It has been a busy few weeks since we previewed the new Secure Score API. While the team was working on this, they also were working on another common request, support for additional controls. In particular we heard that you wanted controls from the Enterprise Mobility + Security (EMS) suite. As you might have seen in the Microsoft Secure Blog we are expanding Secure Score to support additional EMS solutions and are happy to share that we have new controls for Microsoft Cloud App Security and additional controls for Azure Active Directory (Azure AD).
Azure AD Controls
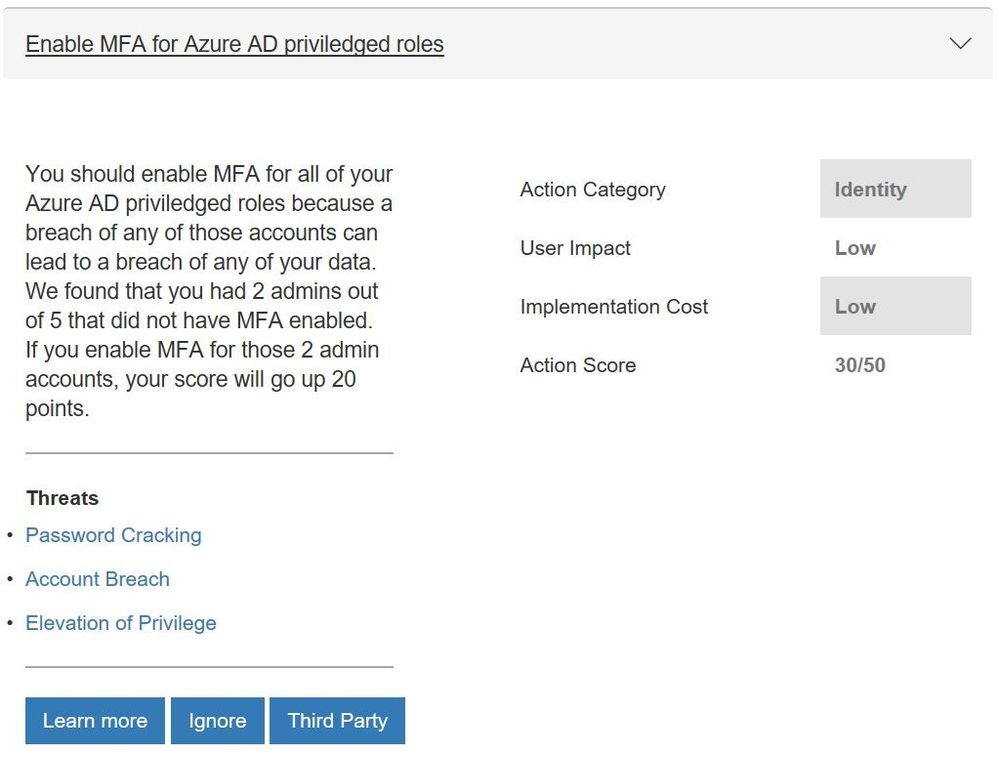
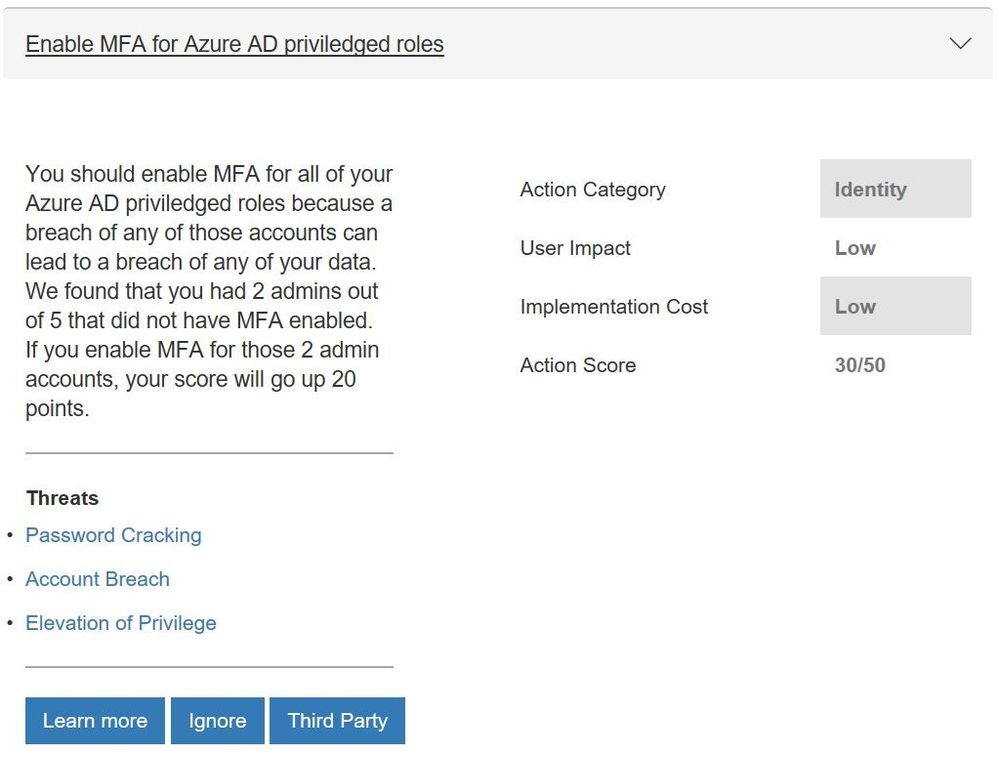
We have seen the feedback from many of you that you wanted support for additional Azure Active Directory (Azure AD) controls to help you manage user identities and create intelligence-driven access policies to secure your resources. In particular you wanted the multifactor authentication (MFA) controls to support conditional access. Working with the Azure AD team this is now available and 8 more controls which include:
- Enabling self-service password reset that helps empower users and reduce help desk costs
- Require just in time access for global administrators using Privileged Identity Management
- Turning on password hash sync which helps you leverage the same password you use to sign in to your on-premises Active Directory for Azure AD services
- Enable user risk policies that can block access or require a user to use MFA to login in when there is a likelihood that a user’s identity has been compromised
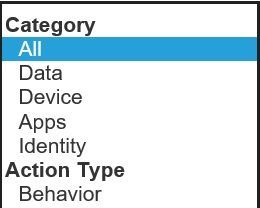
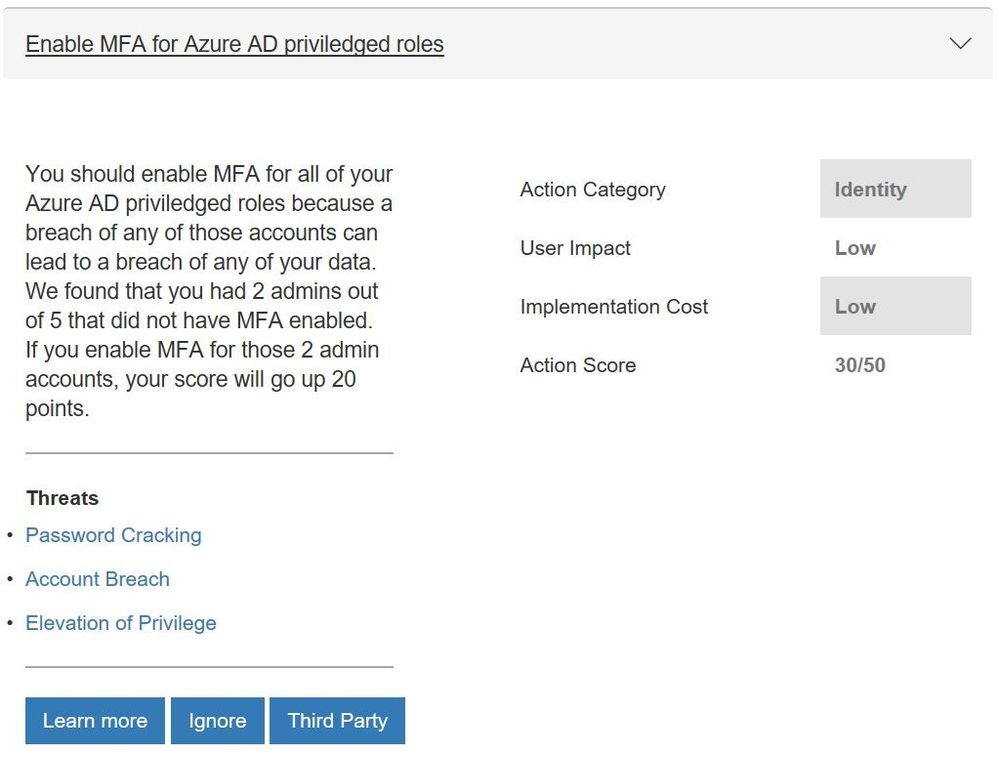
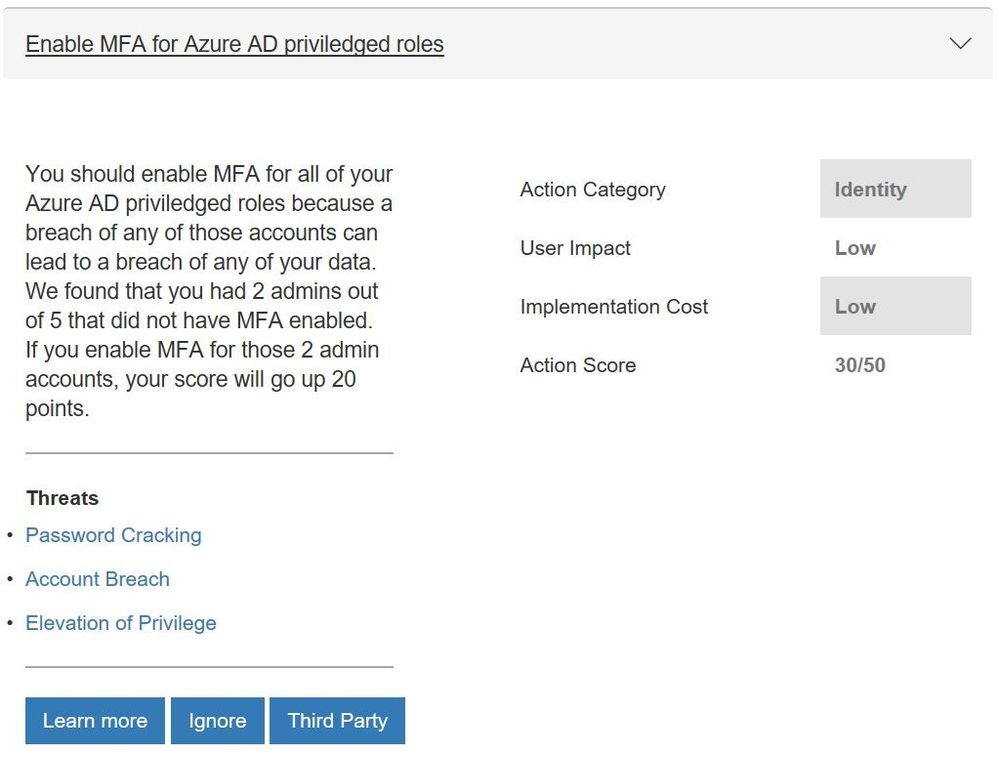 Updated control for Azure AD multi-factor authentication
Updated control for Azure AD multi-factor authentication
Microsoft Cloud App Security Controls
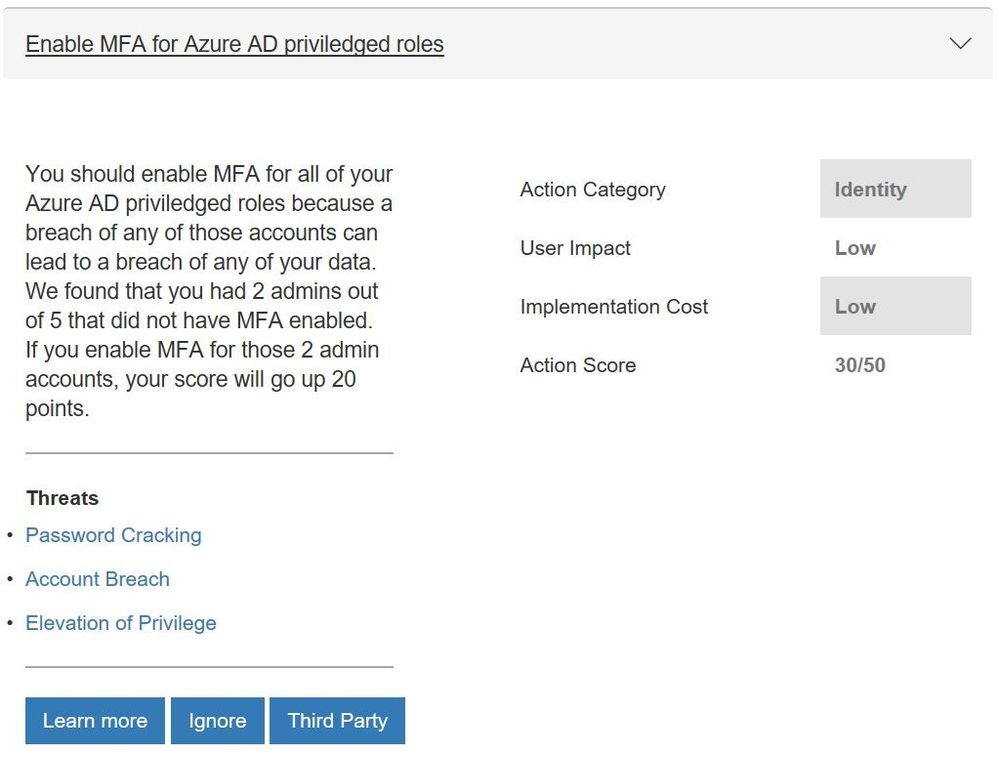
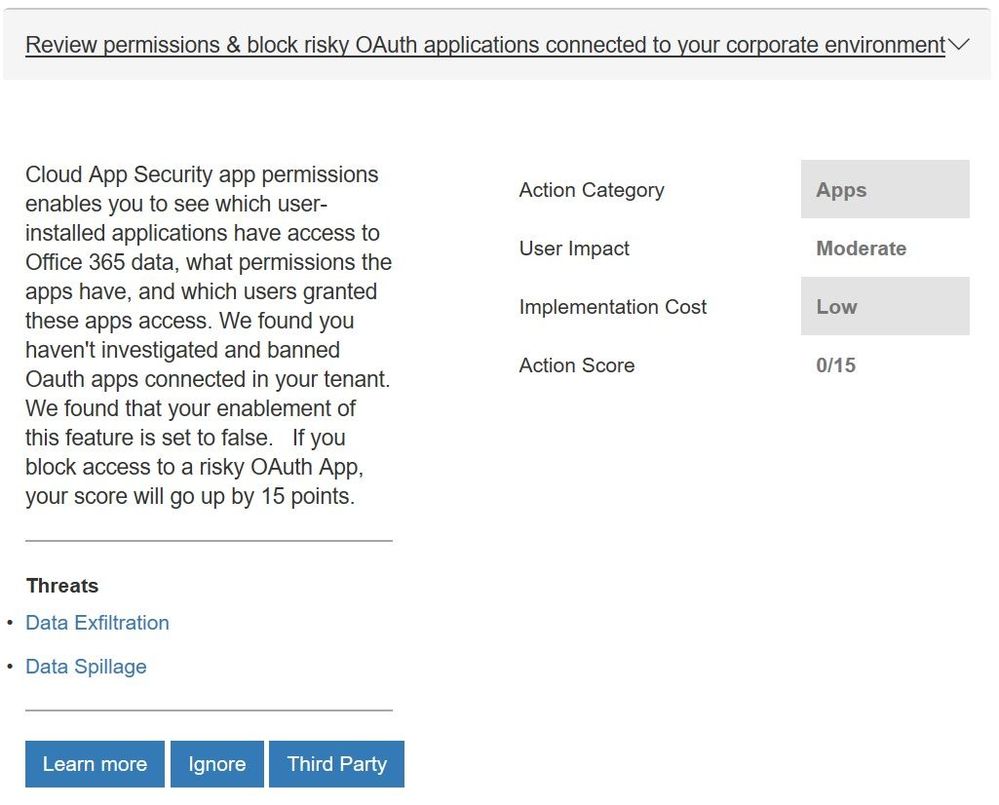
More and more organizations are adopting SaaS apps, not only to reduce costs but also to unlock competitive advantages such as faster time to market and improved collaboration. Even if your company hasn’t embraced cloud applications, your employees are probably using them. Microsoft Cloud App Security is our cloud access security broker that gives you visibility into your cloud apps and services, provides sophisticated analytics to identify and combat cyberthreats and enables you to control how your data travels. If you are taking advantage of the solution, you will now get points for actions like:
- Reviewing permissions and blocking risky OAuth applications that your users have installed and have access to Office 365 data
- Reviewing anomaly detection policies that help you understand if users are logging in from locations that they normally don’t log in from, using anonymous IP addresses, and have multiple failed login attempts
- Discover risky and non-compliant Shadow IT applications used in your organization through the Cloud Discovery Dashboard and automatic uploading of your firewall/proxy logs
- Creating custom activity policies to discover risky behavior in cloud apps like a mass downloads of data.
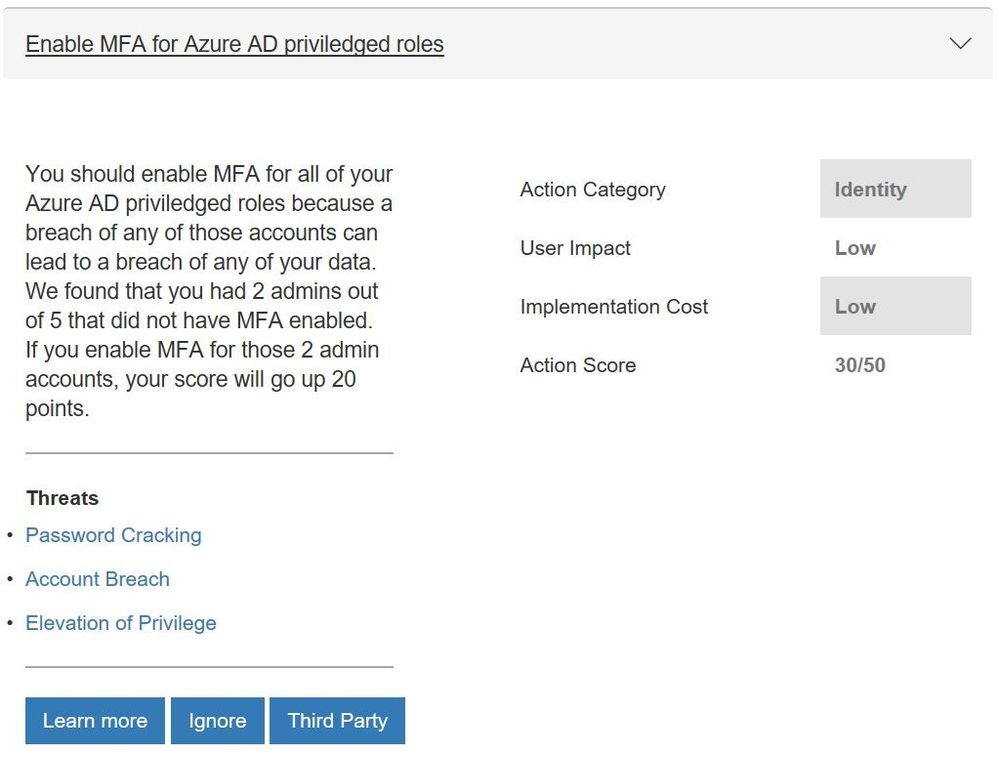
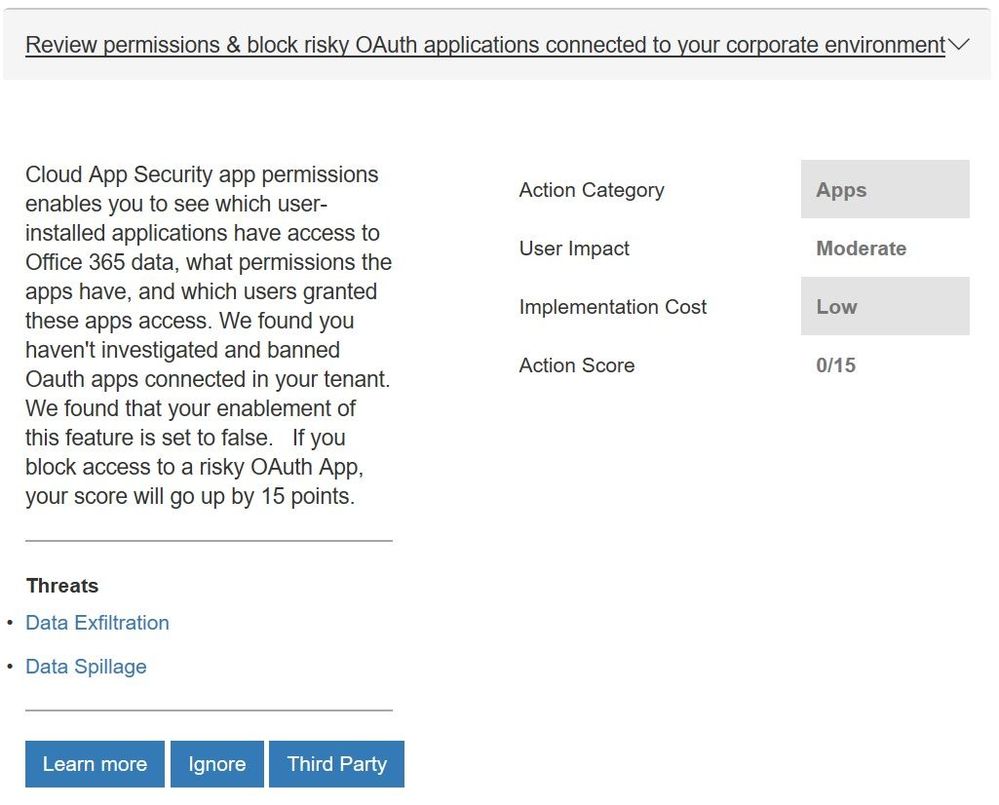 New control from Microsoft Cloud App Security
New control from Microsoft Cloud App Security
We will be looking to add more controls in the future. For example, we will look to add controls from Azure Security Center as they have launched a public preview of their own score.
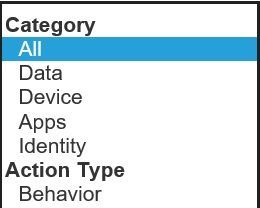
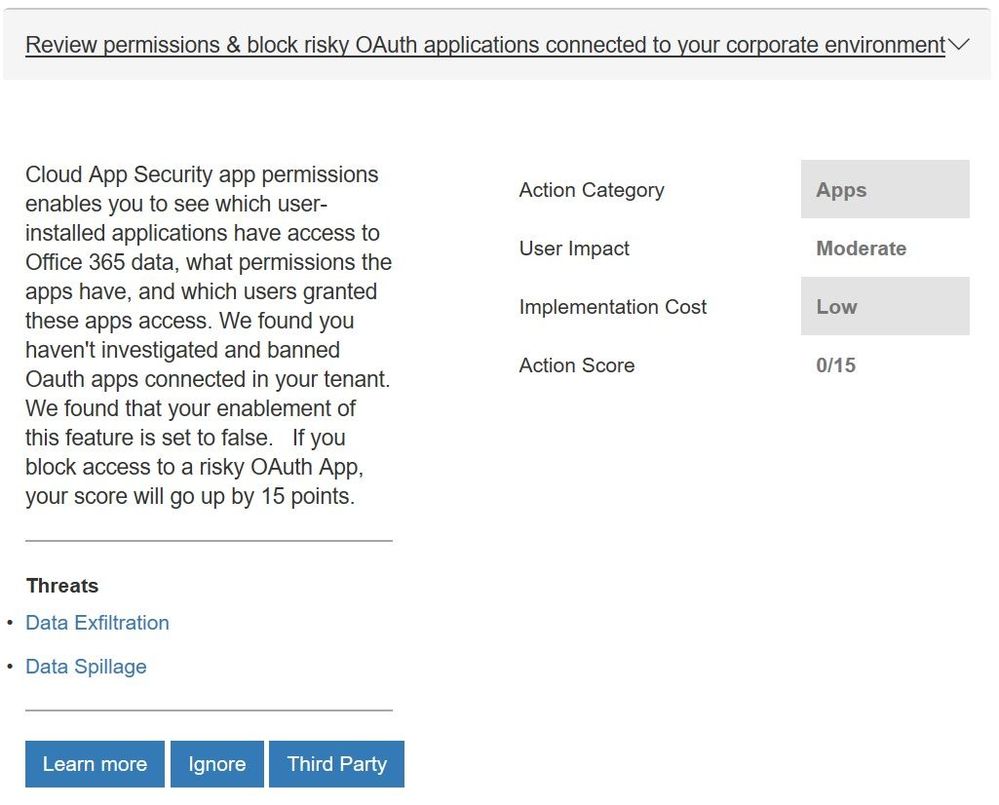
With all the new controls we are rethinking how we show the points you have obtained. Today we display the overall Microsoft Secure Score and the points by solution (Office 365 and Windows). With the addition of controls from EMS and eventually Azure Security Center, along with the fact that organizations have told us that they think about their environment more broadly then just solutions, this approach will be less effective in helping you understand your security posture. To help solve this, in the future we will move to a category view that will show a score for controls that focus on identity, apps, data, devices, and infrastructure. You can see the beginnings of this change in the filter box within the “Take Action, Improve Your Microsoft Secure Score” section of Secure Score.
 Category options to filter on in the “Take Action, Improve Your Microsoft Secure Score” section
Category options to filter on in the “Take Action, Improve Your Microsoft Secure Score” section
To see what your score looks like with the new controls, login with administrative credentials at https://securescore.microsoft.com and start thinking about which ones you will enable. We hope that these changes help you get even greater visibility into your security posture and the guidance to help you find the right level of security for your organization.
As always, feel free to leave your questions, thoughts, and comments below.
It has been a busy few weeks since we previewed the new Secure Score API. While the team was working on this, they also were working on another common request, support for additional controls. In particular we heard that you wanted controls from the Enterprise Mobility + Security (EMS) suite. As you might have seen in the Microsoft Secure Blog we are expanding Secure Score to support additional EMS solutions and are happy to share that we have new controls for Microsoft Cloud App Security and additional controls for Azure Active Directory (Azure AD).
Azure AD Controls
We have seen the feedback from many of you that you wanted support for additional Azure Active Directory (Azure AD) controls to help you manage user identities and create intelligence-driven access policies to secure your resources. In particular you wanted the multifactor authentication (MFA) controls to support conditional access. Working with the Azure AD team this is now available and 8 more controls which include:
- Enabling self-service password reset that helps empower users and reduce help desk costs
- Require just in time access for global administrators using Privileged Identity Management
- Turning on password hash sync which helps you leverage the same password you use to sign in to your on-premises Active Directory for Azure AD services
- Enable user risk policies that can block access or require a user to use MFA to login in when there is a likelihood that a user’s identity has been compromised
 Updated control for Azure AD multi-factor authentication
Updated control for Azure AD multi-factor authentication
Microsoft Cloud App Security Controls
More and more organizations are adopting SaaS apps, not only to reduce costs but also to unlock competitive advantages such as faster time to market and improved collaboration. Even if your company hasn’t embraced cloud applications, your employees are probably using them. Microsoft Cloud App Security is our cloud access security broker that gives you visibility into your cloud apps and services, provides sophisticated analytics to identify and combat cyberthreats and enables you to control how your data travels. If you are taking advantage of the solution, you will now get points for actions like:
- Reviewing permissions and blocking risky OAuth applications that your users have installed and have access to Office 365 data
- Reviewing anomaly detection policies that help you understand if users are logging in from locations that they normally don’t log in from, using anonymous IP addresses, and have multiple failed login attempts
- Discover risky and non-compliant Shadow IT applications used in your organization through the Cloud Discovery Dashboard and automatic uploading of your firewall/proxy logs
- Creating custom activity policies to discover risky behavior in cloud apps like a mass downloads of data.
 New control from Microsoft Cloud App Security
New control from Microsoft Cloud App Security
We will be looking to add more controls in the future. For example, we will look to add controls from Azure Security Center as they have launched a public preview of their own score.
With all the new controls we are rethinking how we show the points you have obtained. Today we display the overall Microsoft Secure Score and the points by solution (Office 365 and Windows). With the addition of controls from EMS and eventually Azure Security Center, along with the fact that organizations have told us that they think about their environment more broadly then just solutions, this approach will be less effective in helping you understand your security posture. To help solve this, in the future we will move to a category view that will show a score for controls that focus on identity, apps, data, devices, and infrastructure. You can see the beginnings of this change in the filter box within the “Take Action, Improve Your Microsoft Secure Score” section of Secure Score.
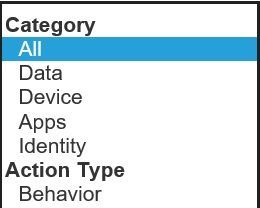 Category options to filter on in the “Take Action, Improve Your Microsoft Secure Score” section
Category options to filter on in the “Take Action, Improve Your Microsoft Secure Score” section
To see what your score looks like with the new controls, login with administrative credentials at https://securescore.microsoft.com and start thinking about which ones you will enable. We hope that these changes help you get even greater visibility into your security posture and the guidance to help you find the right level of security for your organization.
As always, feel free to leave your questions, thoughts, and comments below.

We’re facing a data explosion – changes in the way we do business have resulted in a rapid increase in the amount of data and information being collected throughout your business. As this data grows, so do the problems of managing it all. Where, or what, can you turn to for help?
Our modern business techniques require a modern approach to managing the increased data in our systems. For many, the chosen system is Office 365 – but, no matter what the system, the data still needs to be managed, governed, and supervised to provide value.
More details from the event page:
“In this webinar, AIIM’s chief evangelist John Mancini and Nishan DeSilva from Microsoft will discuss the latest ways Office 365 is providing the tools to develop and implement a modern records management strategy to take charge of the data explosion, including:
- Improved Findability: How to find and retain important data while eliminating ROT (redundant, outdated and trivial information) – with classification, archiving, retention, disposition, supervision, and more
- New Approaches to Governance: Where the Office 365 governance capabilities are today and what’s in store for the future, highlighted by the newest features and scenarios available
- Increased Business Intelligence: How machine learning algorithms can automatically or manually detect, classify sensitive data mapping to enterprise taxonomies
In addition, Nishan DeSilva will share customer use case stories that illustrate these modern approaches to the latest functionality found in Office 365. Hear how information professionals are succeeding with governing their data in Office 365. And envision how you can succeed, too.”

We’re facing a data explosion – changes in the way we do business have resulted in a rapid increase in the amount of data and information being collected throughout your business. As this data grows, so do the problems of managing it all. Where, or what, can you turn to for help?
Our modern business techniques require a modern approach to managing the increased data in our systems. For many, the chosen system is Office 365 – but, no matter what the system, the data still needs to be managed, governed, and supervised to provide value.
More details from the event page:
“In this webinar, AIIM’s chief evangelist John Mancini and Nishan DeSilva from Microsoft will discuss the latest ways Office 365 is providing the tools to develop and implement a modern records management strategy to take charge of the data explosion, including:
- Improved Findability: How to find and retain important data while eliminating ROT (redundant, outdated and trivial information) – with classification, archiving, retention, disposition, supervision, and more
- New Approaches to Governance: Where the Office 365 governance capabilities are today and what’s in store for the future, highlighted by the newest features and scenarios available
- Increased Business Intelligence: How machine learning algorithms can automatically or manually detect, classify sensitive data mapping to enterprise taxonomies
In addition, Nishan DeSilva will share customer use case stories that illustrate these modern approaches to the latest functionality found in Office 365. Hear how information professionals are succeeding with governing their data in Office 365. And envision how you can succeed, too.”

We’re facing a data explosion – changes in the way we do business have resulted in a rapid increase in the amount of data and information being collected throughout your business. As this data grows, so do the problems of managing it all. Where, or what, can you turn to for help?
Our modern business techniques require a modern approach to managing the increased data in our systems. For many, the chosen system is Office 365 – but, no matter what the system, the data still needs to be managed, governed, and supervised to provide value.
More details from the event page:
“In this webinar, AIIM’s chief evangelist John Mancini and Nishan DeSilva from Microsoft will discuss the latest ways Office 365 is providing the tools to develop and implement a modern records management strategy to take charge of the data explosion, including:
- Improved Findability: How to find and retain important data while eliminating ROT (redundant, outdated and trivial information) – with classification, archiving, retention, disposition, supervision, and more
- New Approaches to Governance: Where the Office 365 governance capabilities are today and what’s in store for the future, highlighted by the newest features and scenarios available
- Increased Business Intelligence: How machine learning algorithms can automatically or manually detect, classify sensitive data mapping to enterprise taxonomies
In addition, Nishan DeSilva will share customer use case stories that illustrate these modern approaches to the latest functionality found in Office 365. Hear how information professionals are succeeding with governing their data in Office 365. And envision how you can succeed, too.”

We’re facing a data explosion – changes in the way we do business have resulted in a rapid increase in the amount of data and information being collected throughout your business. As this data grows, so do the problems of managing it all. Where, or what, can you turn to for help?
Our modern business techniques require a modern approach to managing the increased data in our systems. For many, the chosen system is Office 365 – but, no matter what the system, the data still needs to be managed, governed, and supervised to provide value.
More details from the event page:
“In this webinar, AIIM’s chief evangelist John Mancini and Nishan DeSilva from Microsoft will discuss the latest ways Office 365 is providing the tools to develop and implement a modern records management strategy to take charge of the data explosion, including:
- Improved Findability: How to find and retain important data while eliminating ROT (redundant, outdated and trivial information) – with classification, archiving, retention, disposition, supervision, and more
- New Approaches to Governance: Where the Office 365 governance capabilities are today and what’s in store for the future, highlighted by the newest features and scenarios available
- Increased Business Intelligence: How machine learning algorithms can automatically or manually detect, classify sensitive data mapping to enterprise taxonomies
In addition, Nishan DeSilva will share customer use case stories that illustrate these modern approaches to the latest functionality found in Office 365. Hear how information professionals are succeeding with governing their data in Office 365. And envision how you can succeed, too.”
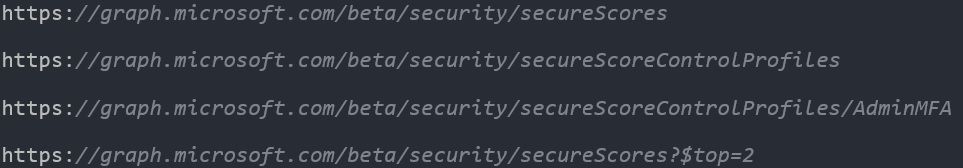
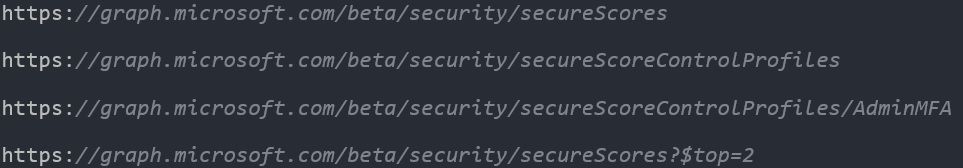
We love that the community has great discussions on Microsoft Secure Score. One of the topics we hear from you and other organizations is on the Secure Score API. This is a great way to programmatically access Secure Score data. Over the past year and a half, we have received a lot of feedback on the API and the Microsoft 365 Security Engineering team is pleased to announce the availability and preview of the new Microsoft 365 Secure Score API.
As part of building the new API we also wanted to provide it in other languages. In doing this work for the API, it also gave us localization of the Secure Score interface. The localization of the interface is starting to roll out.
What’s new?
The new API is based on much of your feedback and has a host of changes to enable new scenarios. At a high level they are:
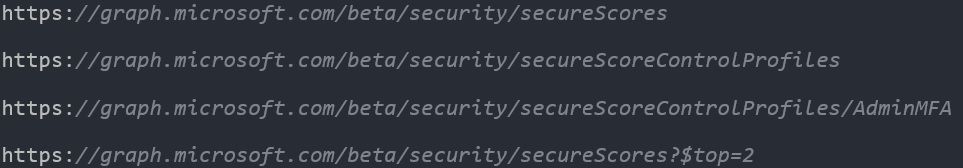
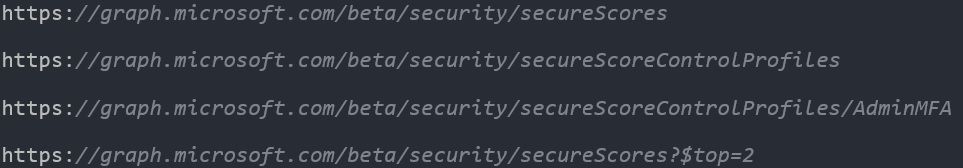
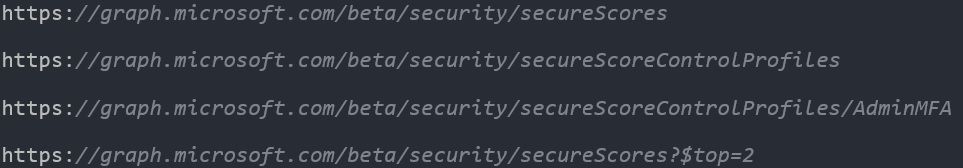
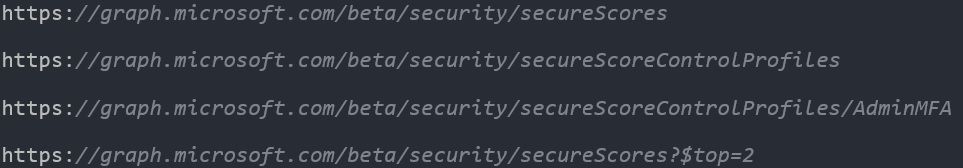
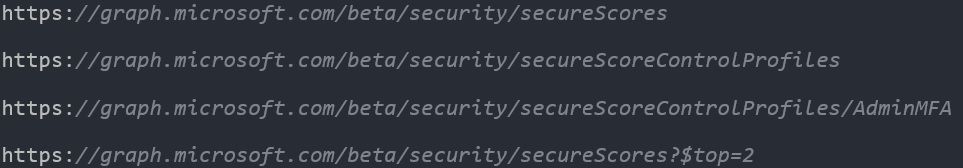
- Integrated into the Security Graph API, allowing easier permission scoping.
- Support for filtering methods such as $top=2 or explicit control access.
- Dual entities, an entity for bringing back just the score data and an entity for bringing back control metadata such as Title, Descriptions and Threats etc.
- Patch support, allowing you to flag controls as 3rd Party or Ignore.
- New fields, such as “assignedTo” and “tenantNote”.
- Support for delegated admin rights.
- Available in the Microsoft Graph Explorer.
- Localization will start to appear over the next few weeks. The first languages will be Czech, Danish, Dutch, French, German, Hungarian, Italian, Japanese, Korean, and Spanish.
Why did we use the security API and connect with Microsoft Intelligent Security Graph?
The Intelligent Security Graph is a unified platform for combatting cyberthreats. It powers real-time threat protection for Microsoft products and services and supports an ecosystem of integrated solutions.
The security API in Microsoft Graph makes it easy to connect with those solutions in the Intelligent Security Graph. It allows you to more readily realize and enrich the value of these solutions.
We see three common business scenarios driving consumption of the Secure Score API through the Microsoft Intelligent Security Graph:
- Monitor, track and report on your configuration baseline and score in downstream reporting tools.
- Integrate the data into compliance or cybersecurity insurance applications.
- Integrate Secure Score data into your SIEM or CASB to drive a hybrid or multi-cloud framework for security analytics.
Getting Started
Acquiring the Secure Score data from the API requires you to setup a few pre-requisites.
First, you should choose your consumption model. If you plan to have a non-user-interactive application to retrieve data from the API, you should opt for the Service-To-Service Authentication model. Reference information about this model is located at https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-protocols-oauth-service-to-service.
If your application will require an administrator to provide their logon credentials each time you pull data from the API, you should opt for the user OAuth model. Reference information about this model is located here. If you are a CSP application developer partner you can also find information here.
Second, you will need to register your application in Azure Active Directory in order to call the API. You need to grant the SecurityEvents.Read.All and SecurityEvents.ReadWrite.All permission scopes. See here for further details.
Now you’re ready to access the API. For more details on how to use it, head over to:
https://developer.microsoft.com/en-us/graph/docs/api-reference/beta/resources/security-api-overview
https://developer.microsoft.com/en-us/graph/docs/api-reference/beta/resources/securescores
We hope you all enjoy the new API and start using it right away. For those of you who are currently using the original API, we recommend that you migrate to the new one before January 31st, 2019 as we will deprecate it at that time.
If you have any questions, thoughts, comments on the new API please share them with us below.
Thanks for continuing to use Microsoft Secure Score!
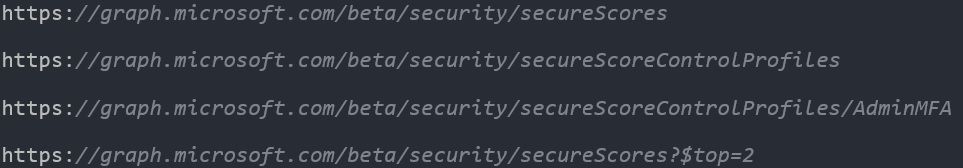
We love that the community has great discussions on Microsoft Secure Score. One of the topics we hear from you and other organizations is on the Secure Score API. This is a great way to programmatically access Secure Score data. Over the past year and a half, we have received a lot of feedback on the API and the Microsoft 365 Security Engineering team is pleased to announce the availability and preview of the new Microsoft 365 Secure Score API.
As part of building the new API we also wanted to provide it in other languages. In doing this work for the API, it also gave us localization of the Secure Score interface. The localization of the interface is starting to roll out.
What’s new?
The new API is based on much of your feedback and has a host of changes to enable new scenarios. At a high level they are:
- Integrated into the Security Graph API, allowing easier permission scoping.
- Support for filtering methods such as $top=2 or explicit control access.
- Dual entities, an entity for bringing back just the score data and an entity for bringing back control metadata such as Title, Descriptions and Threats etc.
- Patch support, allowing you to flag controls as 3rd Party or Ignore.
- New fields, such as “assignedTo” and “tenantNote”.
- Support for delegated admin rights.
- Available in the Microsoft Graph Explorer.
- Localization will start to appear over the next few weeks. The first languages will be Czech, Danish, Dutch, French, German, Hungarian, Italian, Japanese, Korean, and Spanish.
Why did we use the security API and connect with Microsoft Intelligent Security Graph?
The Intelligent Security Graph is a unified platform for combatting cyberthreats. It powers real-time threat protection for Microsoft products and services and supports an ecosystem of integrated solutions.
The security API in Microsoft Graph makes it easy to connect with those solutions in the Intelligent Security Graph. It allows you to more readily realize and enrich the value of these solutions.
We see three common business scenarios driving consumption of the Secure Score API through the Microsoft Intelligent Security Graph:
- Monitor, track and report on your configuration baseline and score in downstream reporting tools.
- Integrate the data into compliance or cybersecurity insurance applications.
- Integrate Secure Score data into your SIEM or CASB to drive a hybrid or multi-cloud framework for security analytics.
Getting Started
Acquiring the Secure Score data from the API requires you to setup a few pre-requisites.
First, you should choose your consumption model. If you plan to have a non-user-interactive application to retrieve data from the API, you should opt for the Service-To-Service Authentication model. Reference information about this model is located at https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-protocols-oauth-service-to-service.
If your application will require an administrator to provide their logon credentials each time you pull data from the API, you should opt for the user OAuth model. Reference information about this model is located here. If you are a CSP application developer partner you can also find information here.
Second, you will need to register your application in Azure Active Directory in order to call the API. You need to grant the SecurityEvents.Read.All and SecurityEvents.ReadWrite.All permission scopes. See here for further details.
Now you’re ready to access the API. For more details on how to use it, head over to:
https://developer.microsoft.com/en-us/graph/docs/api-reference/beta/resources/security-api-overview
https://developer.microsoft.com/en-us/graph/docs/api-reference/beta/resources/securescores
We hope you all enjoy the new API and start using it right away. For those of you who are currently using the original API, we recommend that you migrate to the new one before January 31st, 2019 as we will deprecate it at that time.
If you have any questions, thoughts, comments on the new API please share them with us below.
Thanks for continuing to use Microsoft Secure Score!
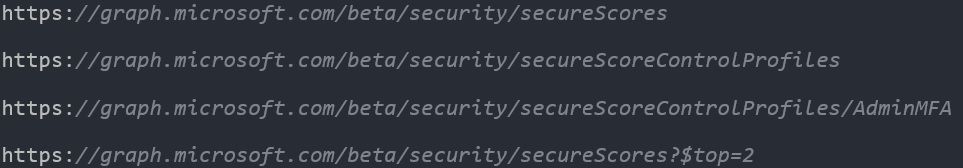
We love that the community has great discussions on Microsoft Secure Score. One of the topics we hear from you and other organizations is on the Secure Score API. This is a great way to programmatically access Secure Score data. Over the past year and a half, we have received a lot of feedback on the API and the Microsoft 365 Security Engineering team is pleased to announce the availability and preview of the new Microsoft 365 Secure Score API.
As part of building the new API we also wanted to provide it in other languages. In doing this work for the API, it also gave us localization of the Secure Score interface. The localization of the interface is starting to roll out.
What’s new?
The new API is based on much of your feedback and has a host of changes to enable new scenarios. At a high level they are:
- Integrated into the Security Graph API, allowing easier permission scoping.
- Support for filtering methods such as $top=2 or explicit control access.
- Dual entities, an entity for bringing back just the score data and an entity for bringing back control metadata such as Title, Descriptions and Threats etc.
- Patch support, allowing you to flag controls as 3rd Party or Ignore.
- New fields, such as “assignedTo” and “tenantNote”.
- Support for delegated admin rights.
- Available in the Microsoft Graph Explorer.
- Localization will start to appear over the next few weeks. The first languages will be Czech, Danish, Dutch, French, German, Hungarian, Italian, Japanese, Korean, and Spanish.
Why did we use the security API and connect with Microsoft Intelligent Security Graph?
The Intelligent Security Graph is a unified platform for combatting cyberthreats. It powers real-time threat protection for Microsoft products and services and supports an ecosystem of integrated solutions.
The security API in Microsoft Graph makes it easy to connect with those solutions in the Intelligent Security Graph. It allows you to more readily realize and enrich the value of these solutions.
We see three common business scenarios driving consumption of the Secure Score API through the Microsoft Intelligent Security Graph:
- Monitor, track and report on your configuration baseline and score in downstream reporting tools.
- Integrate the data into compliance or cybersecurity insurance applications.
- Integrate Secure Score data into your SIEM or CASB to drive a hybrid or multi-cloud framework for security analytics.
Getting Started
Acquiring the Secure Score data from the API requires you to setup a few pre-requisites.
First, you should choose your consumption model. If you plan to have a non-user-interactive application to retrieve data from the API, you should opt for the Service-To-Service Authentication model. Reference information about this model is located at https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-protocols-oauth-service-to-service.
If your application will require an administrator to provide their logon credentials each time you pull data from the API, you should opt for the user OAuth model. Reference information about this model is located here. If you are a CSP application developer partner you can also find information here.
Second, you will need to register your application in Azure Active Directory in order to call the API. You need to grant the SecurityEvents.Read.All and SecurityEvents.ReadWrite.All permission scopes. See here for further details.
Now you’re ready to access the API. For more details on how to use it, head over to:
https://developer.microsoft.com/en-us/graph/docs/api-reference/beta/resources/security-api-overview
https://developer.microsoft.com/en-us/graph/docs/api-reference/beta/resources/securescores
We hope you all enjoy the new API and start using it right away. For those of you who are currently using the original API, we recommend that you migrate to the new one before January 31st, 2019 as we will deprecate it at that time.
If you have any questions, thoughts, comments on the new API please share them with us below.
Thanks for continuing to use Microsoft Secure Score!
We love that the community has great discussions on Microsoft Secure Score. One of the topics we hear from you and other organizations is on the Secure Score API. This is a great way to programmatically access Secure Score data. Over the past year and a half, we have received a lot of feedback on the API and the Microsoft 365 Security Engineering team is pleased to announce the availability and preview of the new Microsoft 365 Secure Score API.
As part of building the new API we also wanted to provide it in other languages. In doing this work for the API, it also gave us localization of the Secure Score interface. The localization of the interface is starting to roll out.
What’s new?
The new API is based on much of your feedback and has a host of changes to enable new scenarios. At a high level they are:
- Integrated into the Security Graph API, allowing easier permission scoping.
- Support for filtering methods such as $top=2 or explicit control access.
- Dual entities, an entity for bringing back just the score data and an entity for bringing back control metadata such as Title, Descriptions and Threats etc.
- Patch support, allowing you to flag controls as 3rd Party or Ignore.
- New fields, such as “assignedTo” and “tenantNote”.
- Support for delegated admin rights.
- Available in the Microsoft Graph Explorer.
- Localization will start to appear over the next few weeks. The first languages will be Czech, Danish, Dutch, French, German, Hungarian, Italian, Japanese, Korean, and Spanish.
Why did we use the security API and connect with Microsoft Intelligent Security Graph?
The Intelligent Security Graph is a unified platform for combatting cyberthreats. It powers real-time threat protection for Microsoft products and services and supports an ecosystem of integrated solutions.
The security API in Microsoft Graph makes it easy to connect with those solutions in the Intelligent Security Graph. It allows you to more readily realize and enrich the value of these solutions.
We see three common business scenarios driving consumption of the Secure Score API through the Microsoft Intelligent Security Graph:
- Monitor, track and report on your configuration baseline and score in downstream reporting tools.
- Integrate the data into compliance or cybersecurity insurance applications.
- Integrate Secure Score data into your SIEM or CASB to drive a hybrid or multi-cloud framework for security analytics.
Getting Started
Acquiring the Secure Score data from the API requires you to setup a few pre-requisites.
First, you should choose your consumption model. If you plan to have a non-user-interactive application to retrieve data from the API, you should opt for the Service-To-Service Authentication model. Reference information about this model is located at https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-protocols-oauth-service-to-service.
If your application will require an administrator to provide their logon credentials each time you pull data from the API, you should opt for the user OAuth model. Reference information about this model is located here. If you are a CSP application developer partner you can also find information here.
Second, you will need to register your application in Azure Active Directory in order to call the API. You need to grant the SecurityEvents.Read.All and SecurityEvents.ReadWrite.All permission scopes. See here for further details.
Now you’re ready to access the API. For more details on how to use it, head over to:
https://developer.microsoft.com/en-us/graph/docs/api-reference/beta/resources/security-api-overview
https://developer.microsoft.com/en-us/graph/docs/api-reference/beta/resources/securescores
We hope you all enjoy the new API and start using it right away. For those of you who are currently using the original API, we recommend that you migrate to the new one before January 31st, 2019 as we will deprecate it at that time.
If you have any questions, thoughts, comments on the new API please share them with us below.
Thanks for continuing to use Microsoft Secure Score!