Last September, we announced new capabilities in Office 365 Message Encryption that enable users to seamlessly collaborate on protected emails with anyone. This release included Do Not Forward an out-of-the-box policy that encrypts emails and Office attachments, and restricts the content and email from being forwarded, printed or copied.
Today, we are happy to share that we are releasing another out-of-the-box policy called encrypt only. With the encrypt-only policy, users can send encrypted email to any recipient, whether they are inside or outside the organization, and the protection follows the lifecycle of the email. That means recipients can copy, print and forward the email, and encryption will not be removed. This new policy provides more flexibility in the type of protection that can be applied to your sensitive emails.
This is valuable for organizations that want persistent encryption, but do not want to add additional restrictions. For example, a doctor looking to protect an email containing sensitive personal information, can apply the encrypt-only policy, and the patient receiving the email can easily consume the protected message regardless of their email provider, and forward that email to another trusted party.
With this new, flexible policy, users and admins can apply different levels of protection to best fit their data protection needs.
Read more to understand what the encrypt-only policy looks like and how to apply the policy.
How the encrypt-only policy works
The encrypt-only policy is an out-of-the box policy that can be used without additional configuration, and as the name suggests, only applies encryption to the email. You can apply the policy through end-user controls in Outlook or through automatic admin managed controls in the Exchange admin center. Users can apply this policy to individual emails through end-user controls in Outlook, and Admins can apply this policy automatically to any email that matches the set criteria through admin-managed controls in the Exchange admin center.
Customers that have enabled the new Office 365 Message Encryption capabilities will see the encrypt-only policy first through Outlook on the web and in the Exchange admin center under mail flow rules. Updates to Outlook for Windows and Outlook for Mac are planned for the coming months.
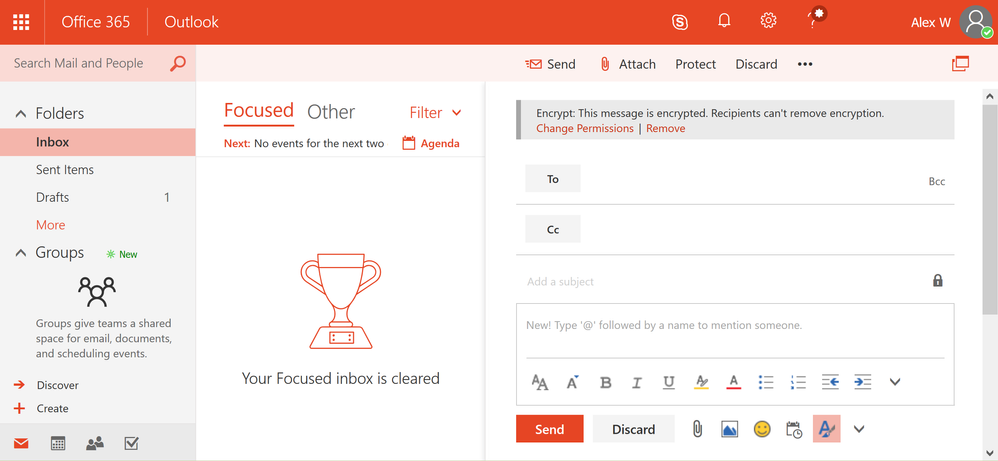
How to send an email with the encrypt-only policy in Outlook on the web
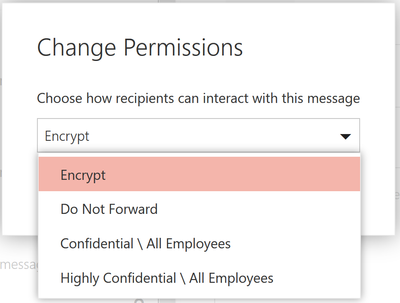
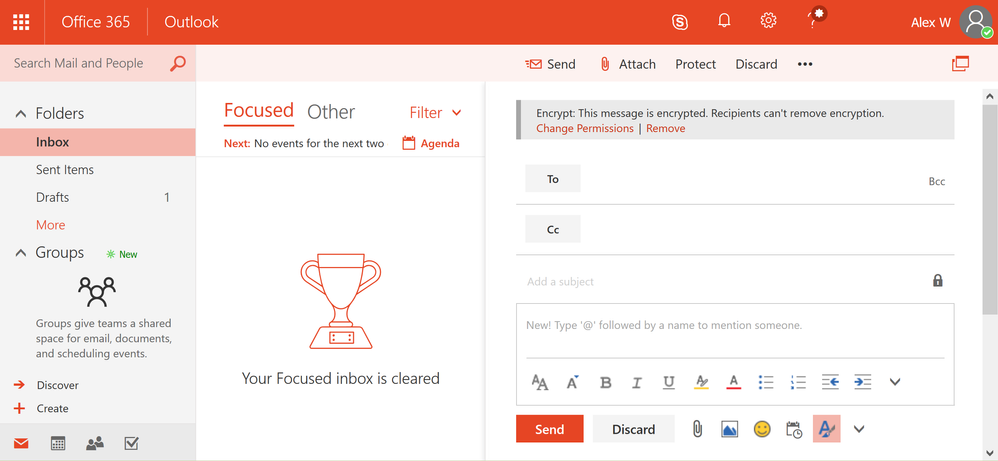
Users can apply protection with the encrypt-only policy by clicking on the protect button and changing the permissions to just encrypt. While the other options encrypt the message, the encrypt option will apply the encrypt-only policy to the message, therefore enabling recipients to forward, copy and print the message.
Applying this option will offer added flexibility for recipients to share the email with other trusted parties while encryption continues to persist and throughout the lifecycle of the email.
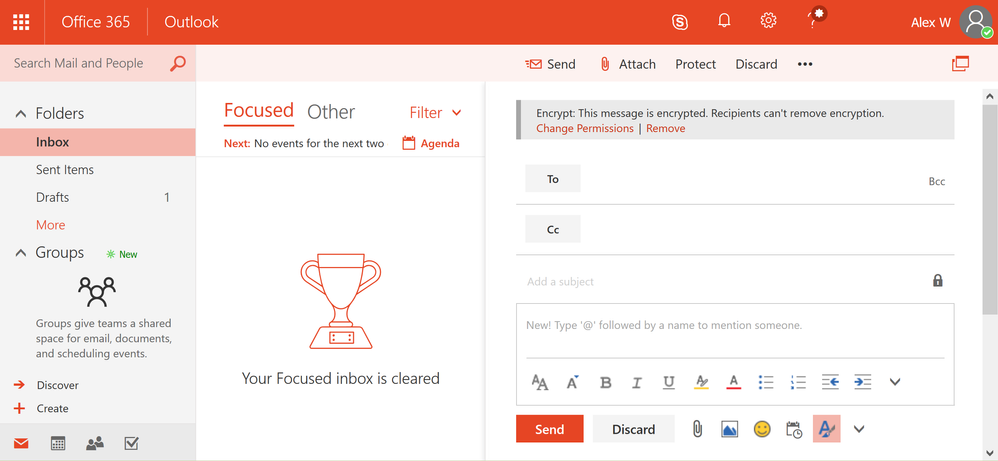
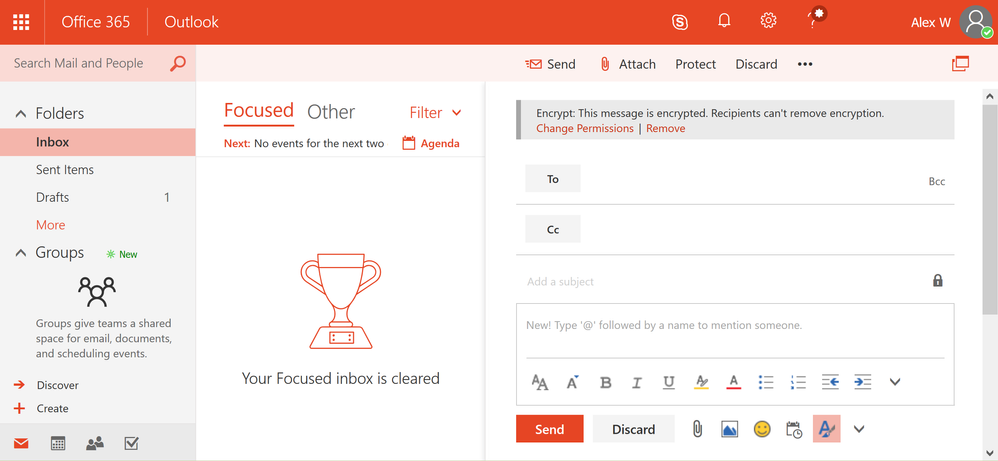
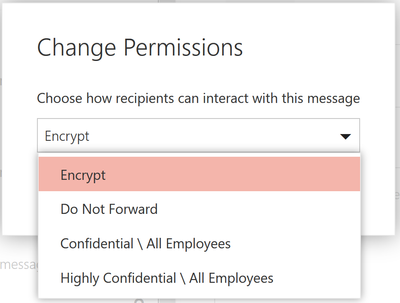 In Outlook on the web, users can click on the protect button to change the permissions of the email. Once a user clicks on protect, the users can click on encrypt, to only encrypt the email.
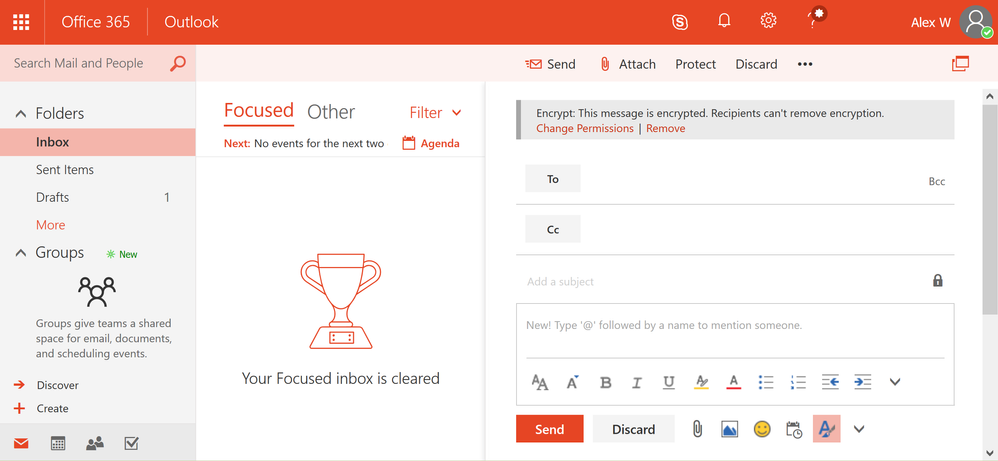
In Outlook on the web, users can click on the protect button to change the permissions of the email. Once a user clicks on protect, the users can click on encrypt, to only encrypt the email. 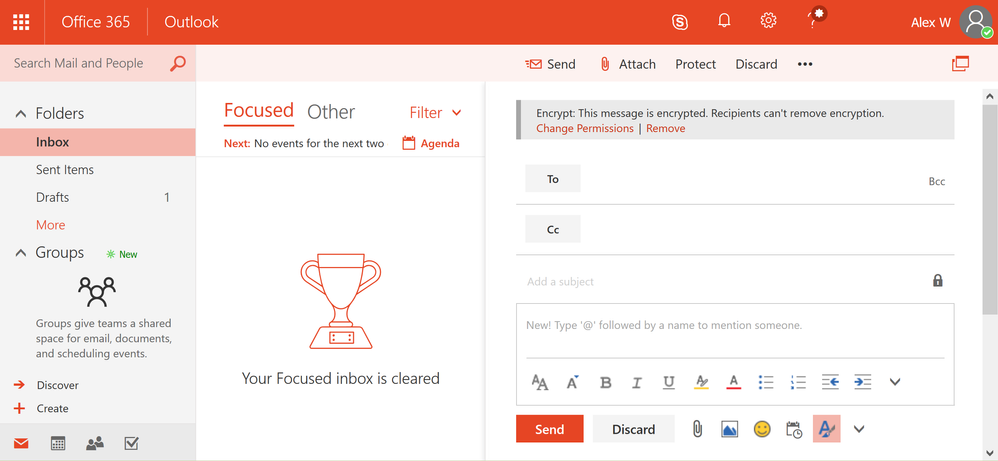 Once the encrypt-only policy is applied, the user will see a notification that encryption has been applied.
Once the encrypt-only policy is applied, the user will see a notification that encryption has been applied.
How to apply the encrypt-only policy through Exchange mail flow rules
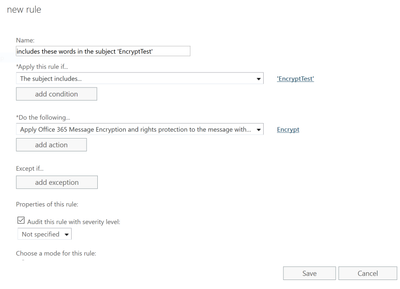
As an administrator, you can apply the encrypt-only policy automatically to emails that meet certain conditions by creating a mail flow rule. When you do this, email affected by the encrypt-only policy is encrypted in transport by Office 365.
For instructions on creating a mail flow rule that employs the encrypt-only policy, see define mail flow rules to encrypt email messages in Office 365.
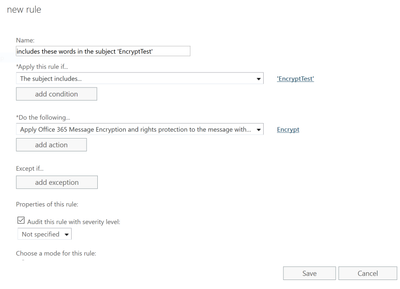 You as an administrator can create new mail flow rule to automatically apply the encrypt-only policy to emails.
You as an administrator can create new mail flow rule to automatically apply the encrypt-only policy to emails.
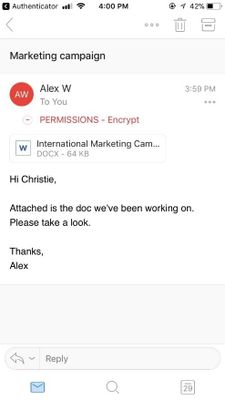
How to read encrypt-only email using Outlook on the web and Outlook mobile
Office 365 recipients can easily read and reply to emails that have been applied with the encrypt-only policy using Outlook on the web and Outlook mobile directly from the client.
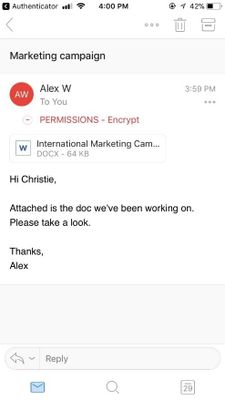 Users can read the encrypted message natively directly in Outlook on the web and Outlook mobile.
Users can read the encrypted message natively directly in Outlook on the web and Outlook mobile.
The inline reading experience for Outlook desktop (Windows and Mac) will be available in the coming months. In the meantime, Office 365 users using Outlook desktop will see the encrypted mail as an html mail with an rpmsg_v2 attachment.
How to read encrypt-only emails for non-Office 365 users (on-prem, Gmail, and Outlook.com users)
Non-Office 365 users, receive an html mail with an rpmsg_v4 attachment. Once they click Read Message they are redirected to the Office 365 Message Encryption portal where they can reply, forward, print, or take other allowed actions. More information can be found in this article.
Get started!
The new encrypt-only policy rolls out starting today as part of Office 365 Message Encryption.
Office 365 Message Encryption is offered in Office 365 E3 and E5, or as an add-on -you can find the full list of where Office 365 Message Encryption is offered here.
Please let us know what you think here or give us your feedback on uservoice!
Last September, we announced new capabilities in Office 365 Message Encryption that enable users to seamlessly collaborate on protected emails with anyone. This release included Do Not Forward an out-of-the-box policy that encrypts emails and Office attachments, and restricts the content and email from being forwarded, printed or copied.
Today, we are happy to share that we are releasing another out-of-the-box policy called encrypt only. With the encrypt-only policy, users can send encrypted email to any recipient, whether they are inside or outside the organization, and the protection follows the lifecycle of the email. That means recipients can copy, print and forward the email, and encryption will not be removed. This new policy provides more flexibility in the type of protection that can be applied to your sensitive emails.
This is valuable for organizations that want persistent encryption, but do not want to add additional restrictions. For example, a doctor looking to protect an email containing sensitive personal information, can apply the encrypt-only policy, and the patient receiving the email can easily consume the protected message regardless of their email provider, and forward that email to another trusted party.
With this new, flexible policy, users and admins can apply different levels of protection to best fit their data protection needs.
Read more to understand what the encrypt-only policy looks like and how to apply the policy.
How the encrypt-only policy works
The encrypt-only policy is an out-of-the box policy that can be used without additional configuration, and as the name suggests, only applies encryption to the email. You can apply the policy through end-user controls in Outlook or through automatic admin managed controls in the Exchange admin center. Users can apply this policy to individual emails through end-user controls in Outlook, and Admins can apply this policy automatically to any email that matches the set criteria through admin-managed controls in the Exchange admin center.
Customers that have enabled the new Office 365 Message Encryption capabilities will see the encrypt-only policy first through Outlook on the web and in the Exchange admin center under mail flow rules. Updates to Outlook for Windows and Outlook for Mac are planned for the coming months.
How to send an email with the encrypt-only policy in Outlook on the web
Users can apply protection with the encrypt-only policy by clicking on the protect button and changing the permissions to just encrypt. While the other options encrypt the message, the encrypt option will apply the encrypt-only policy to the message, therefore enabling recipients to forward, copy and print the message.
Applying this option will offer added flexibility for recipients to share the email with other trusted parties while encryption continues to persist and throughout the lifecycle of the email.
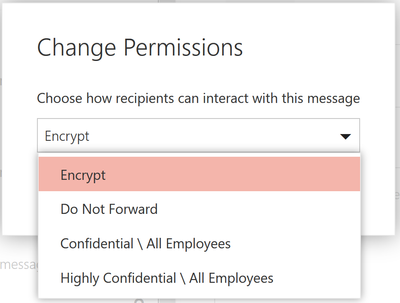 In Outlook on the web, users can click on the protect button to change the permissions of the email. Once a user clicks on protect, the users can click on encrypt, to only encrypt the email.
In Outlook on the web, users can click on the protect button to change the permissions of the email. Once a user clicks on protect, the users can click on encrypt, to only encrypt the email. 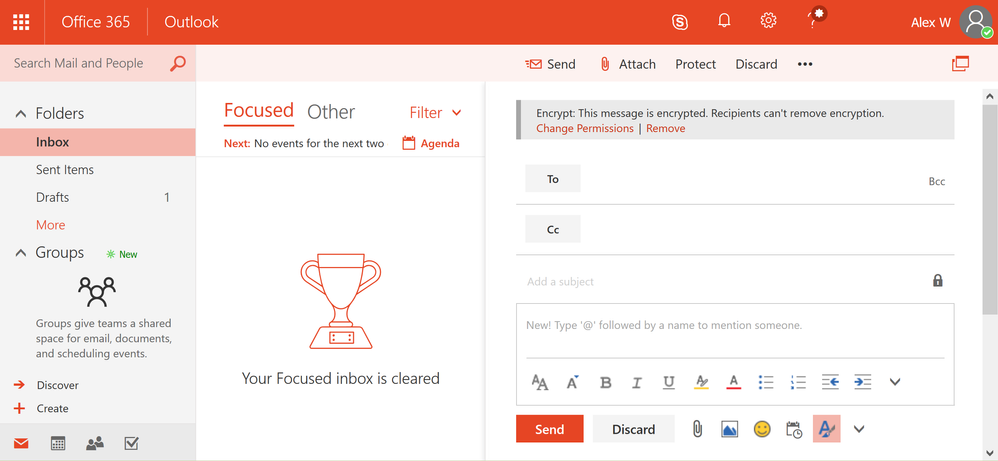 Once the encrypt-only policy is applied, the user will see a notification that encryption has been applied.
Once the encrypt-only policy is applied, the user will see a notification that encryption has been applied.
How to apply the encrypt-only policy through Exchange mail flow rules
As an administrator, you can apply the encrypt-only policy automatically to emails that meet certain conditions by creating a mail flow rule. When you do this, email affected by the encrypt-only policy is encrypted in transport by Office 365.
For instructions on creating a mail flow rule that employs the encrypt-only policy, see define mail flow rules to encrypt email messages in Office 365.
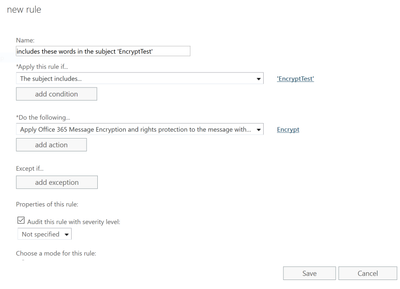 You as an administrator can create new mail flow rule to automatically apply the encrypt-only policy to emails.
You as an administrator can create new mail flow rule to automatically apply the encrypt-only policy to emails.
How to read encrypt-only email using Outlook on the web and Outlook mobile
Office 365 recipients can easily read and reply to emails that have been applied with the encrypt-only policy using Outlook on the web and Outlook mobile directly from the client.
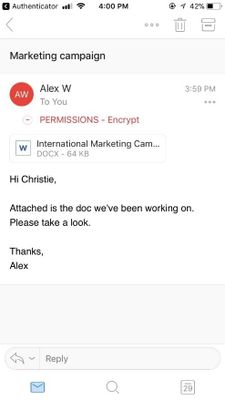 Users can read the encrypted message natively directly in Outlook on the web and Outlook mobile.
Users can read the encrypted message natively directly in Outlook on the web and Outlook mobile.
The inline reading experience for Outlook desktop (Windows and Mac) will be available in the coming months. In the meantime, Office 365 users using Outlook desktop will see the encrypted mail as an html mail with an rpmsg_v2 attachment.
How to read encrypt-only emails for non-Office 365 users (on-prem, Gmail, and Outlook.com users)
Non-Office 365 users, receive an html mail with an rpmsg_v4 attachment. Once they click Read Message they are redirected to the Office 365 Message Encryption portal where they can reply, forward, print, or take other allowed actions. More information can be found in this article.
Get started!
The new encrypt-only policy rolls out starting today as part of Office 365 Message Encryption.
Office 365 Message Encryption is offered in Office 365 E3 and E5, or as an add-on -you can find the full list of where Office 365 Message Encryption is offered here.
Please let us know what you think here or give us your feedback on uservoice!
Last September, we announced new capabilities in Office 365 Message Encryption that enable users to seamlessly collaborate on protected emails with anyone. This release included Do Not Forward an out-of-the-box policy that encrypts emails and Office attachments, and restricts the content and email from being forwarded, printed or copied.
Today, we are happy to share that we are releasing another out-of-the-box policy called encrypt only. With the encrypt-only policy, users can send encrypted email to any recipient, whether they are inside or outside the organization, and the protection follows the lifecycle of the email. That means recipients can copy, print and forward the email, and encryption will not be removed. This new policy provides more flexibility in the type of protection that can be applied to your sensitive emails.
This is valuable for organizations that want persistent encryption, but do not want to add additional restrictions. For example, a doctor looking to protect an email containing sensitive personal information, can apply the encrypt-only policy, and the patient receiving the email can easily consume the protected message regardless of their email provider, and forward that email to another trusted party.
With this new, flexible policy, users and admins can apply different levels of protection to best fit their data protection needs.
Read more to understand what the encrypt-only policy looks like and how to apply the policy.
How the encrypt-only policy works
The encrypt-only policy is an out-of-the box policy that can be used without additional configuration, and as the name suggests, only applies encryption to the email. You can apply the policy through end-user controls in Outlook or through automatic admin managed controls in the Exchange admin center. Users can apply this policy to individual emails through end-user controls in Outlook, and Admins can apply this policy automatically to any email that matches the set criteria through admin-managed controls in the Exchange admin center.
Customers that have enabled the new Office 365 Message Encryption capabilities will see the encrypt-only policy first through Outlook on the web and in the Exchange admin center under mail flow rules. Updates to Outlook for Windows and Outlook for Mac are planned for the coming months.
How to send an email with the encrypt-only policy in Outlook on the web
Users can apply protection with the encrypt-only policy by clicking on the protect button and changing the permissions to just encrypt. While the other options encrypt the message, the encrypt option will apply the encrypt-only policy to the message, therefore enabling recipients to forward, copy and print the message.
Applying this option will offer added flexibility for recipients to share the email with other trusted parties while encryption continues to persist and throughout the lifecycle of the email.
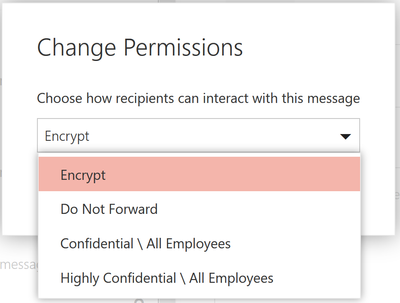 In Outlook on the web, users can click on the protect button to change the permissions of the email. Once a user clicks on protect, the users can click on encrypt, to only encrypt the email.
In Outlook on the web, users can click on the protect button to change the permissions of the email. Once a user clicks on protect, the users can click on encrypt, to only encrypt the email. 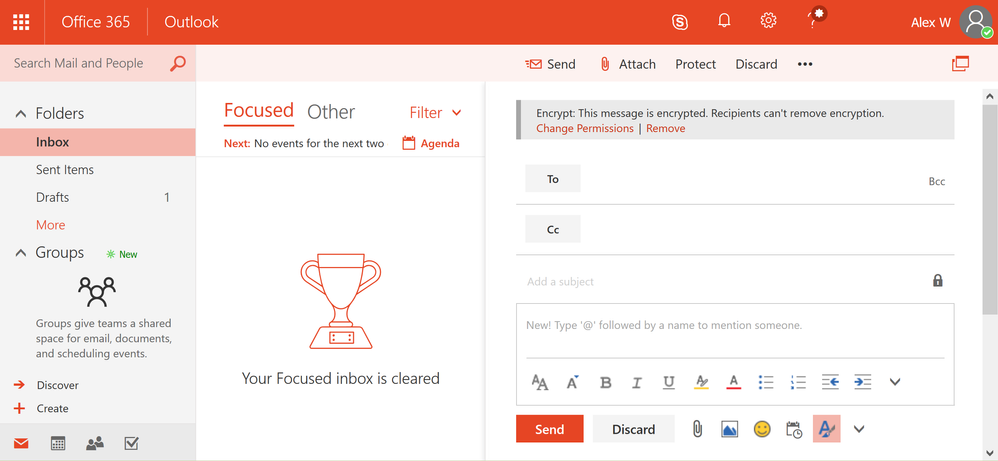 Once the encrypt-only policy is applied, the user will see a notification that encryption has been applied.
Once the encrypt-only policy is applied, the user will see a notification that encryption has been applied.
How to apply the encrypt-only policy through Exchange mail flow rules
As an administrator, you can apply the encrypt-only policy automatically to emails that meet certain conditions by creating a mail flow rule. When you do this, email affected by the encrypt-only policy is encrypted in transport by Office 365.
For instructions on creating a mail flow rule that employs the encrypt-only policy, see define mail flow rules to encrypt email messages in Office 365.
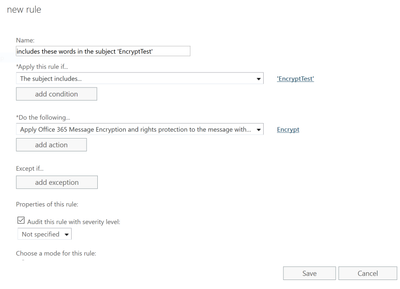 You as an administrator can create new mail flow rule to automatically apply the encrypt-only policy to emails.
You as an administrator can create new mail flow rule to automatically apply the encrypt-only policy to emails.
How to read encrypt-only email using Outlook on the web and Outlook mobile
Office 365 recipients can easily read and reply to emails that have been applied with the encrypt-only policy using Outlook on the web and Outlook mobile directly from the client.
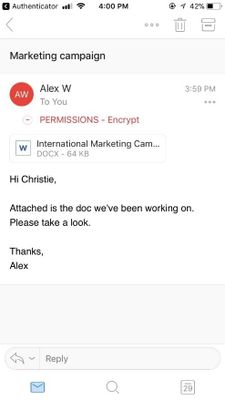 Users can read the encrypted message natively directly in Outlook on the web and Outlook mobile.
Users can read the encrypted message natively directly in Outlook on the web and Outlook mobile.
The inline reading experience for Outlook desktop (Windows and Mac) will be available in the coming months. In the meantime, Office 365 users using Outlook desktop will see the encrypted mail as an html mail with an rpmsg_v2 attachment.
How to read encrypt-only emails for non-Office 365 users (on-prem, Gmail, and Outlook.com users)
Non-Office 365 users, receive an html mail with an rpmsg_v4 attachment. Once they click Read Message they are redirected to the Office 365 Message Encryption portal where they can reply, forward, print, or take other allowed actions. More information can be found in this article.
Get started!
The new encrypt-only policy rolls out starting today as part of Office 365 Message Encryption.
Office 365 Message Encryption is offered in Office 365 E3 and E5, or as an add-on -you can find the full list of where Office 365 Message Encryption is offered here.
Please let us know what you think here or give us your feedback on uservoice!

Oh yes, I love automation. Having a mountain of robots, and building them (especially my DR Who full sized dalek), fascinates me in the wonder how invented things can move without human intervention (except I suppose the dalek because I will be driving it – haha).
There are various products which all elude to automation in my arena of Microsoft Office systems and services. And now that they are being brought all together under the Office365 hood, now is the time to understand the nature of Service Delivery and Automation.
This quick article is my take on what it is from my standpoint giving some arguments as to what it means from a basic viewpoint. Note that this view is one I have had for many years, because the model, and my notion, stems all the way back to my Systems Analysis days.
Ahem, a little check first… Automation and associated service delivery has been around in systems since the age of software. It is not new. Unfortunately, by many, it is an art which is glossed over, and as such, when someone says ‘lets automate process using powershell’ that’s only a small link in chain mail armour. But now, we have entered the realm of convergence, the advent of ‘connected’ systems. This means automation takes an evolved step, into the land of systems with software beyond human reach, beyond scripting, beyond coding, beyond one platform (e.g. SharePoint), beyond Office365, into and beyond cloud services, to the nether regions of connected systems and connected data. The fact that more data is available to be accessed which can then be scrutinized, re-modeled and then used to automate other processes makes this an exciting time in the land of software design. The fact that time-to-live for the company process becomes shorter, the re-use and revamp of automation becomes an enterprise imperative, and the need for a complete ‘coded’ approach is not the answer. Also, the following video gives even more reasons why automation and service delivery are becoming more important.
Why Service Delivery and Automation is important
As a younger lad, having been introduced to Systems Analysis and Design (which includes programming in a multitude of computer languages using a multitude of platforms and technologies), as I see that as time marches on with new technologies, so does the increased need to maintain and therefore automate, endpoints of legacy with endpoints to current with endpoints of the ‘external’. Critically, and in every solution devised, there is service delivery. The absolute imperative to ensure that whatever solution being devised is maintainable, available, repeatable by design and resilient. This resiliency is not just to do with things like Disaster Recovery or Business Continuity, it goes right to the heart of making sure that the solution is fit for purpose. Service Delivery flows through every part of enterprise architecture, from the idea, to analysis, to design, to production, to support and thrives within that solutions and connected solutions lifecycles. It includes the physical and digital technology that makes up the solution – yes, the servers, and the software, and the storage etc. That means, that even more crucially, it does not matter whether you are a business analyst, a programmer, an administrator, an engineer, a product manager or programme manager. You will be thinking service delivery in whatever you do, whether you like it or not. As you may know, my site is a haven to all things service delivery and includes another passion of mine, which is automation. Why? Because automation is the connector that allows the solution to be flexible, to scale, to morph, to carry out processes without human intervention (which then means better accuracy) – it supports service delivery. Of course, I don’t aim to create a wonderful robot of automation to win a prize, but am absolutely keen to learn and use my integration expertise with it!  Anyway, lets go back to why you should understand the importance of service delivery automation. For example, lets quickly mention Office 365 as an example. Any administrative process that you are carrying out when interacting with the admin centre of Office365 carries out a robotic process. A robotic process is one where you interact with the product, and yet, the back end product is not wholly under your control. Rather, you are automating the software to carry out functions, as opposed to you directly influencing the software. You do not have access to any server based tools – you are automating those tools to carry out a process, in fact, you are being non-invasive – that’s robotic automation. Robotic automation also includes things like system upgrade, data entry and transactional processing. And the high chances are that you will not have direct access to those systems in a multi-departmental organisation. Robotic automation is definitely coming on leaps and bounds in a multi-server environment where you need information from a collection of systems. I spoke to a company which has a desire to manage specific services wanting to not only control web services on a particular group of pre-production servers, but also wanted to store results securely online because they had support groups which did not have access to those servers.
Anyway, lets go back to why you should understand the importance of service delivery automation. For example, lets quickly mention Office 365 as an example. Any administrative process that you are carrying out when interacting with the admin centre of Office365 carries out a robotic process. A robotic process is one where you interact with the product, and yet, the back end product is not wholly under your control. Rather, you are automating the software to carry out functions, as opposed to you directly influencing the software. You do not have access to any server based tools – you are automating those tools to carry out a process, in fact, you are being non-invasive – that’s robotic automation. Robotic automation also includes things like system upgrade, data entry and transactional processing. And the high chances are that you will not have direct access to those systems in a multi-departmental organisation. Robotic automation is definitely coming on leaps and bounds in a multi-server environment where you need information from a collection of systems. I spoke to a company which has a desire to manage specific services wanting to not only control web services on a particular group of pre-production servers, but also wanted to store results securely online because they had support groups which did not have access to those servers.
Automation comes with a price
But automation carries with it a price. The increase in automation has a detrimental affect on wisdom, that is, it will curtail the ability to continually review an already automated created process. Reasoning is that once something has been automated, it is then difficult and/or cumbersome, and therefore not desirable (particularly for large automated processes), to alter that process, without then impacting on other processes connected to it. Take for example the process to automatically upload data into SharePoint which then automatically stamps metadata on that data. Lets assume for a moment that it starts off as simple as this:
- Get a file from a network share
- Upload that file into a SharePoint document library
- Set metadata, the Title becomes the filename
Sounds simple? Yes, until you add a simple automation with that file, like:
- Once the file has been uploaded, alert the members
- Gather details from the file to pass onto a data management system
For alerting, sounds simple because you would simply set an e-mail alert, yes? But it is not so simple if that alert needs to be customised beyond what SharePoint does, or if the alert needs to trigger some other process, like having its contents interrogated to be used in another system. And as for the data being passed onto a data management system, that means additional management of ensuring the right data gets across. Then there’s the service delivery angle, ensuring that the automative process continues to be maintainable, available, resilient and supportable. So that means, either code it, or use say a workflow to customise a notification that fires as soon as the file is added and carry out other functions. The point is this. Once something becomes a target for automation, the human desire to do more with it comes arises, but that impacts on wisdom because the need to change things does not happen at the same speed as when the process came into action. This speed decreases with every new connection to systems and other processes, because of amount of work required to identify and service deliver all steps in the process end-to-end. This affects wisdom, as the sheer added number of steps in a process make it more cumbersome to confirm things like performance, audit, human response tracking, etc. Of course, one may argue that certain workflow tools tracks performance in each step. But that rarely comes from a central point – that generally comes from the application system running that step. If are able to centralise all processes under one system banner, then maybe, well done! But, I am not talking about just one tool. I am talking about automation that does not just include that tool working in one system, but all the other systems that tool may be a part of in an automative process (that is, all endpoints).
Automation is not just writing an app to display a form or a workflow
In essence, automation is one of the keys in which systems work in harmony to fuel a seemlessly connected process, machine driven and harvesting intelligence. Service delivery automation encompasses all parts of a process that requires automation in order to meet one or more of the imperatives at the bottom of this section. It is more than simply the need for someone to fill in a form (that is simply an aspect of a process).
For example, if HR wants an individual to fill in a form online once they are on-boarded, that form must be sent to specific individuals, then to other departments to assign resources, then needs to be stored, and needs to be applicable to audit (or used again when that new person changes departments or even leaves the company). So writing an app to get someone to fill in a form is not automation of a process, it is a step in that process. Another example. You want to be able to collect information on the status of all servers in your estate – specifically, the status of specific services and want to display that centrally. You don’t have access to SCOM (System Center Operations Manager), and you don’t want to code it. Again, writing an app to display the status of all the services is not automation of that process, it is a step in that process, because automation of display of that information does not end with it simple being displayed. You want to be able to act on the data, or take some automated action to resolve issues if the status is not as expected.

Automation using any technology is decided upon because one needs to address all of the following, but only works if by connecting technologies using automation techniques minimises disruption:
- Quality
- Speed
- Accuracy
- Productivity
- Efficiency
- Scaleability
- Flexibility
Don’t automate everything!
Just because you have a bicycle does not mean you fix it so it rides itself. By doing that you miss the simple enjoyment of doing anything physical, like exercising your legs. The same thing comes with automation. Just because you want to cut costs to achieve additional benefits by reducing or eliminating human involvement doesn’t mean you should immediately automate the process. A factory which distributes milk has automated the entire factory floor so that robots move the milk containers around the factory. But they still need humans to keep an eye on the robots. Certain processes you will want to be operated by humans, because at the very least you will still maintain some modicum of control, and to mitigate risk. Otherwise, you might as well consign yourself as a cyborg or a member of the Borg from Star Trek. You only automate things that you think will reduce time around time, or will reduce the requirement to chase actions. But improving things to simply reduce headcount is not going to solve anything, unless you can absolutely guarantee that nothing will happen to upset the automated process. Some companies where automation has been a success is were they actively introduce business continuity. I’ve even seen companies use a back to paper continuity plan if the automated process through computers fail. This is where, for example, they utilise legacy equipment and where they need to guarantee a process if that legacy equipment fails.
Conclusion – and a new beginning?
If you are not thinking automation for your technology set, you should be. I think that it is time to take stock of your automation alternatives. Automation of an enterprise solution using multiple technologies requires an adoption of an suite that allows you flexibility. Remember that using a tool within one platform is not enough. Maintainability, Availability, Resiliency and Supportability is key. Automation in the SharePoint space is already taking place, is driven by transactional processes across systems, to ring-fenced workflow against specific processes, to Web Analytics across Office365 and on-premise SharePoint. As this increases, so will be the need to review automation tools. On my voyage of discovery, a few of the companies I have surveyed taking automation seriously have mentioned to be a product called Automate 10, owned by HelpSystems LLC. This product provides a none scripting platform to integrate and automate a myriad of services from Amazon through to FTP through to WMI automation and across multiple servers and services in the enterprise. Am running some demos of this myself and the product seems to be very useful. Check out some automation case-studies from some products which I recommend if you are considering enterprise wide automation (not sticking to one technology or one sticking to one scripting language). Click the below screenshot to see the number of services (note – Azure is also listed!).  There are other links to articles you should also check out, to see how some other organisations are dealing with automation.
There are other links to articles you should also check out, to see how some other organisations are dealing with automation.

When utilising a collaboration tool the key productivity rationale is to automate processes through the content stored within that collaboration tool. SharePoint has a number of platform flavours (on-premise, hybrid, online) and has integration points which is only limited by creativity it seems (not simply confined to Microsoft products). Therefore, it is crucial that when thinking of what workflow tool should be used to automated business process that you understand also the options, strengths, weaknesses of the various workflow options that can be utilised with SharePoint.
Having had a lot of fun trying to fathom, making mistakes along the way of course, I got together all my notes, including querying lots of knowledgeable people (thanks to you all) – and put together an article; published on Tech Net blogs and also on DOCS!
The article is quite large therefore I had it split into four parts (great idea from Charlotte C at Microsoft – thanks)
Sections in Part 1 are:
1: Introduction to the business process automated
2: What does a workflow system need to accomplish
3: Mind set of developing workflow
4: Types of workflow
5: What does the full article cover in terms of product, scope
Link: http://blogs.technet.com/b/uktechnet/archive/2014/12/10/part-1-sharepoint-workflow-service-delivery-options.aspx
Sections in Part 2 are:
1: Options for workflow with on-premise SharePoint
2: Options for developing custom workflows using SharePoint Designer / Microsoft Visual Studio
Link: http://blogs.technet.com/b/uktechnet/archive/2014/12/18/sharepoint-workflow-service-delivery-options-part-2.aspx
Sections in Part 3 are:
1: Options for workflow in SharePoint Online through Office365
2: Options for workflow in hybrid situations
3: The ‘workflow manager’
4: Publishing workflows to Azure
5: Workflow options available through third parties
6: Strengths and weaknesses of covering all options
Link: http://blogs.technet.com/b/uktechnet/archive/2015/01/19/sharepoint-workflow-service-delivery-options-part-3.aspx
Part four completes the article by summarising the key take-away – what tasks should be carried out concerning an approach to choosing the workflow solution that suits you and the customer
Link: http://blogs.technet.com/b/uktechnet/archive/2015/01/26/sharepoint-workflow_3a00_-service-delivery-options-_2d00_-part-4.aspx
Happy reading!
General Availability of Microsoft Graph reporting APIs for retrieving Office 365 product usage data
The usage reports in the Office 365 admin center enable admins to understand their company’s usage across the Office 365 services. However, many of you have existing reporting solutions such as a company reporting application or a web portal in place. To assure that you can monitor your IT services in one unified location, the usage reporting APIs complement the usage reports and allow organizations and independent software vendors to incorporate Office 365 usage data into their existing reporting solutions. Using these APIs, you can retrieve the data available in all of the usage reports, including organization level summaries per service, entity level (user, sites, accounts) usage information for reporting periods of the last 7/30/90/180 days, and daily activity aggregates.
Get started with the new APIs
The new APIs are available now, and any user with global admin, product admin rights (for Exchange, Skype for Business and SharePoint), or a reports reader role can retrieve data through these APIs.
You can leverage the Microsoft Graph documentation for the reporting API and submit feature requests by asking or voting on an idea on UserVoice. Please submit questions by posting them on Stack Overflow and tagging microsoftgraph.
With this announcement, we are announcing the deprecation of the following APIs within the Office 365 Reporting Web Service: ConnectionbyClientType, ConnectionbyClientTypeDetail, CsActiveUser, CsAVConferenceTime, CsP2PAVTime, CsConference, CsP2PSession, GroupActivity, MailboxActivity, GroupActivity, MailboxUsage, MailboxUsageDetail, StaleMailbox and StaleMailboxDetail.
We will remove these APIs, as well as any related PowerShell cmdlets, on January 29, 2018.
If you are currently using APIs or any of the related PowerShell cmdlets from the Office 365 Reporting Web Service, please start planning the migration of any subsystems within your organization.
Below is a summary of the APIs and cmdlets that will be deprecated.
|
Office 365 Reporting web service
reference page
|
Office 365 reporting-related
Windows PowerShell cmdlets
|
Description
|
MS Graph Replacement
|
|
CsActiveUser* reports
|
Get-CsAVConferenceTimeReport
|
The number of active, logged-in Lync Online users during the reporting period
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/skype_for_business_activity_reports
|
|
CsAVConferenceTime* reports
|
Get-CsActiveUserReport
|
The amount of time logged-in organization users participated in Lync Online conferences during the reporting period
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/skype_for_business_organizer_activity_reports
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/skype_for_business_participant_activity_reports
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/skype_for_business_peer_to_peer_activity
|
|
CsP2PAVTime* reports
|
Get-CsP2PAVTimeReport
|
|
|
Get-CsClientDeviceReport
|
View statistics about the client devices that connected to Skype for Business Online in your cloud-based organization.
|
These methods are being deprecated as of January 29, 2018. They are being replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/skype_for_business_device_usage_reports
|
|
Get-CsClientDeviceDetailReport
|
View statistics about the number of peer-to-peer sessions and conferences by users and devices that connected to Skype for Business Online in your cloud-based organization.
|
|
CsConference* reports
|
Get-CsConferenceReport
|
The count of Lync Online conferences and peer-to-peer sessions during the reporting period.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
Â
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/skype_for_business_organizer_activity_reports
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/skype_for_business_participant_activity_reports
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/skype_for_business_peer_to_peer_activity
|
|
CsP2PSession* reports
|
Get-CsP2PSessionReport
|
|
|
Get-CsUserActivitiesReport
|
View number and type of activities that a user participated in while connected to Skype for Business Online in your cloud-based organization.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getskypeforbusinessactivityuserdetail
|
|
|
Get-CsUsersBlockedReport
|
View Skype for Business Online users who have been blocked due to fraudulent call activities.
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-CsPSTNConferenceTimeReport
|
Show the number of minutes that Skype for Business Online users spent in dial-in or dial-out conferences.
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-CsPSTNUsageDetailReport
|
View public switched telephone network (PSTN) usage details for Skype for Business Online users.
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
ConnectionbyClientType* reports
|
Get-ConnectionByClientTypeReport
|
The number and types of email client-access methods used by the organization’s users during the reporting period. For example, Outlook Web Access, Exchange Web services, and so on.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/email_app_usage_reports
|
|
ConnectionbyClientTypeDetail* reports
|
Get-ConnectionByClientTypeDetailReport
|
|
MailboxActivity* reports
GroupActivity* reports
|
Get-MailboxActivityReport
Get-GroupActivityReport
|
Office 365 users created and deleted, summarized over the indicated time periods. Active Directory Domain Services (AD DS) replication can sometimes delay this information up to a day.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/mailbox_usage_reports
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/office_365_groups_activity_reports
|
|
|
Get-ExternalActivityByDomainReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-ExternalActivityByUserReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-ExternalActivityReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-ExternalActivitySummaryReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-LicenseVsUsageSummaryReport
|
To retrieve a report that identifies the number of active users for installed software licenses (workloads).
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
MailboxUsage report
|
Get-MailboxUsageReport
|
Summary and detailed statistics about organization user mailboxes.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/mailbox_usage_reports
|
|
MailboxUsageDetail report
|
Get-MailboxUsageDetailReport
|
|
MailDetail report
|
Get-MailDetailReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailDetailDlpPolicy report
|
Get-MailDetailDlpPolicyReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailDetailMalware report
|
Get-MailDetailMalwareReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailDetailSpam report
|
Get-MailDetailSpamReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailDetailTransportRule report
|
Get-MailDetailTransportRuleReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailFilterList report
|
Get-MailFilterListReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailTraffic report
|
Get-MailTrafficReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailTrafficPolicy report
|
Get-MailTrafficPolicyReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailTrafficSummary reports
|
Get-MailTrafficSummaryReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MailTrafficTop report
|
Get-MailTrafficTopReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MessageTrace report
|
Get-MessageTrace
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MessageTraceDetail report
|
Get-MessageTraceDetail
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
MxRecordReport report
|
Get-MxRecordReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
| |
Get-O365ClientOSReport
|
Get a summary report of client operating system use.
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-O365ClientOSDetailReport
|
Get a detailed report of client operating system use.
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-O365ClientBrowserReport
|
Get a summary report of client browser use.
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-O365ClientBrowserDetailReport
|
Get a detailed report of client browser use.
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
OutboundConnectorReport report
|
Get-OutboundConnectorReport
|
|
This method will continue to work as expected and is not impacted by this deprecation.
|
|
|
Get-PartnerClientExpiringSubscriptionReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-PartnerCustomerUserReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-ScorecardClientDeviceReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-ScorecardClientOSReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-ScorecardClientOutlookReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
|
Get-ScorecardMetricsReport
|
|
This method is being deprecated as of January 29, 2018. There is no MS Graph replacement.
|
|
ServiceDeliveryReport report
|
Get-ServiceDeliveryReport
|
|
This method will continue to work as expected and is not impacted by this deprecation
|
|
|
Get-SPOActiveUserReport
|
View statistics about Microsoft SharePoint Online users in your cloud-based organization.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getsharepointactivityusercounts
|
|
|
Get-SPOOneDriveForBusinessFileActivityReport
|
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getonedriveactivityfilecounts
|
|
|
Get-SPOOneDriveForBusinessUserStatisticsReport
|
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getonedriveactivityusercounts
|
|
|
Get-SPOSkyDriveProDeployedReport
|
View the number of My Site sites in your cloud-based organization.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getonedriveactivityusercounts
|
|
|
Get-SPOSkyDriveProStorageReport
|
View statistics about the space taken up (in MB) by My Sites in your cloud-based organization.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getonedriveusagestorage
|
|
|
Get-SPOTeamSiteDeployedReport
|
View the number of My Site sites in your cloud-based organization.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getsharepointsiteusagestorage
|
|
|
Get-SPOTeamSiteStorageReport
|
View statistics about the space taken up (in MB) by team sites in your cloud-based organization.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getsharepointsiteusagestorage
|
|
|
Get-SPOTenantStorageMetricReport
|
View statistics about the space taken up (in MB) by all sites in for your cloud-based organization.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/api/reportroot_getsharepointsiteusagestorage
|
|
StaleMailbox report
|
Get-StaleMailboxReport
|
The details and summary counts of mailboxes that have not been accessed within the indicated time period.
|
This method is being deprecated as of January 29, 2018. It is replaced by the new MS Graph Reporting API available at
https://developer.microsoft.com/en-us/graph/docs/api-reference/v1.0/resources/email_activity_reports
|
|
StaleMailboxDetail report
|
Get-StaleMailboxDetailReport
|
As the use of content management systems evolve with users adding more, ahem, “content”, the organizations accountable for those content systems will need to ensure that they build in people resources who can manage that content, and particularly people who can find insights in that content for the benefit of the organization.
Business intelligence requirements and implementations are growing faster than ever before, particularly due to the rise of cloud computing and more cloud services. There is now much more pressure on ensuring that customer interactions are tracked as a key aspect of business intelligence data gathering. This is one of the most critically important ways of working out the value that cloud services provide.
The blog article has been written for TechNet and is available on this link.
Protecting your data against file corruption , data loss, and malicious intent is a top priority for Microsoft, and an integral part of the Office 365 service. Our approach to data protection goes beyond high availability and disaster recovery scenarios. Resiliency and recoverability are built into the service.
Even if a traditional backup solution provides recovery options to address file corruption, deletion, and malicious attacks, it won’t necessarily help you recover quickly from such incidents. Research shows that it can take months to detect the presence of an attacker an organization’s network. Given this, a backup and restore solution could be a potential area of attack, and could further broaden the scope of attack into your disaster recovery environment. Additionally, all backup data would need to be throuroughly cleansed before it could be leveraged as a viable restore option. Gartner predicts that by 2020, 30% of organizations targeted by major cyberattacks will spend more than two months cleansing backup systems and data, resulting in delayed recoveries.[i]
With this in mind, Office 365 has moved beyond the backup and restore solutions that were first established in on-premises environments. Microsoft invests deeply in providing a holistic in-place solution that both keeps multiple copies of your data across multiple locations, and enables you to develop upfront policies for prevention and detection. These policies can be enforced manually and automatically at multiple levels of granularity, including via intelligent location-based classification, patterns, or sensitive types of content.
In addition to the inherent versioning and recycling capabilities provided by applications like Exchange, SharePoint, and OneDrive, Office 365 provides comprehensive solutions to help keep your data safe from both human error as well as malicious attacks:
- Data Loss Prevention helps customers to identify, monitor and protect sensitive data through deep content analysis.
- Exchange Online Protection provides robust email protection against spam, known viruses and malware.
- Advanced Threat Protection extends Exchange Online Protection by safeguarding your Office 365 environment (email, Word, Excel, Powerpoint, SharePoint, OneDrive, and Teams) from today’s most sophisticated unknown threats leveraging behavioral analysis and machine learning techniques to mitigate malicious content. ATP also provides real time, time-of-click protection against malicious URLs, and rich reporting and tracking capabilities, so you can gain critical insights into who is being targeted in your organization and the category, volume, and frequency of attacks you are facing.
- Threat Intelligence provides interactive tools to analyze prevalence and severity of threats in near real-time, real-time and customizable threat alert notifications, and remediation capabilities for suspicious content.
- Auditing helps monitor and investigate actions taken on your data, intelligently identify risks, contain and respond to threats, and protect valuable intellectual property.
- Advanced Data Governance provides smart policy recommendations and automatic data classifications that allow you to take actions on data- such as retention and deletion -throughout its lifecycle. Built-in and custom alerts help you identify data governance risks like unusual volumes of file deletion.
The multiple built-in security capabilities of Office 365 in combination with the above services and controls help ensure your data is protected in-place and incidents like file corruption, deletion, and malicious intent are minimized at all times.
More information:
[i] From Gartner Foundational Research: Prepare for and Respond to a Business Disruption After an Aggressive Cyberattack, ID: G00275607
Today we are announcing a preview of the Office Customization Tool for Click-to-Run, a simple to use web application that enables desktop administrators to customize Office 365 clients.
Until today, Windows desktop administrators would use notepad or an equivalent text editor to compile various XML statements to define the Office edition, feature update frequency, version, language and other number of available settings. This somewhat tedious task, in most cases, would result in installation errors from fouled up manual entries or copy-and-paste actions into the text editor.
With the new Office Customization Tool, desktop admins can leverage the rich user interface that intuitively shows all available options to build the desired Office configurations. The configuration tool groups the commonly used settings in the following categories:
- software & language
- installation & update
- licensing & display
Each of these areas provide admins with options to help meet their security and regulatory needs.
One of our favorite additions, is the configuration builder. Desktop admins can quickly see a list of all configuration settings being chosen on the right-hand side of the screen, giving the desktop admin a quick and easy way to see the result of their selections without jumping through multiple screens.
When all the desired settings have been selected, desktop admins are provided with the option to download the resulting configuration.xml file which is to be used in conjunction with the Office Deployment Tool for the settings to take affect during installation time of the Office 365 client.
Desktop Admin also have an option to upload any previously configured XML files to the configuration tool and modify them with new or existing settings.
For those of you who are familiar with the old Win32 Office Customization Tool which came with your perpetual (MS Installer) bits, you’ll notice the new customization tool has a lack of install-time user preferences. Over the next several months we will be enhancing the tool to enable desktop admins to select many configurable user preferences that are currently being offered with the perpetual counterpart. We encourage you to try out the new Office Customization Tool which is available in preview today, by clicking on the link or typing http://config.office.com in your browser. Send us feedback and let us know what you think by using the send a smile feature, located on the top right of the web application.
Amesh Mansukhani
Senior Program Manager – Office Engineering
![Rethinking the modern workplace with Microsoft 365]()

Today’s post was written by Catherine Boeger, general manager for Microsoft Office marketing
Today the rapid pace of change is challenging businesses and government organizations to rethink everything we do. What’s changing? For the first time ever, we have five generations in the workforce, from Baby Boomers to Generation Z, all with different ideas about how work gets done and different levels of comfort and expectations around technology. Constantly changing customer and citizen expectations are pushing businesses to innovate quickly and find new ways to leverage information from both inside and outside organizations. And ever-growing cyber security threats remind us we must remain vigilant in protecting our employees and customer data and in maintaining regulatory and industry compliance. One of the primary questions is, how can you embrace these modern workplace trends to help drive business growth? I want to share some of the ways Microsoft 365, which brings together Office 365, Windows 10, and Enterprise Security + Mobility, can help organizations like yours leverage digital transformation to enable people to come together in a secure way and get the best results from each other to drive business forward.
Let’s first look at the generational shift in the workplace. With five generations of workers on the payroll, how can you create a connected environment to leverage that diversity, which can be so critical for your success? At Microsoft, we’ve found that teamwork is key—bringing together groups of people, no matter their generation, function, or location, to address problems and opportunities with a shared sense of accountability to complete the task in front of them. That’s why we built Microsoft Teams in Microsoft 365: to help you create a digital hub for teamwork where everyone can easily share or access information they need and focus on a common goal. Powerful features like threaded persistent chats and access to recorded meetings can help create an ongoing dialog and enable people to learn from each other and get caught up quickly. And while we all may have a habit of thinking that mobility is more important to Millennials or younger generations, really the need and desire to be productive from anywhere has become a reality of all our lives, which is why Teams is accessible from almost any device.
Generational diversity isn’t the only gap we can bridge to help drive business growth. We’re building tools for the modern workplace that close longstanding technology gaps that separate employees from data, resources and expertise they need to do their best work. We believe a truly modern workplace can empower everyone in the organization to turn ideas into action – from the executive team to the Firstline Workforce.
Firstline Workers are often the first to engage customers, the first to represent a company’s brand and first to see products and services in action. They are the people behind the counter, on the phone, in the clinics, on shop floor and in the field. Their unique perspective provides the on-the-ground facts that help organizations spot trends, challenges and best practices. We see organizations take advantage of this firstline perspective every day to unlock innovation and growth. I’m reminded of a Microsoft customer, Fruit of the Loom, who recognized that “their greatest thinkers are within the company,” according to their Chief Operating Officer, Tony Pelaski. Fruit of the Loom is using Microsoft 365 Enterprise to connect the entire organization and foster an engaged workforce with the capabilities and tools to deliver against customer insights, market trends, and new ideas. Customer stories like these inspired us to create a version of Microsoft 365 specifically for your Firstline Workforce. We know that all organizations have critical data, and I believe it will be those that take advantage of their firstline data and empower all workers that will achieve a true and sustainable competitive advantage.
Of course, any data you collect must be secured. Today we all face constant pressure to have open flows of information to drive productivity and teamwork, and it’s as critical as ever to protect our organizations because threats today are complex and target everyone. Cyber threats have grown so pervasive that 74 percent of organizations expect to be hacked in the next year.[1] That’s why Microsoft built security into all layers of Microsoft 365, powered by the Microsoft Intelligent Security Graph, to help you detect threats and protect your people, data, and devices without disrupting employee productivity. Customers like the UK Ministry of Defence have felt confident in shifting to the Microsoft cloud because capabilities like Office 365 Advanced Threat Protection and Customer Lockbox help provide the security and privacy controls they need to protect sensitive data.
And on top of security, we all worry about how best to maintain compliance and data privacy, because no doing so can stop any organization—no matter how innovative—in its tracks. Microsoft works closely with regulators and customers to ensure that our services are compliant with global, regional, and industry regulations. Microsoft 365 provides advanced compliance functionality to help adhere to these regulations, including General Data Protection Regulation, also known as GDPR. Microsoft 365 is ready for May 25, 2018 – the day when GDPR takes effect, and can help you accelerate your compliance journey.
As a keynote speaker at the upcoming Microsoft Tech Summit Toronto December 13 and 14, I’ll be talking in depth about how Microsoft 365 can help you create a modern workplace that brings people together in secure ways to innovate new products and services. I hope you’ll join me and Arpan Shah, general manager of Azure Infrastructure marketing at Microsoft, to discover the latest trends, tools, and product roadmaps designed to help you thrive in a new world of work.
[1] http://www.isaca.org/cyber/Documents/State-of-Cybersecurity-infographic.pdf