigation.
Customers are continuing to derive value form the advanced analytics capabilities already included in Advanced eDiscovery as the core vehicle to reduce and refine content. This reduction helps to drive down redundant, duplicative or highly related content and reduce the costs of eDiscovery.
Integrated review and redact experience
Now organizations can review and take action on the content within their case right within Microsoft 365. A new integrated review experience offers the ability to view a wide variety of file types, including jpgs, all office files, mp4s and more, and to take action on that content. Either tag and further refine content based on its responsiveness, or annotate, mark-up and redact content that might be sensitive and should not be shared with outside parties.
The new review experience includes a native, text and annotate view to provide options to support the various ways your team assess content. In addition, a customizable coding panel helps make sure that you are able to effectively tag and triage and organize the content under review. Further insights such as document history, other contributors to the document and views like difference detection in near duplicates will help speed the process to identify and curate the most responsive content.
Watch the short video and read more about this new review and redact experience here.
Data Investigations preview
Also today, we are announcing a new preview for a Data Investigations capability that helps IT and security operations search and take action on specific data in their organizations. Many organizations need to address scenarios like leaked confidential information, or investigating data breaches with this type of data remediation workflow. These scenarios are important as the risk to data security and privacy expectations continue to evolve. IT and privacy officers now have the tools to respond to any kinds of risk to personal, sensitive or business confidential information effectively and efficiently with this new solution.
The new capability, starting to roll out to preview today, includes the ability to execute targeted searches for specific content based on a variety of conditions, then investigate user activity around relevant content, and contain and ultimately remediate the leaked content at the source. Read more about the early look at this new capability here.
Ready to get started?
Make sure you have Office 365 E5, Advanced Compliance, or Microsoft 365 Information Protection and Compliance to get started today with these new features.
Read more about Advanced eDiscovery in Microsoft 365, see our broader updates and webcast on privacy and compliance in the modern era of privacy expectations and engage with us in our Tech Community .
- Iram Arras, Sr Program Manager, Advanced eDiscovery Microsoft 365
White Paper
Microsoft 365 provides innovative capabilities to empower anyone – developers, power users, and information workers – to craft business applications tailored to real-world needs.
SharePoint lists provide foundational data storage across the suite. PowerApps and Microsoft Flow bring custom forms and workflow into business applications. And Microsoft Forms and Power BI extend business apps with data gathering and analytics.
That’s a lot of power. If you’re a problem solver, you’re in the right place. Our new white paper “Transforming Business Process with Microsoft 365” helps you understand these capabilities. You’ll learn about why business apps matter. We review the core capabilities of each tool – SharePoint lists, PowerApps, Flow, Forms, and Power BI. Finally, we complete the journey by presenting three scenarios to guide your implementation:
- Event organizer
- Travel approval
- Employee onboarding
Each solution is accompanied by templates you can use immediately. Download the white paper today to start this journey.
Solutions
We also know that there’s no substitute for learning by doing. That’s why our white paper is accompanied by three downloadable scenario templates. Each includes setup scripts, PowerApps, Flow, and other tools, along with videos and step by step instructions to help you bring each of these solutions to life in your own environment.
These solutions take their place alongside the other templates already published on the TechCommunity Resource Center. Let’s take a look.
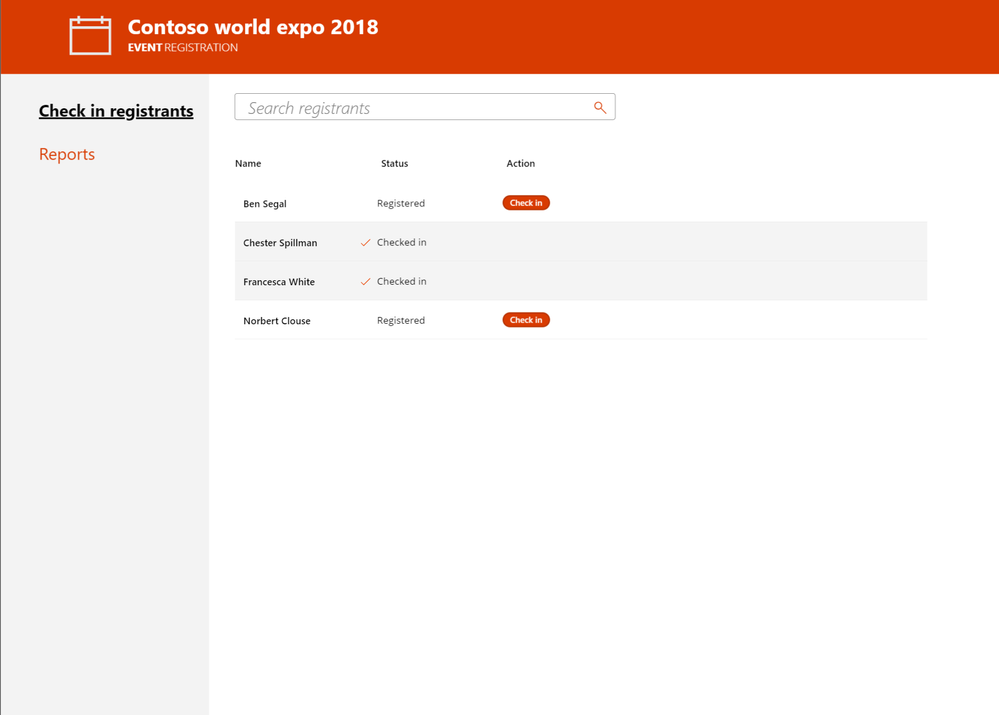
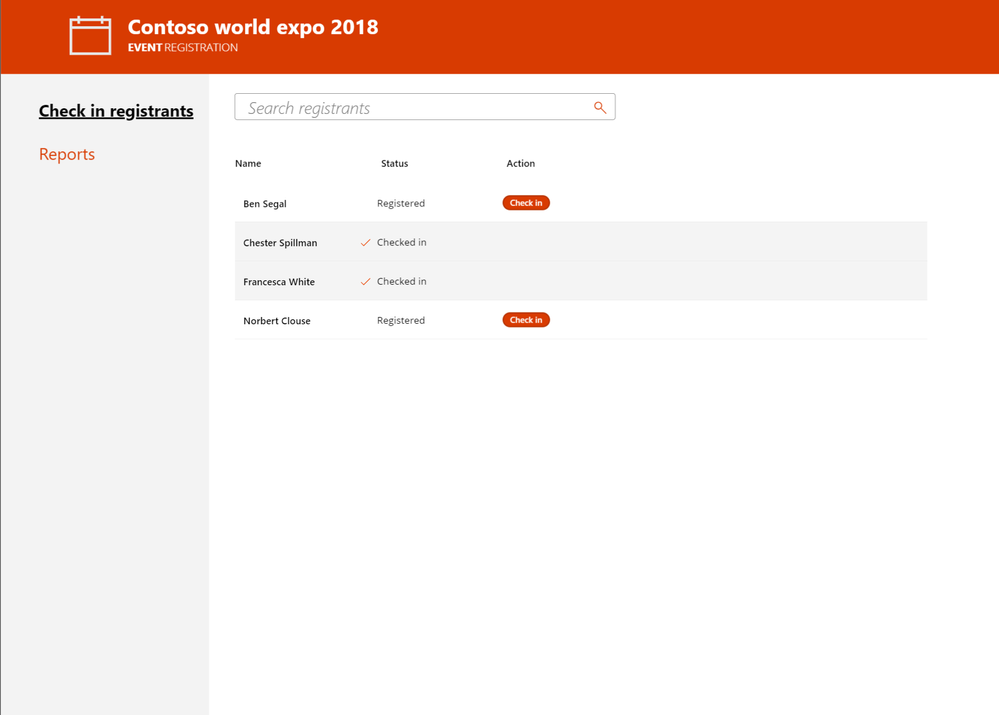
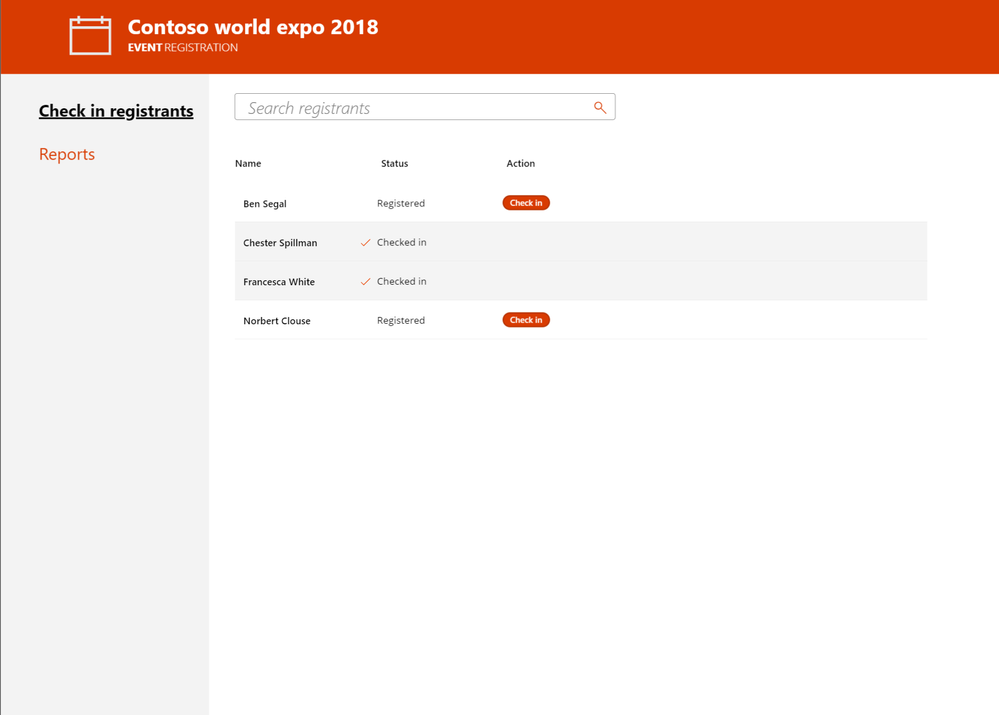
Event organizer
This solution allows you to invitee attendees to self-register for an event using Microsoft Forms. Registrations are tracked in a SharePoint list, which can be deployed automatically using our site scripts included in the solution. Microsoft Flow is used to provide alerts , confirmations, and reminders about the event to attendees and staff. Power BI is used for real-time reporting on attendee registrations and attendance. Finally, this solution includes mobile and tablet versions of our PowerApps solution for checking in and managing attendees on the day of the event. Download the template and get started.
 Event Organizer
Event Organizer
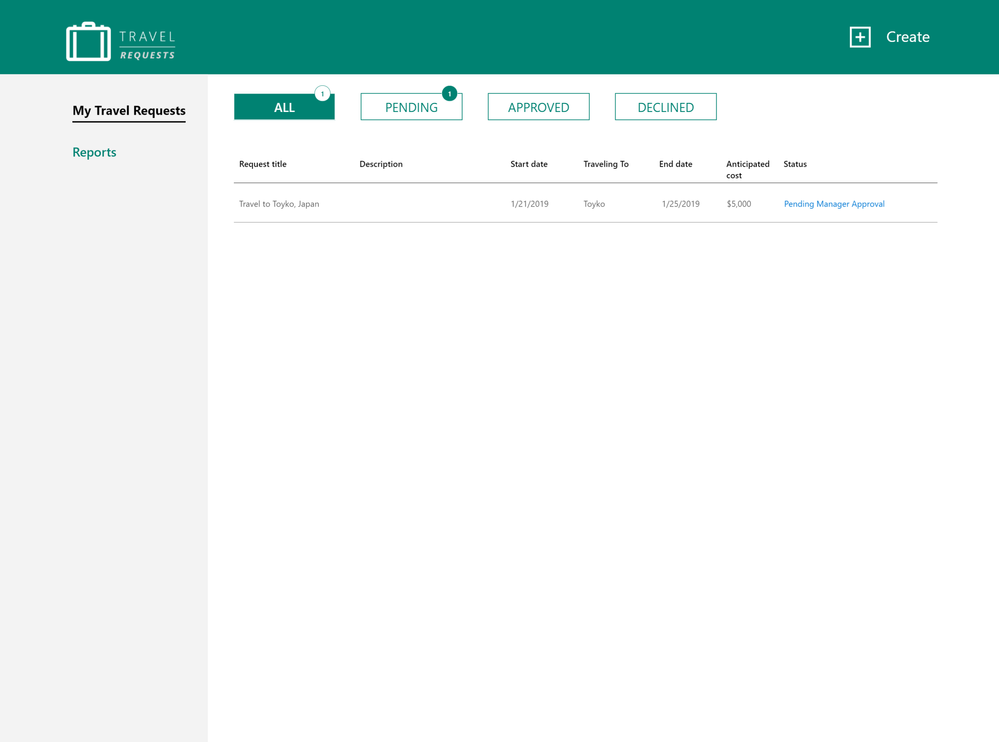
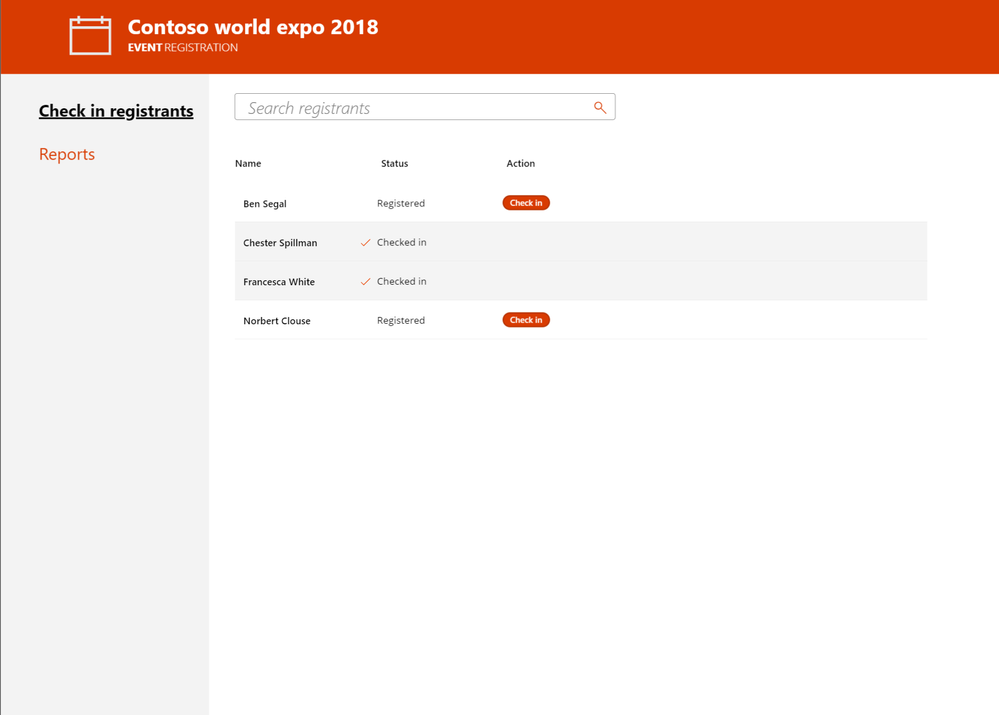
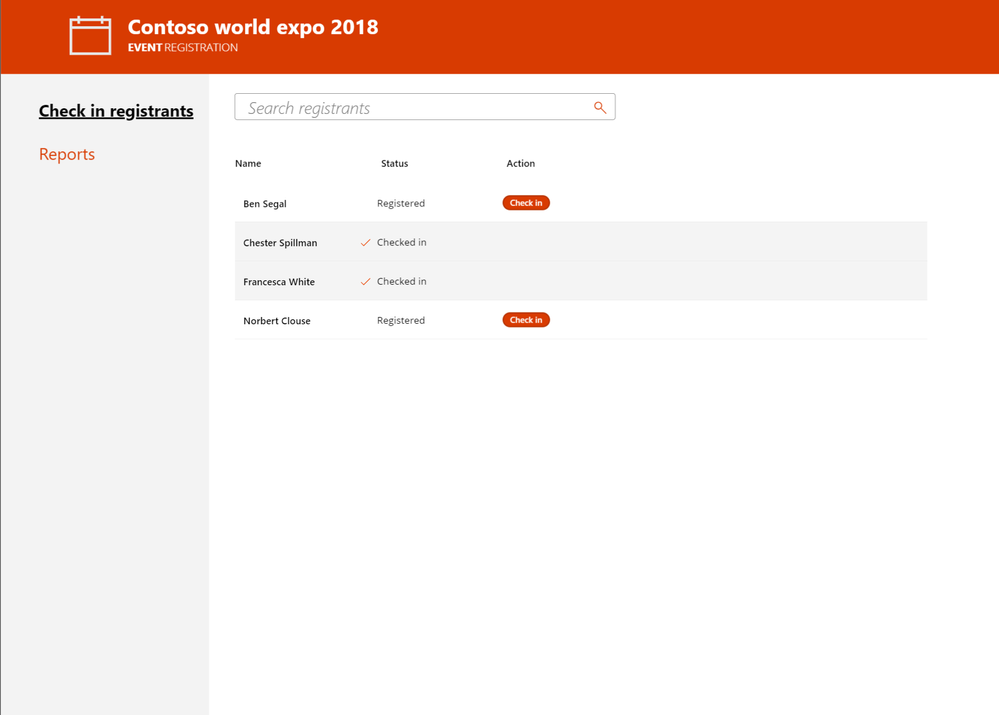
Travel Approval
Travel is a critical part of business operations. This solution allows employees to easily submit travel requests from desktop or mobile devices using PowerApps. Requests are automatically routed using Flow to the appropriate manager and travel department for approval. Managers can also access Power BI based status reports for all travel requests to verify current status and manage budgets. Get started with our downloadable template.
 Travel Requests
Travel Requests
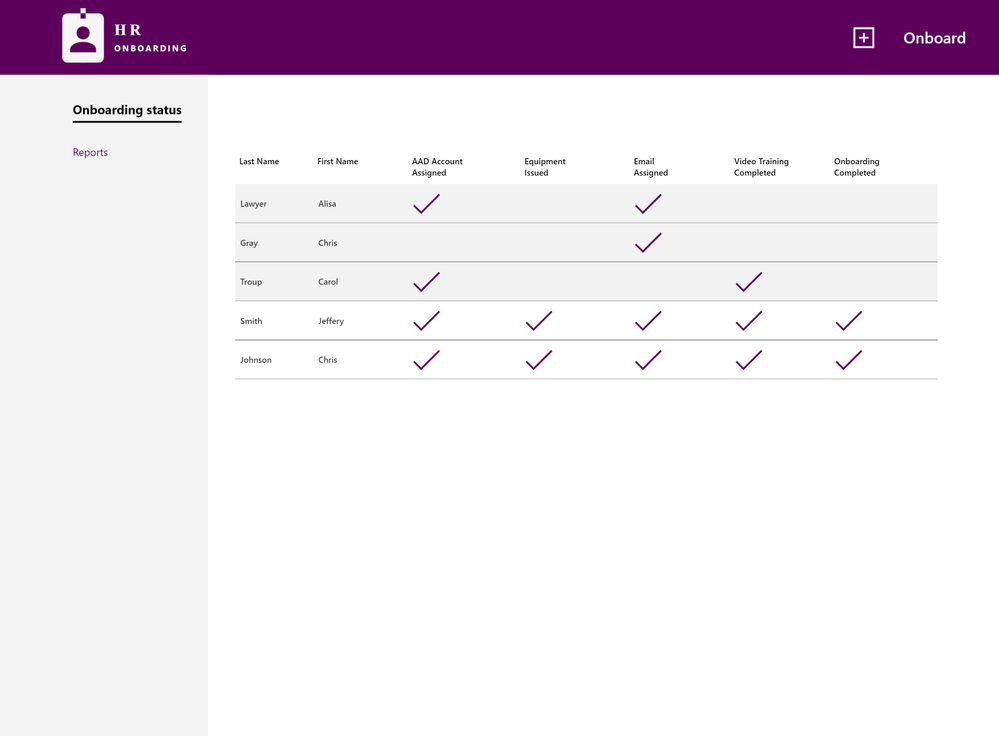
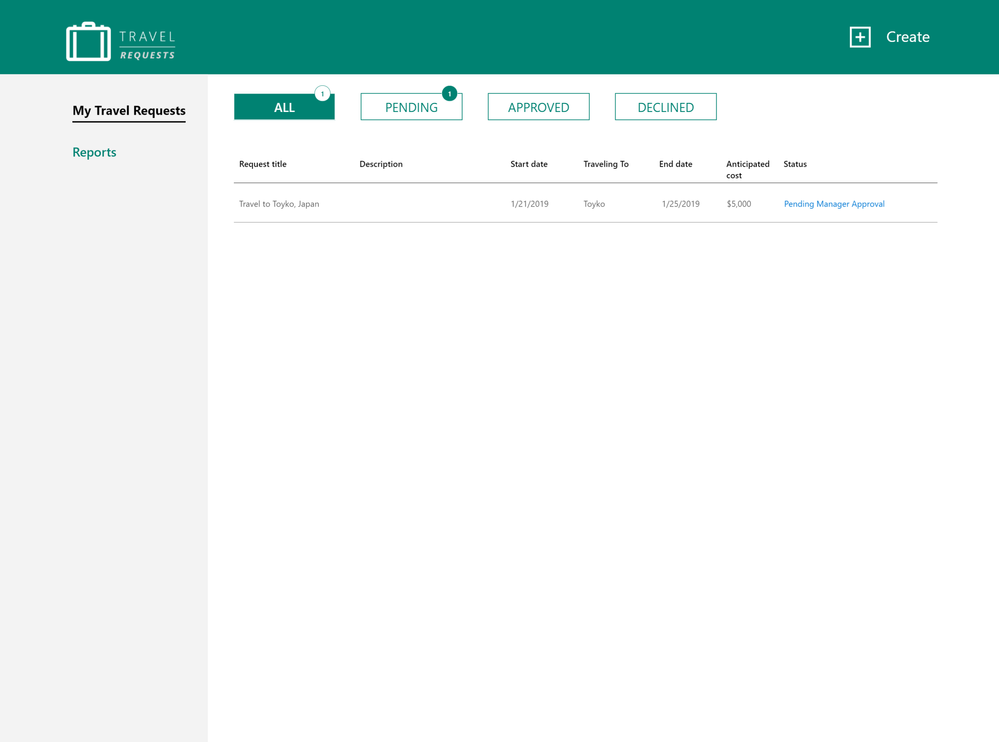
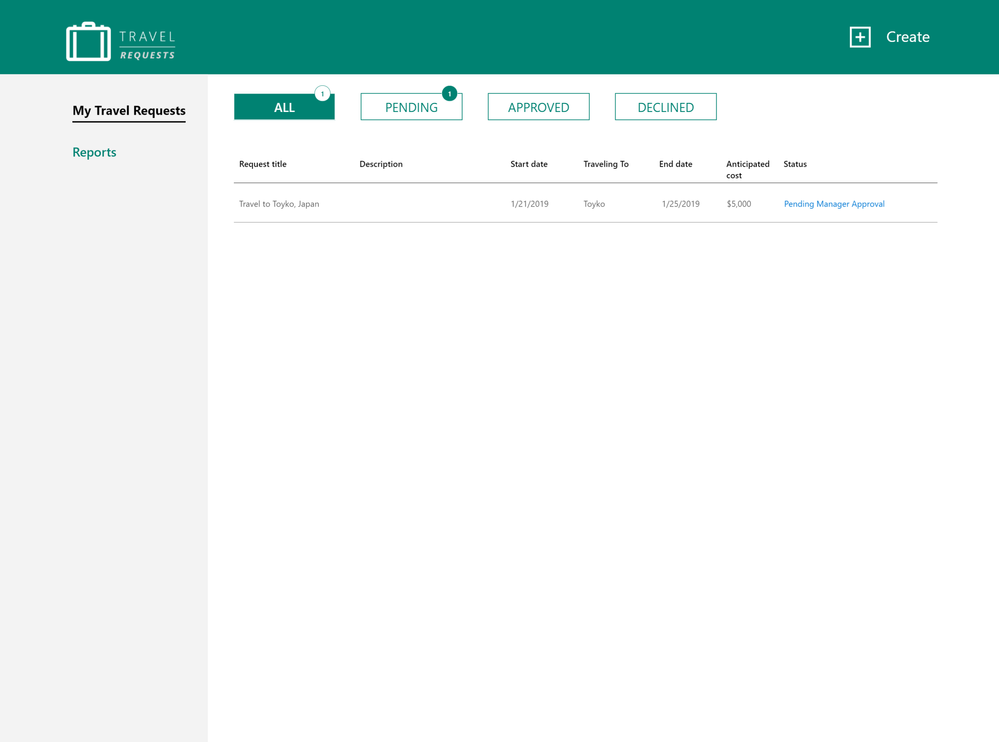
Employee onboarding
The Employee Onboarding app is designed to streamline and simplify the process of bringing a new employee onboard into the organization. In many organizations, onboarding new employees can be a complicated and laborious process. This solution integrates PowerApps, SharePoint and Flow to manage procurement, logins, email and training tasks for new staff. Download our template to get started today.
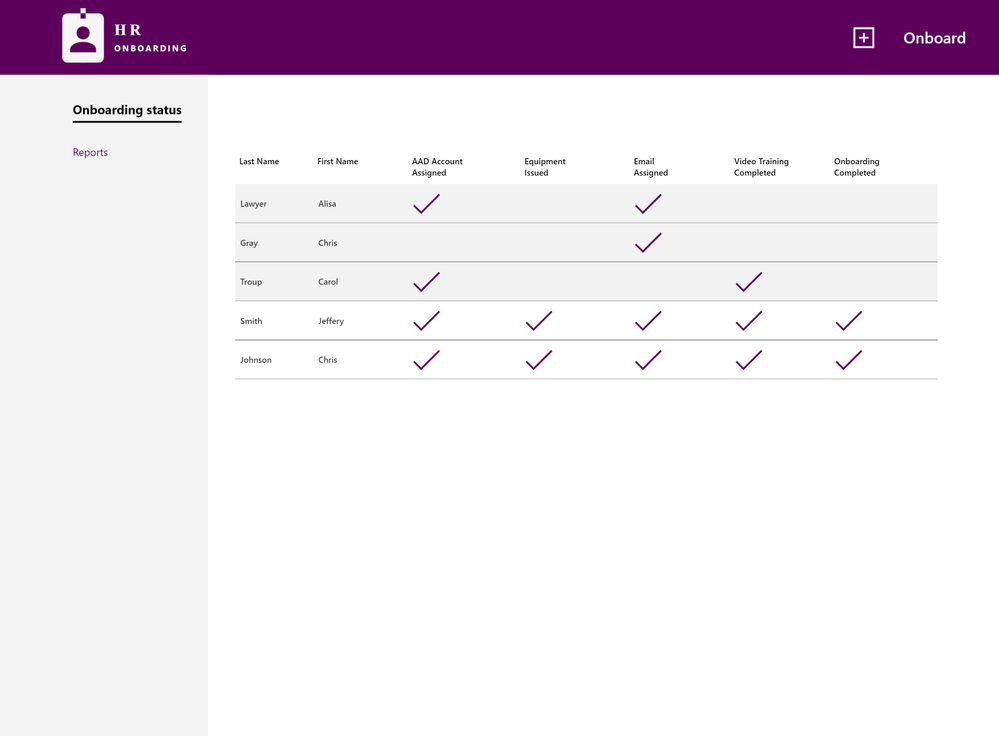 Employee Onboarding
Employee Onboarding
Conclusion
Business apps are essential to transforming processes in every organization’s journey to digital transformation. Our new white paper and templates provide a road map for learning and adopting these solutions in your organization. We look forward to learning more about your experience here on the TechCommunity.
White Paper
Microsoft 365 provides innovative capabilities to empower anyone – developers, power users, and information workers – to craft business applications tailored to real-world needs.
SharePoint lists provide foundational data storage across the suite. PowerApps and Microsoft Flow bring custom forms and workflow into business applications. And Microsoft Forms and Power BI extend business apps with data gathering and analytics.
That’s a lot of power. If you’re a problem solver, you’re in the right place. Our new white paper “Transforming Business Process with Microsoft 365” helps you understand these capabilities. You’ll learn about why business apps matter. We review the core capabilities of each tool – SharePoint lists, PowerApps, Flow, Forms, and Power BI. Finally, we complete the journey by presenting three scenarios to guide your implementation:
- Event organizer
- Travel approval
- Employee onboarding
Each solution is accompanied by templates you can use immediately. Download the white paper today to start this journey.
Solutions
We also know that there’s no substitute for learning by doing. That’s why our white paper is accompanied by three downloadable scenario templates. Each includes setup scripts, PowerApps, Flow, and other tools, along with videos and step by step instructions to help you bring each of these solutions to life in your own environment.
These solutions take their place alongside the other templates already published on the TechCommunity Resource Center. Let’s take a look.
Event organizer
This solution allows you to invitee attendees to self-register for an event using Microsoft Forms. Registrations are tracked in a SharePoint list, which can be deployed automatically using our site scripts included in the solution. Microsoft Flow is used to provide alerts , confirmations, and reminders about the event to attendees and staff. Power BI is used for real-time reporting on attendee registrations and attendance. Finally, this solution includes mobile and tablet versions of our PowerApps solution for checking in and managing attendees on the day of the event. Download the template and get started.
 Event Organizer
Event Organizer
Travel Approval
Travel is a critical part of business operations. This solution allows employees to easily submit travel requests from desktop or mobile devices using PowerApps. Requests are automatically routed using Flow to the appropriate manager and travel department for approval. Managers can also access Power BI based status reports for all travel requests to verify current status and manage budgets. Get started with our downloadable template.
 Travel Requests
Travel Requests
Employee onboarding
The Employee Onboarding app is designed to streamline and simplify the process of bringing a new employee onboard into the organization. In many organizations, onboarding new employees can be a complicated and laborious process. This solution integrates PowerApps, SharePoint and Flow to manage procurement, logins, email and training tasks for new staff. Download our template to get started today.
 Employee Onboarding
Employee Onboarding
Conclusion
Business apps are essential to transforming processes in every organization’s journey to digital transformation. Our new white paper and templates provide a road map for learning and adopting these solutions in your organization. We look forward to learning more about your experience here on the TechCommunity.
We are happy to announce Microsoft Graph Security connectors for Azure Logic Apps, Microsoft Flow, and PowerApps, which greatly simplify the development of automated security workflows. By building playbooks that use the Microsoft Graph Security connector, you can automate common security tasks across multiple security solutions. This reduces the time and resources required to triage, investigate, and remediate security alerts, without the cost and complexity of building and maintaining multiple integrations. For further details on integrating with the Microsoft Graph Security API, learn about the API and access the schema.
Getting Started
Use these connectors now in your existing workflows or create new workflows. The steps are similar for Azure Logic Apps, Flow, and PowerApps. We’ll use Azure Logic Apps as an example here. Refer to the documentation and connector reference for further details.
- Your Azure Active Directory (AD) tenant administrator must first grant consent for the connector; follow the steps in the connector documentation.
- Sign in to the Azure portal, and open a new or an existing Logic App in Logic App Designer.
- For a blank Logic App, first start with a trigger, such as the Recurrence trigger. For existing Logic Apps, add an action to the end of a workflow by clicking ‘+ Next Step’ or between steps by clicking the (+) sign and selecting ‘Add an action’.
- Search for “Microsoft graph security” and select an action from the list.
- Provide the necessary details for your selected action and continue building your Logic App workflow.
Supported Actions
The Microsoft Graph Security connectors enable the following actions:
- Get alerts – Use this action to get a list of alerts filtered on one or more alert properties. For example, get a list of alerts with Provider equals Azure Security Center or Palo Alto Networks.
- Get alert by ID – Use this action to get a specific alert by alert id property.
- Update alert – Update a specific alert by specifying the alert id property. Refer to the list of the editable properties of alerts to ensure required and editable properties are passed in your request. For example, you can update alert assigned to property to assign the alert to a security analyst for investigations.
- Create subscriptions – Use this action to create a Graph webhook subscription that notifies you of any changes, filtered to certain types of alerts you are interested in. For example, you can create a subscription that notifies you of high severity alerts.
- Get active subscriptions – Use this action to get a list of unexpired subscriptions to manage the list of subscriptions
- Update subscription – Update your subscription by specifying the subscription id. For example, you can update the expirationDateTime property of the subscription to extend the subscription.
- Delete subscription – Delete your subscription by specifying the subscription id.
User Scenarios
You can mash up the Microsoft Graph Security connector with the 200+ Microsoft and non-Microsoft connectors available for Azure Logic Apps, Flow and PowerApps to build end-to-end scenarios based on your requirements. We have provided a few examples of scenarios that can be enabled using the Microsoft Graph Security and other connectors.
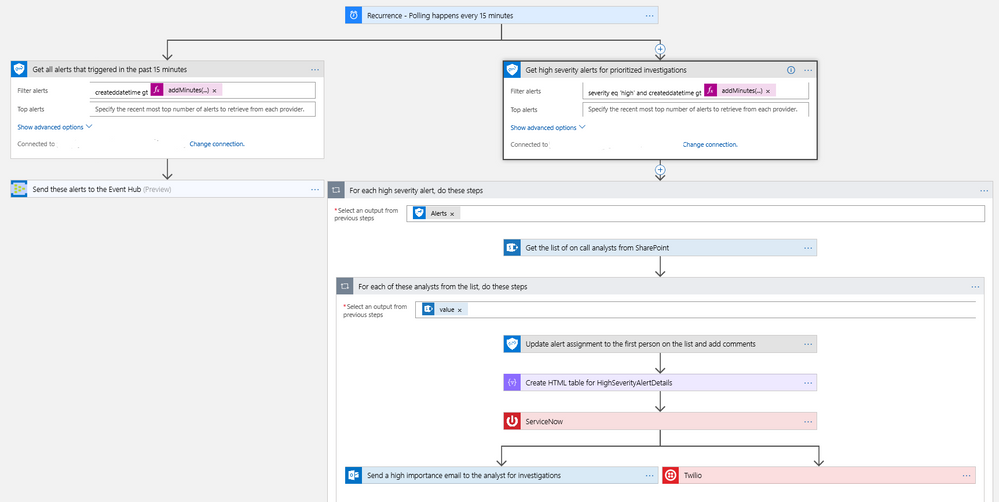
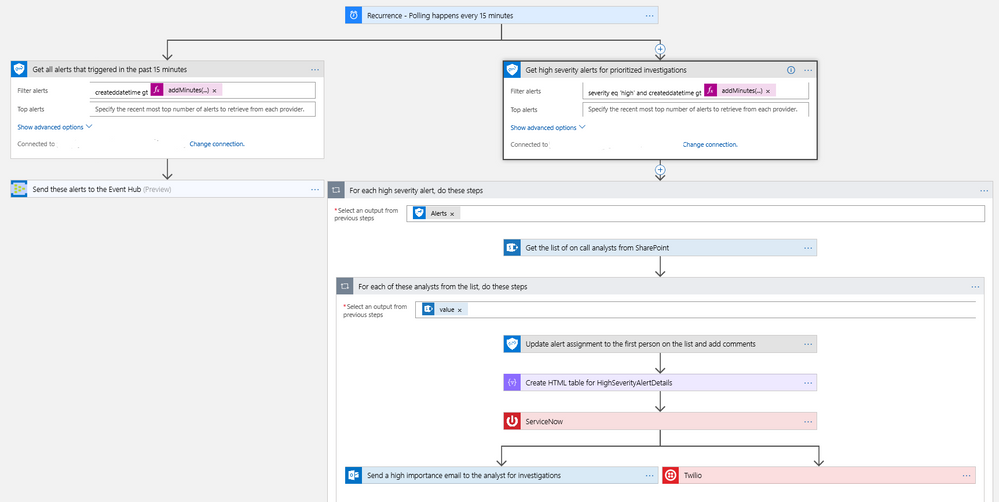
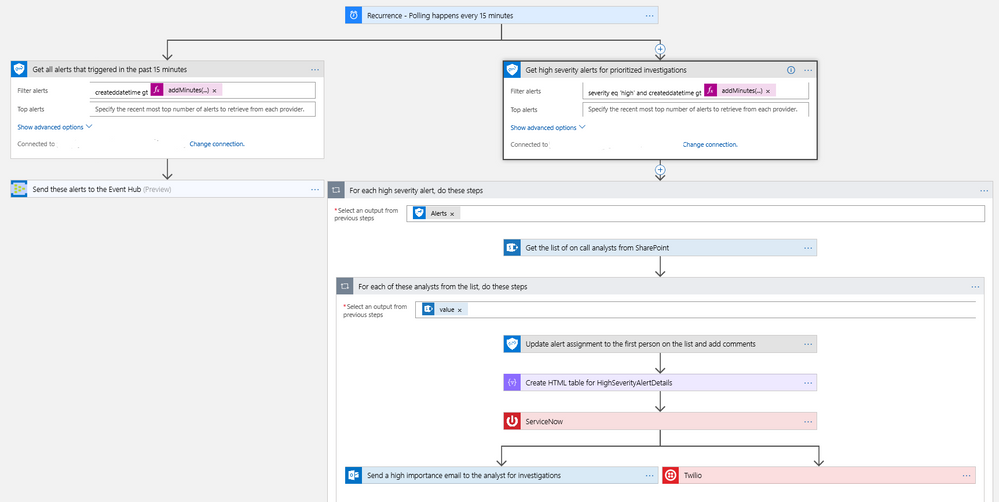
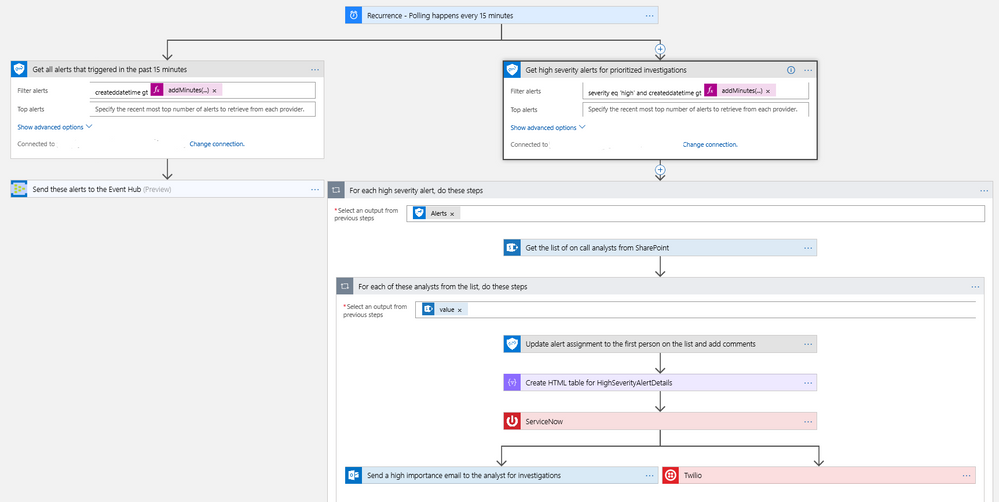
Automating Security Monitoring and Management
It’s always been a challenge to get notified of critical alerts that needs immediate action in an automated manner. At the same time, not all alerts are of equal priority and needs to be handled differently for optimal security management. You can now use the Microsoft Graph Security connector to get your high severity alerts across various security products like Azure Security Center, Windows Defender ATP, Palo Alto Networks, etc. and route those for immediate action. This example workflow below segregates alerts based on severity and routes high severity alerts for investigations.
- This workflow starts with a Recurrence trigger set for polling every 15 minutes. Two workflows kick off in parallel.
- Refer to the left branch.
- Refer to the right branch.
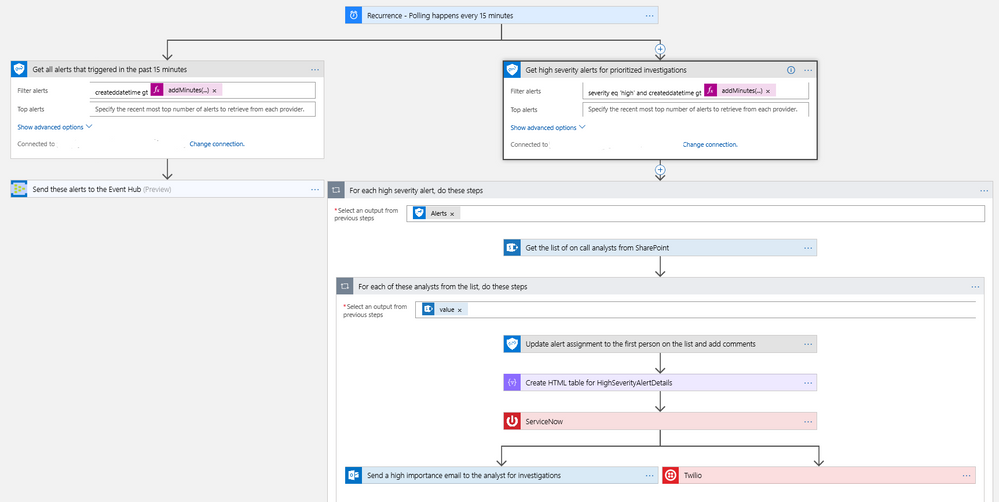 Diagram 1 – Automate Security Monitoring and Management
Diagram 1 – Automate Security Monitoring and Management
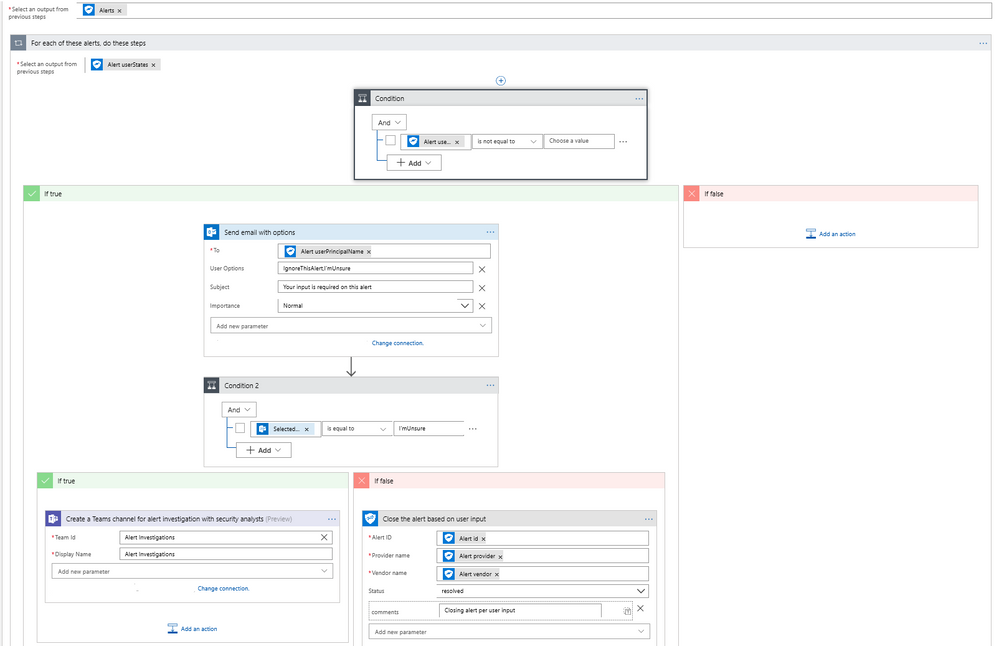
Automating Security Response Handling
To reduce the workload of security analysts, alerts about suspicious user actions, such as logging in from unusual locations or atypical data access, can be investigated further and in some cases automatically resolved with input from the user in question. An example workflow for this using the Microsoft Graph Security Connector is as follows.
- The workflow starts with a Recurrence trigger like the previous examples.
- For each new alert, check for a user principal name. If present, use the Outlook connector to email the user asking them to provide feedback about the alert, such as IgnoreThisAlert if the activity was legitimate or I’mUnsure if it’s not known.
- If the user responds as I’mUnsure, further investigation of the alert is needed; initiate a Teams channel with the security analysts for further investigations using the Microsoft Teams connector. This can be supplemented by SMS, etc. as well as covered in the earlier example.
- If the user responds as IgnoreThisAlert, update the alert status to closed using the Microsoft Graph Security connector and add comments to track resolution based on user input.
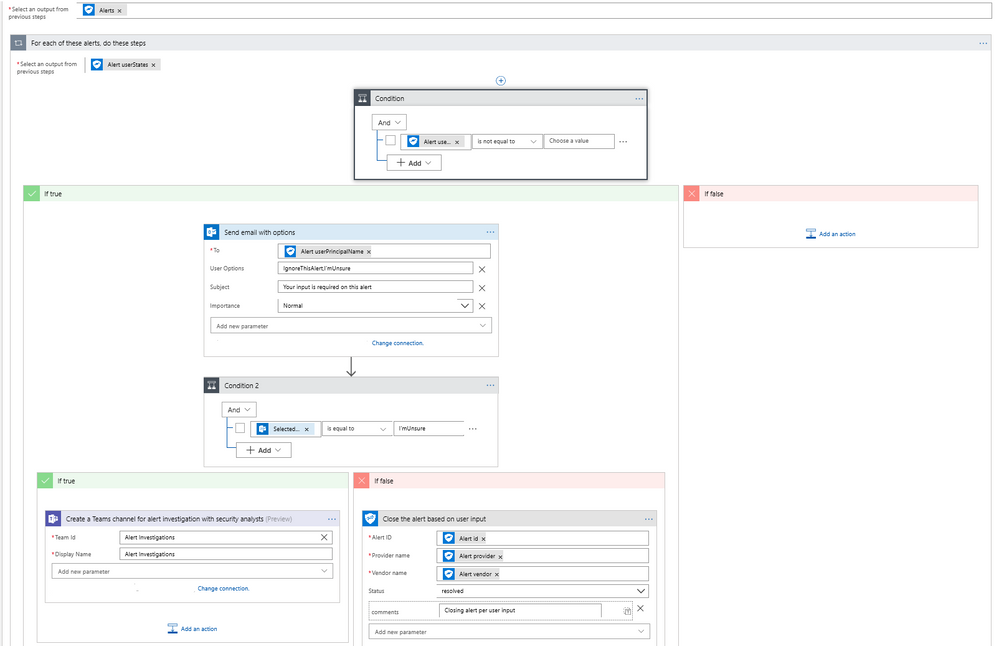 Diagram 2 – Automate Security Response Handling
Diagram 2 – Automate Security Response Handling
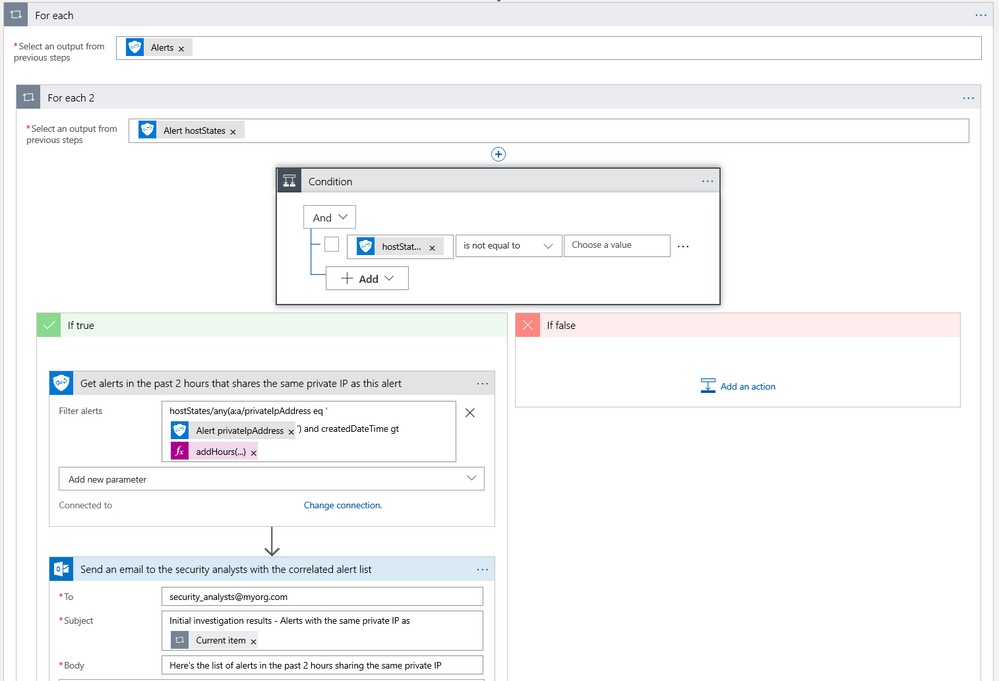
Automating Security Investigations
The often-manual process of correlating related alerts during an investigation can be automated using the Microsoft Graph Security connector. In this example workflow, all recent alerts for the host IP being investigated are automatically collected. This same example can be leveraged to find alerts for a specific file, user, or process user under investigation or other alert properties.
- The workflow starts with a Recurrence trigger like the previous examples.
- For each high severity alert, check for a host private IP address. If available, compare the address with that of all alerts generated in the past 2 hours using the Microsoft Graph Security connector.
- Email a list of related alerts to the security analyst team for investigation using the Outlook connector.
 Diagram 3 – Automate Security Investigations
Diagram 3 – Automate Security Investigations
What’s Next?
We are working on templates for the Microsoft Graph Security connector to simplify the process of building your security playbooks. Fill out the feedback form to help us design templates for the workflows you need most.
Try the Microsoft Graph Security connector and please share your feedback by filing a GitHub issue or by engaging on the Microsoft Security Graph API tech community or StackOverflow.
We are happy to announce Microsoft Graph Security connectors for Azure Logic Apps, Microsoft Flow, and PowerApps, which greatly simplify the development of automated security workflows. By building playbooks that use the Microsoft Graph Security connector, you can automate common security tasks across multiple security solutions. This reduces the time and resources required to triage, investigate, and remediate security alerts, without the cost and complexity of building and maintaining multiple integrations. For further details on integrating with the Microsoft Graph Security API, learn about the API and access the schema.
Getting Started
Use these connectors now in your existing workflows or create new workflows. The steps are similar for Azure Logic Apps, Flow, and PowerApps. We’ll use Azure Logic Apps as an example here. Refer to the documentation and connector reference for further details.
- Your Azure Active Directory (AD) tenant administrator must first grant consent for the connector; follow the steps in the connector documentation.
- Sign in to the Azure portal, and open a new or an existing Logic App in Logic App Designer.
- For a blank Logic App, first start with a trigger, such as the Recurrence trigger. For existing Logic Apps, add an action to the end of a workflow by clicking ‘+ Next Step’ or between steps by clicking the (+) sign and selecting ‘Add an action’.
- Search for “Microsoft graph security” and select an action from the list.
- Provide the necessary details for your selected action and continue building your Logic App workflow.
Supported Actions
The Microsoft Graph Security connectors enable the following actions:
- Get alerts – Use this action to get a list of alerts filtered on one or more alert properties. For example, get a list of alerts with Provider equals Azure Security Center or Palo Alto Networks.
- Get alert by ID – Use this action to get a specific alert by alert id property.
- Update alert – Update a specific alert by specifying the alert id property. Refer to the list of the editable properties of alerts to ensure required and editable properties are passed in your request. For example, you can update alert assigned to property to assign the alert to a security analyst for investigations.
- Create subscriptions – Use this action to create a Graph webhook subscription that notifies you of any changes, filtered to certain types of alerts you are interested in. For example, you can create a subscription that notifies you of high severity alerts.
- Get active subscriptions – Use this action to get a list of unexpired subscriptions to manage the list of subscriptions
- Update subscription – Update your subscription by specifying the subscription id. For example, you can update the expirationDateTime property of the subscription to extend the subscription.
- Delete subscription – Delete your subscription by specifying the subscription id.
User Scenarios
You can mash up the Microsoft Graph Security connector with the 200+ Microsoft and non-Microsoft connectors available for Azure Logic Apps, Flow and PowerApps to build end-to-end scenarios based on your requirements. We have provided a few examples of scenarios that can be enabled using the Microsoft Graph Security and other connectors.
Automating Security Monitoring and Management
It’s always been a challenge to get notified of critical alerts that needs immediate action in an automated manner. At the same time, not all alerts are of equal priority and needs to be handled differently for optimal security management. You can now use the Microsoft Graph Security connector to get your high severity alerts across various security products like Azure Security Center, Windows Defender ATP, Palo Alto Networks, etc. and route those for immediate action. This example workflow below segregates alerts based on severity and routes high severity alerts for investigations.
- This workflow starts with a Recurrence trigger set for polling every 15 minutes. Two workflows kick off in parallel.
- Refer to the left branch.
- Refer to the right branch.
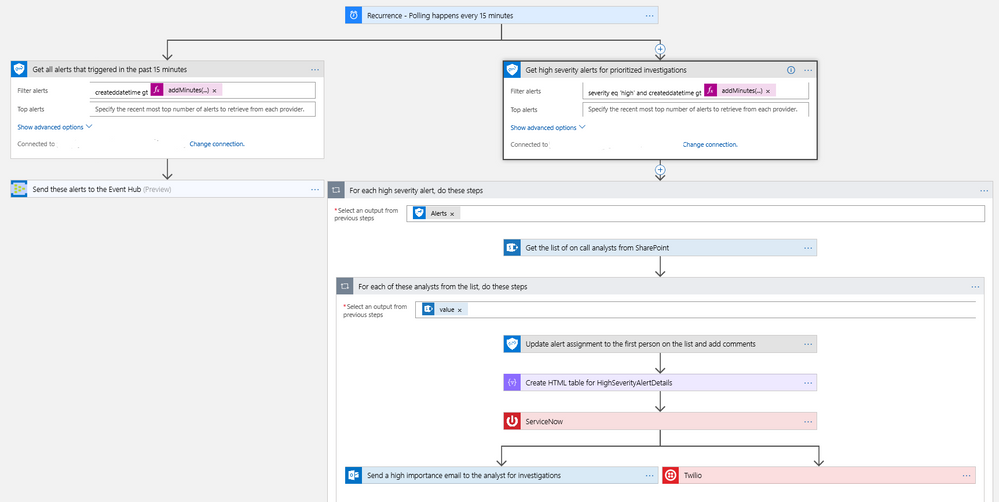 Diagram 1 – Automate Security Monitoring and Management
Diagram 1 – Automate Security Monitoring and Management
Automating Security Response Handling
To reduce the workload of security analysts, alerts about suspicious user actions, such as logging in from unusual locations or atypical data access, can be investigated further and in some cases automatically resolved with input from the user in question. An example workflow for this using the Microsoft Graph Security Connector is as follows.
- The workflow starts with a Recurrence trigger like the previous examples.
- For each new alert, check for a user principal name. If present, use the Outlook connector to email the user asking them to provide feedback about the alert, such as IgnoreThisAlert if the activity was legitimate or I’mUnsure if it’s not known.
- If the user responds as I’mUnsure, further investigation of the alert is needed; initiate a Teams channel with the security analysts for further investigations using the Microsoft Teams connector. This can be supplemented by SMS, etc. as well as covered in the earlier example.
- If the user responds as IgnoreThisAlert, update the alert status to closed using the Microsoft Graph Security connector and add comments to track resolution based on user input.
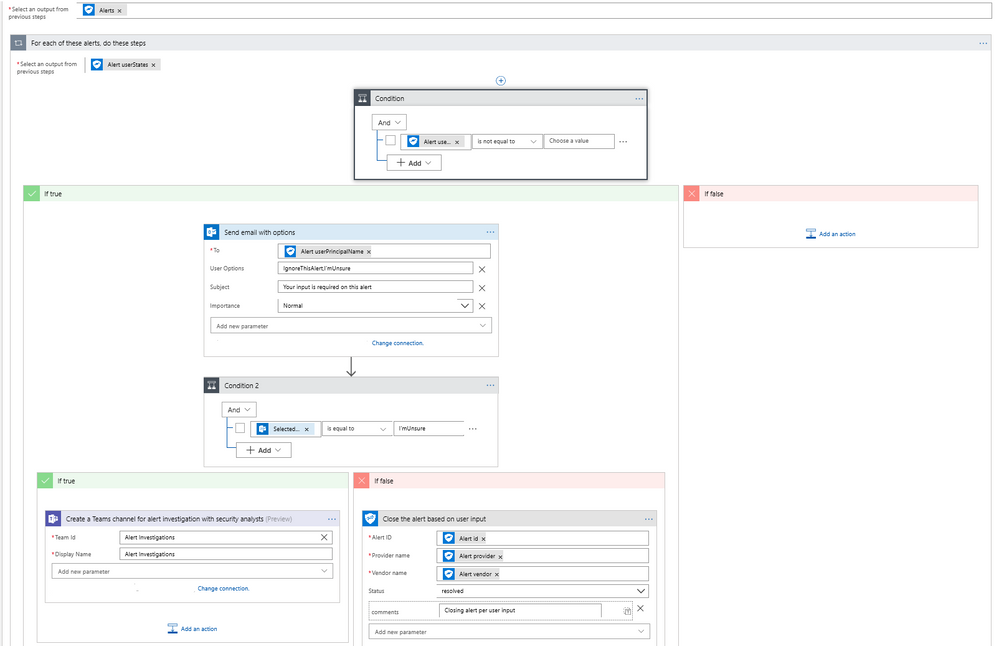 Diagram 2 – Automate Security Response Handling
Diagram 2 – Automate Security Response Handling
Automating Security Investigations
The often-manual process of correlating related alerts during an investigation can be automated using the Microsoft Graph Security connector. In this example workflow, all recent alerts for the host IP being investigated are automatically collected. This same example can be leveraged to find alerts for a specific file, user, or process user under investigation or other alert properties.
- The workflow starts with a Recurrence trigger like the previous examples.
- For each high severity alert, check for a host private IP address. If available, compare the address with that of all alerts generated in the past 2 hours using the Microsoft Graph Security connector.
- Email a list of related alerts to the security analyst team for investigation using the Outlook connector.
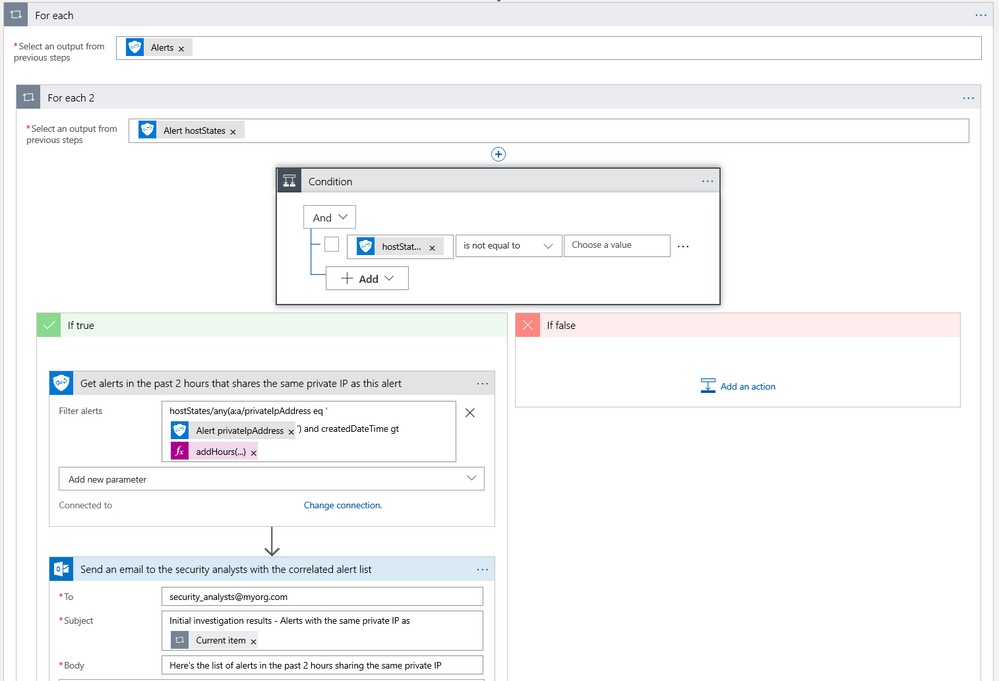 Diagram 3 – Automate Security Investigations
Diagram 3 – Automate Security Investigations
What’s Next?
We are working on templates for the Microsoft Graph Security connector to simplify the process of building your security playbooks. Fill out the feedback form to help us design templates for the workflows you need most.
Try the Microsoft Graph Security connector and please share your feedback by filing a GitHub issue or by engaging on the Microsoft Security Graph API tech community or StackOverflow.
We are happy to announce Microsoft Graph Security connectors for Azure Logic Apps, Microsoft Flow, and PowerApps, which greatly simplify the development of automated security workflows. By building playbooks that use the Microsoft Graph Security connector, you can automate common security tasks across multiple security solutions. This reduces the time and resources required to triage, investigate, and remediate security alerts, without the cost and complexity of building and maintaining multiple integrations. For further details on integrating with the Microsoft Graph Security API, learn about the API and access the schema.
Getting Started
Use these connectors now in your existing workflows or create new workflows. The steps are similar for Azure Logic Apps, Flow, and PowerApps. We’ll use Azure Logic Apps as an example here. Refer to the documentation and connector reference for further details.
- Your Azure Active Directory (AD) tenant administrator must first grant consent for the connector; follow the steps in the connector documentation.
- Sign in to the Azure portal, and open a new or an existing Logic App in Logic App Designer.
- For a blank Logic App, first start with a trigger, such as the Recurrence trigger. For existing Logic Apps, add an action to the end of a workflow by clicking ‘+ Next Step’ or between steps by clicking the (+) sign and selecting ‘Add an action’.
- Search for “Microsoft graph security” and select an action from the list.
- Provide the necessary details for your selected action and continue building your Logic App workflow.
Supported Actions
The Microsoft Graph Security connectors enable the following actions:
- Get alerts – Use this action to get a list of alerts filtered on one or more alert properties. For example, get a list of alerts with Provider equals Azure Security Center or Palo Alto Networks.
- Get alert by ID – Use this action to get a specific alert by alert id property.
- Update alert – Update a specific alert by specifying the alert id property. Refer to the list of the editable properties of alerts to ensure required and editable properties are passed in your request. For example, you can update alert assigned to property to assign the alert to a security analyst for investigations.
- Create subscriptions – Use this action to create a Graph webhook subscription that notifies you of any changes, filtered to certain types of alerts you are interested in. For example, you can create a subscription that notifies you of high severity alerts.
- Get active subscriptions – Use this action to get a list of unexpired subscriptions to manage the list of subscriptions
- Update subscription – Update your subscription by specifying the subscription id. For example, you can update the expirationDateTime property of the subscription to extend the subscription.
- Delete subscription – Delete your subscription by specifying the subscription id.
User Scenarios
You can mash up the Microsoft Graph Security connector with the 200+ Microsoft and non-Microsoft connectors available for Azure Logic Apps, Flow and PowerApps to build end-to-end scenarios based on your requirements. We have provided a few examples of scenarios that can be enabled using the Microsoft Graph Security and other connectors.
Automating Security Monitoring and Management
It’s always been a challenge to get notified of critical alerts that needs immediate action in an automated manner. At the same time, not all alerts are of equal priority and needs to be handled differently for optimal security management. You can now use the Microsoft Graph Security connector to get your high severity alerts across various security products like Azure Security Center, Windows Defender ATP, Palo Alto Networks, etc. and route those for immediate action. This example workflow below segregates alerts based on severity and routes high severity alerts for investigations.
- This workflow starts with a Recurrence trigger set for polling every 15 minutes. Two workflows kick off in parallel.
- Refer to the left branch.
- Refer to the right branch.
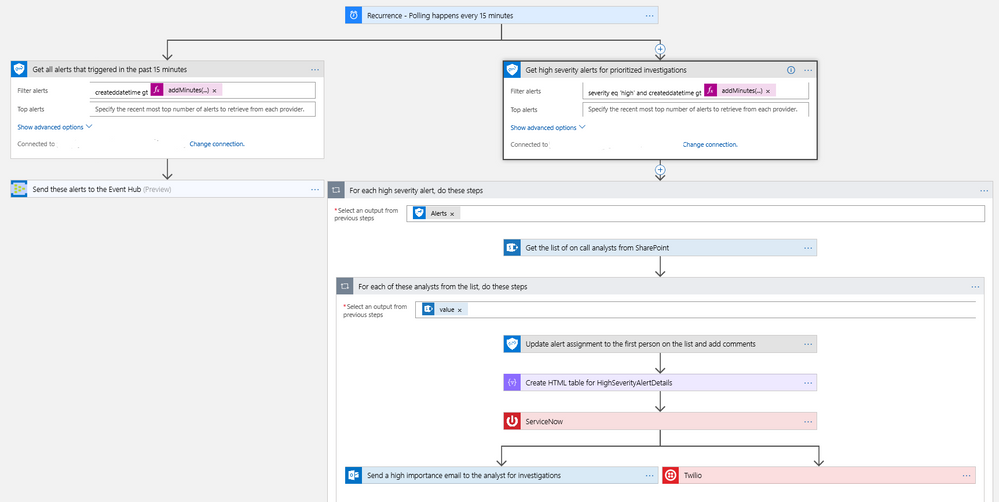 Diagram 1 – Automate Security Monitoring and Management
Diagram 1 – Automate Security Monitoring and Management
Automating Security Response Handling
To reduce the workload of security analysts, alerts about suspicious user actions, such as logging in from unusual locations or atypical data access, can be investigated further and in some cases automatically resolved with input from the user in question. An example workflow for this using the Microsoft Graph Security Connector is as follows.
- The workflow starts with a Recurrence trigger like the previous examples.
- For each new alert, check for a user principal name. If present, use the Outlook connector to email the user asking them to provide feedback about the alert, such as IgnoreThisAlert if the activity was legitimate or I’mUnsure if it’s not known.
- If the user responds as I’mUnsure, further investigation of the alert is needed; initiate a Teams channel with the security analysts for further investigations using the Microsoft Teams connector. This can be supplemented by SMS, etc. as well as covered in the earlier example.
- If the user responds as IgnoreThisAlert, update the alert status to closed using the Microsoft Graph Security connector and add comments to track resolution based on user input.
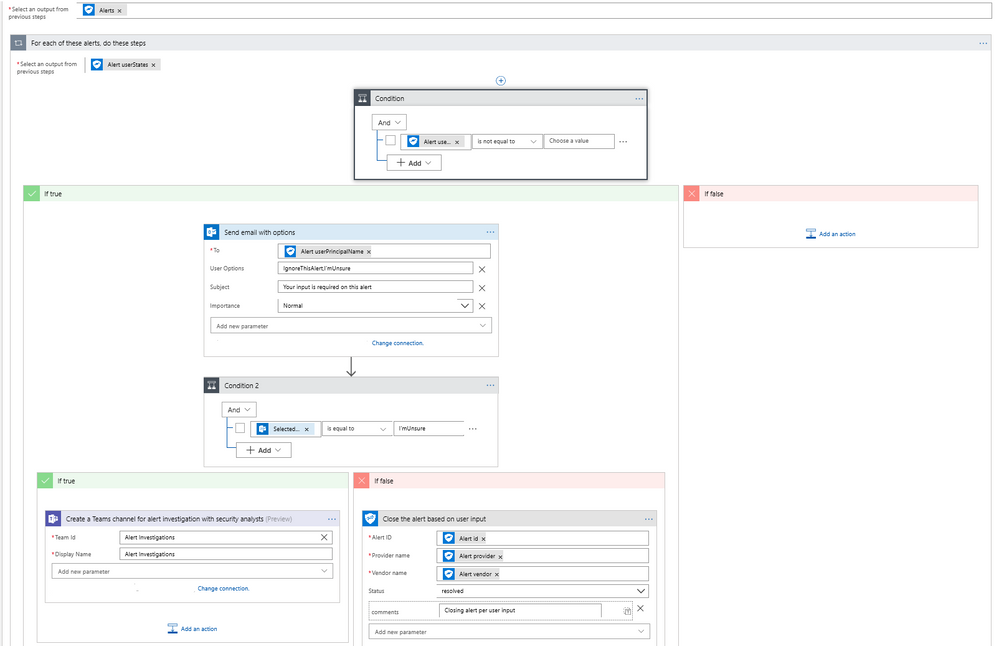 Diagram 2 – Automate Security Response Handling
Diagram 2 – Automate Security Response Handling
Automating Security Investigations
The often-manual process of correlating related alerts during an investigation can be automated using the Microsoft Graph Security connector. In this example workflow, all recent alerts for the host IP being investigated are automatically collected. This same example can be leveraged to find alerts for a specific file, user, or process user under investigation or other alert properties.
- The workflow starts with a Recurrence trigger like the previous examples.
- For each high severity alert, check for a host private IP address. If available, compare the address with that of all alerts generated in the past 2 hours using the Microsoft Graph Security connector.
- Email a list of related alerts to the security analyst team for investigation using the Outlook connector.
 Diagram 3 – Automate Security Investigations
Diagram 3 – Automate Security Investigations
What’s Next?
We are working on templates for the Microsoft Graph Security connector to simplify the process of building your security playbooks. Fill out the feedback form to help us design templates for the workflows you need most.
Try the Microsoft Graph Security connector and please share your feedback by filing a GitHub issue or by engaging on the Microsoft Security Graph API tech community or StackOverflow.